 CrowdStrike was working on behalf of the DNC, the company was also under contract with the FBI for unspecified technical services. According to a US federal government spending database, CrowdStrike’s “period of performance” on behalf of the FBI was between July 2015 and July 2016. CrowdStrike’s findings regarding the DNC server breach — which continue to this day to be cited as authoritative by everyone from former FBI Director James Comey, to NBC anchor Megyn Kelly — were issued in June 2016, when the contract was still active. source
CrowdStrike was working on behalf of the DNC, the company was also under contract with the FBI for unspecified technical services. According to a US federal government spending database, CrowdStrike’s “period of performance” on behalf of the FBI was between July 2015 and July 2016. CrowdStrike’s findings regarding the DNC server breach — which continue to this day to be cited as authoritative by everyone from former FBI Director James Comey, to NBC anchor Megyn Kelly — were issued in June 2016, when the contract was still active. source
Some may believe this is all old news. It maybe years old, however it is remains unsolved. With a new Biden administration, it is important that many, many of those old players are now part of the Biden presidential operation, especially Susan Rice and the others that did unmasking. Beware of what comes.
Meanwhile…..when governments collude…especially intelligence agencies and operatives….
Real Clear Politics published in May of 2020 the following:
CrowdStrike, the cyber-security firm that first accused Russia of hacking Democratic Party emails and served as a critical source for U.S. intelligence officials in the years-long Trump-Russia probe, privately acknowledged more than two years ago that it had no evidence that Russian hackers stole emails from the Democratic National Committee’s server.
CrowdStrike President Shawn Henry’s admission under oath, in a recently declassified December 2017 interview before the House Intelligence Committee, raises new questions about whether Special Counsel Robert Mueller, intelligence officials and Democrats misled the public. The allegation that Russia stole Democratic Party emails from Hillary Clinton, John Podesta and others and then passed them to WikiLeaks helped trigger the FBI’s probe into now debunked claims of a conspiracy between the Trump campaign and Russia to steal the 2016 election. The CrowdStrike admissions were released just two months after the Justice Department retreated from its its other central claim that Russia meddled in the 2016 election when it dropped charges against Russian troll farms it said had been trying to get Trump elected.
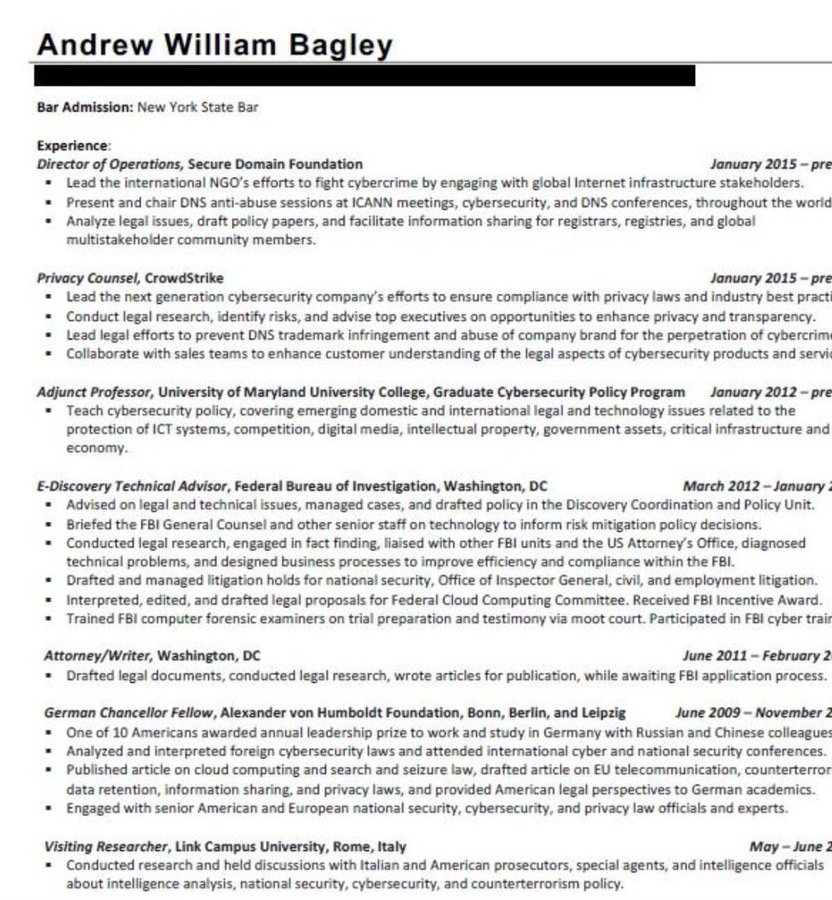
And the Crowdstrike CEO is proud of the work his company does with the FBI. Going back further, it is noted: Attorney Andrew Bagley has been employed by the cybersecurity firm CrowdStrike since January 2015; this company was involved deeply in the Democratic National Committee (DNC) hacking debacle. In 2010, Bagley served as a visiting researcher at the Link Campus University in Rome; while there, his résumé notes that Bagley, “Conducted research and held discussions with Italian and American prosecutors, special agents, and intelligence officials about intelligence analysis, national security, cybersecurity, and counterterrorism policy.”
