FNC: The Justice Department on Monday announced the indictment of six military hackers with the Russian GRU who allegedly carried out a global conspiracy that included cyberattacks around the world.
The alleged attacks hit targets in Ukraine, the 2018 Winter Olympics in South Korea, and western Pennsylvania.
“No country has weaponized its cyber-capabilities as maliciously and irresponsibly as Russia,” Assistant Attorney General John C. Demers said at a DOJ press conference.
The defendants are six current and former members of GRU, Russia’s military intelligence service. The DOJ said the attacks began in November 2015 and continued until at least October 2019. The allegations do not include any interference in U.S. elections.
The alleged attacks include malware strikes against the Ukrainian power grid, Ministry of Finance, and State Treasury Service; spearphishing campaigns and attacks against French President Emmanuel Macron’s political party, local French governments, and French politicians before their 2017 elections; the global NotPetya malware attack that infected computer worldwide including those in medical facilities in western Pennsylvania and a large American pharmaceutical company; the Olympic Destroyer attack that targeted computers supporting the 2018 Olympics; a spearphishing campaign targeting South Korean officials and citizens, as well as Olympic athletes; another spearphishing campaign against the United Kingdom’s Defence Science and Technology Laboratory, and attacks targeting government entities and companies in Georgia.
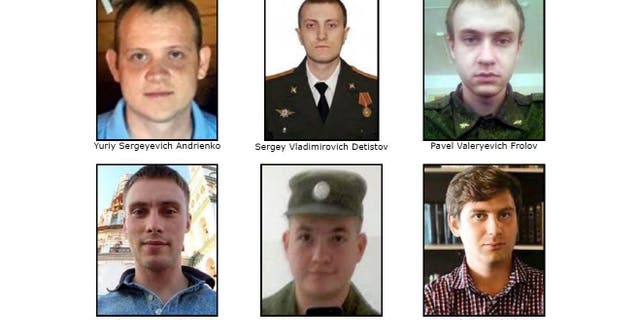
(Source: FBI)
The NotPetya attack alone allegedly resulted in nearly $1 billion in losses, the DOJ said.
The Olympic attacks allegedly came after Russian athletes were banned from competing under the Russia flag due to their country’s government-sponsored doping efforts. The defendants – Yuriy Sergeyevich Andrienko, Sergey Vladimirovich , Pavel Valeryevich Frolov, Anatoliy Sergeyevich Kovalev, Artem Valeryevich Ochichenko and Petr Nikolayevich Pliskin – are charged with conspiracy, computer hacking, wire fraud, aggravated identity theft and false registration of a domain name.
“The crimes committed by these defendants,” said Western District of Pennsylvania U.S. Attorney Scott Brady, “are truly breathtaking in their scope, scale, and impact.”
The Justice Department thanked tech companies including Google, Facebook and Twitter for assisting them in their investigation, but did not explain how they helped.
***
In part from the Justice Department: These GRU hackers and their co-conspirators engaged in computer intrusions and attacks intended to support Russian government efforts to undermine, retaliate against, or otherwise destabilize: (1) Ukraine; (2) Georgia; (3) elections in France; (4) efforts to hold Russia accountable for its use of a weapons-grade nerve agent, Novichok, on foreign soil; and (5) the 2018 PyeongChang Winter Olympic Games after Russian athletes were banned from participating under their nation’s flag, as a consequence of Russian government-sponsored doping effort.
Their computer attacks used some of the world’s most destructive malware to date, including: KillDisk and Industroyer, which each caused blackouts in Ukraine; NotPetya, which caused nearly $1 billion in losses to the three victims identified in the indictment alone; and Olympic Destroyer, which disrupted thousands of computers used to support the 2018 PyeongChang Winter Olympics. The indictment charges the defendants with conspiracy, computer hacking, wire fraud, aggravated identity theft, and false registration of a domain name.
According to the indictment, beginning in or around November 2015 and continuing until at least in or around October 2019, the defendants and their co-conspirators deployed destructive malware and took other disruptive actions, for the strategic benefit of Russia, through unauthorized access to victim computers (hacking). As alleged, the conspiracy was responsible for the following destructive, disruptive, or otherwise destabilizing computer intrusions and attacks:
- Ukrainian Government & Critical Infrastructure: December 2015 through December 2016 destructive malware attacks against Ukraine’s electric power grid, Ministry of Finance, and State Treasury Service, using malware known as BlackEnergy, Industroyer, and KillDisk;
- French Elections: April and May 2017 spearphishing campaigns and related hack-and-leak efforts targeting French President Macron’s “La République En Marche!” (En Marche!) political party, French politicians, and local French governments prior to the 2017 French elections;
- Worldwide Businesses and Critical Infrastructure (NotPetya): June 27, 2017 destructive malware attacks that infected computers worldwide using malware known as NotPetya, including hospitals and other medical facilities in the Heritage Valley Health System (Heritage Valley) in the Western District of Pennsylvania; a FedEx Corporation subsidiary, TNT Express B.V.; and a large U.S. pharmaceutical manufacturer, which together suffered nearly $1 billion in losses from the attacks;
- PyeongChang Winter Olympics Hosts, Participants, Partners, and Attendees: December 2017 through February 2018 spearphishing campaigns and malicious mobile applications targeting South Korean citizens and officials, Olympic athletes, partners, and visitors, and International Olympic Committee (IOC) officials;
- PyeongChang Winter Olympics IT Systems (Olympic Destroyer): December 2017 through February 2018 intrusions into computers supporting the 2018 PyeongChang Winter Olympic Games, which culminated in the Feb. 9, 2018, destructive malware attack against the opening ceremony, using malware known as Olympic Destroyer;
- Novichok Poisoning Investigations: April 2018 spearphishing campaigns targeting investigations by the Organisation for the Prohibition of Chemical Weapons (OPCW) and the United Kingdom’s Defence Science and Technology Laboratory (DSTL) into the nerve agent poisoning of Sergei Skripal, his daughter, and several U.K. citizens; and
- Georgian Companies and Government Entities: a 2018 spearphishing campaign targeting a major media company, 2019 efforts to compromise the network of Parliament, and a wide-ranging website defacement campaign in 2019.
Cybersecurity researchers have tracked the Conspirators and their malicious activity using the labels “Sandworm Team,” “Telebots,” “Voodoo Bear,” and “Iron Viking.”