According to Bagley’s online résumé, he served as the E-Discovery Technical Advisor to the FBI, conducting legal research, advising on technical issues, and drafting policy for the Discovery Coordination and Policy Unit within the FBI, from 2012 to 2015.
In its capacity as attorney for the DNC, Perkins Coie – through another of its partners, Michael Sussman – is also the law firm that retained CrowdStrike, the cyber security outfit, upon learning in April 2016 that the DNC’s servers had been hacked.
Interesting: Despite the patent importance of the physical server system to the FBI and Intelligence-Community investigation of Russian meddling in the 2016 election, the Bureau never examined the DNC servers. Evidently, the DNC declined to cooperate to that degree, and the Obama Justice Department decided not to issue a subpoena to demand that the servers be turned over (just like the Obama Justice Department decided not to issue subpoenas to demand the surrender of critical physical evidence in the Clinton e-mails investigation).
Instead, the conclusion that Russia is responsible for the invasion of the DNC servers rests on the forensic analysis conducted by CrowdStrike. Rather than do its own investigation, the FBI relied on a contractor retained by the DNC’s lawyers.
 Link University, Rome
Link University, Rome
As Senator Lindsey Graham published the now declassified documents/testimonies on RussiaGate, CrowdStrike comes into view again. Why? Well, the FBI has a long and comprehensive history with the Link Campus in Rome and now we learn more about Joseph Mifsud. He was on staff at the Link Campus in Italy. Remember how, AG Barr flew to Italy for some one on one interviews? Those he interviewed remain unknown.Could AG Barr have met with Vincenzo Scotti or maybe even Mifsud himself? As for Link Campus University, Italy: Mifsud, Scotti, and Frattini were all employed by this Italian university. ‘Enzo’ Scotti is Scotti is an Italian politician and member of Christian Democracy. He was Minister of the Interior and Minister of Foreign Affairs. And it could be that Mifsud is hiding in Russia….just a suggestion.
As intelligence expert Chris Blackburn notes on Twitter, leafing through the minutes, “the FBI knew that Joseph Mifsud was working with Italian intelligence figures-trainers at the Link Campus in Rome. Because the FBI worked there, too. Of course Mueller didn’t want to include it in his report.” Nothing but “Russian agent”, then. As RealClearInvestigations points out, after Mifsud was identified as the man who would talk to Papadopoulos, Mueller’s team described him as someone with important Russian contacts. This description of the Maltese lecturer, however, ignored Mifsud’s own ties to Western governments, politicians and institutions, including the CIA, FBI and British intelligence services. It’s really curious that, despite Mifsud’s central role in the investigation, the FBI conducted only a brief interview with him in an atrium of a Washington, D.C., hotel in February 2017. Mueller’s team later claimed that Mifsud provided false statements to FBI agents but did not charge him as happened with Papadopoulos. How could he be a Russian agent? And if he did, why wasn’t he questioned?
Then there is CrowdStrike and Ukraine, or is there?
FILE – CrowdStrike co-founder and CTO Dmitri Alperovitch speaks during the Reuters Media and Technology Summit in New York, June 11, 2012.
After CrowdStrike released its Ukraine report, company co-founder Dmitri Alperovitch claimed it provided added evidence of Russian election interference. In both hacks, he said, the company found malware used by “Fancy Bear,” a group with ties to Russian intelligence agencies.
CrowdStrike’s claims of heavy Ukrainian artillery losses were widely circulated in U.S. media.
On Thursday, CrowdStrike walked back key parts of its Ukraine report.
The company removed language that said Ukraine’s artillery lost 80 percent of the Soviet-era D-30 howitzers, which used aiming software that purportedly was hacked. Instead, the revised report cites figures of 15 to 20 percent losses in combat operations, attributing the figures to IISS.
The original CrowdStrike report was dated Dec. 22, 2016, and the updated report was dated March 23, 2017.
The company also removed language saying Ukraine’s howitzers suffered “the highest percentage of loss of any … artillery pieces in Ukraine’s arsenal.”
***
Just a few months ago, in fact June of 2020, CrowdStrike on their website apparently felt compelled to put forth the following detail for reasons that may be coming clear.
June 5, 2020 UPDATE
Blog update following the release of the testimony by Shawn Henry, CSO and President of CrowdStrike Services, before the House Intelligence Committee that was recently declassified.
What was CrowdStrike’s role in investigating the hack of the DNC?
CrowdStrike was contacted on April 30, 2016 to respond to a suspected breach. We began our work with the DNC on May 1, 2016, collecting intelligence and analyzing the breach. After conducting this analysis and identifying the adversaries on the network, on June 10, 2016 we initiated a coordinated remediation event to ensure the intruders were removed and could not regain access. That remediation process lasted approximately 2-3 days and was completed on June 13, 2016.
Why did the DNC contact CrowdStrike?
The DNC contacted CrowdStrike to respond to a suspected cyber attack impacting its network. The DNC was first alerted to the hack by the FBI in September 2015. According to testimony by DNC IT contractor Yared Tamene Wolde-Yohannes, the FBI attributed the breach to the Russian Government in September 2015 (page 7).
Why did the DNC hire CrowdStrike instead of just working with the FBI to investigate the hack?
The FBI doesn’t perform incident response or network remediation services when organizations need to get back to business after a breach.
CrowdStrike is a leader in protecting customers around the world from cyber threats. It is common for organizations to hire third-party industry experts, like CrowdStrike, to investigate and remediate cyber attacks when they suspect a breach even if they are collaborating with law enforcement. As John Carlin, former Assistant Attorney General for the National Security Division at The Department of Justice, testified before the House Intelligence Committee (cited from page 21 of his testimony):
“A lot of — outside of any political organization, companies, most corporations, they often would use these third party contractors, who they hired through their own counsel, and maximize the control from the point of view of the victim.”
What the heck is going on here for real? Outside of this little website of mine, is anyone else going deeper and seeking truths when it comes to CrowdStrike, Perkins Coie, Link University and the FBI…much less the all things DNC?
Other key citations for reference include:
https://www.voanews.com/usa/cyber-firm-rewrites-part-disputed-russian-hacking-report
https://www.nationalreview.com/corner/scandals-collide-dossier-dnc-server-perkins-coie/
https://www.torial.com/satoshi.nakamoto/portfolio/355396

Pingback: What Is It With CrowdStrike? – Trevor Loudon's New Zeal Blog
Pingback: What is it with CrowdStrike? | NoisyRoom.net