Few appear to remember the brazen, corruption and deceptive operation when pro-Russian separatists invaded Crimea. The world was in shock and now Ukraine is falling victim to the same operation as NATO fights against this.
If you want to understand the Russian operation in Eastern Europe and how the Kremlin game is played, one must begin with the twisting of information, news and propaganda.
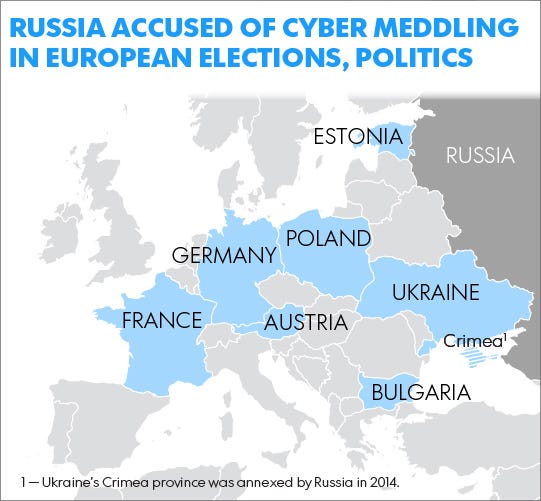
Much has been debated as to the penetration of Russia into the U.S. election system. This is not a new phenomenon for the Kremlin.
The survival of Ukraine as a sovereign, democratic nation was at stake. And the presidential election needed to go smoothly—thus making it a prime target for a Russian cyberattack.
Four days prior to the election, on May 21, 2014, a pro-Russian hacktivist group called CyberBerkut launched a cyberattack against Ukraine’s Central Election Commission computers. According to Ukrainian news reports, the attack destroyed both hardware and software, and for 20 hours shut down programs to monitor voter turnout and tally votes.
On election day, 12 minutes before polls closed, CyberBerkut hackers posted false election results to the election commission’s website. Russia’s TV Channel One promptly aired the bogus results. More here.
An in depth report on ‘disinformation actions by the Kremlin is found below.
The Dynamics of Russia’s Information Activities against Ukraine during the Syria Campaign
The Top Spy Who Is Fighting Corruption in Ukraine
Newsweek: Ukraine’s former top security official has gone from tracking down Russian spies to fighting what he perceives to be the country’s greatest threat—corruption.
“The question is, are we going to survive or not?” Valentyn Nalyvaichenko told The Daily Signal from his offices in Kiev, Ukraine’s capital.
Nalyvaichenko, 50, is the former head of the Security Service of Ukraine, or SBU, which is Ukraine’s successor agency to the Ukrainian Soviet Socialist Republic’s branch of the KGB, the Soviet Union’s main security agency.
“At stake is survival of the country,” Nalyvaichenko said. “At stake is whether we’ll finally get rule of law and a functioning state instead of chaos, corruption, weakness and [being] not capable to defend our territory and the country. So, at stake is the country, its independence.”
During his interview with The Daily Signal, Nalyvaichenko wore a well-appointed suit and tie. He spoke fluent English, evidence of his university degree in linguistics.
His affable demeanor and emotive manner of talking hinted more at his background as a diplomat and member of parliament than his years in charge of Ukraine’s successor agency to the KGB.
Nalyvaichenko led the SBU for the first time from 2006 to 2010. He took over the security agency for a second time on Feb. 24, 2014, two days after deposed former Ukrainian President Viktor Yanukovych fled to Russia in the closing days of the revolution.
Nalyvaichenko has also served as a member of parliament and as Ukraine’s deputy minister of foreign affairs.
Nalyvaichenko’s 2015 departure from the SBU was controversial. In June 2015, while the security agency was investigating high-level Ukrainian officials for financial crimes, Ukrainian President Petro Poroshenko sacked Nalyvaichenko from his leadership post at the SBU.
Today, Nalyvaichenko is the leader of two upstart anti-corruption political platforms: the Justice Civil-Political Movement, and the Nalyvaichenko Anti-Corruption Movement.
“Our people, our common people, are suffering because of corruption, corruption at the top,” Nalyvaichenko said, pounding his fist on the table for emphasis.
“I really like what [Winston] Churchill said in the Second World War,” Nalyvaichenko said. “‘If you’re going through hell, keep going.’ If we’re corrupt, it doesn’t mean we have to say, ‘OK, we’re a failed state.’ No, it’s not true.”
Purge
True to his diplomatic roots, Nalyvaichenko recently traveled to Washington to present evidence to Congress about Russia’s involvement in the war in eastern Ukraine and to press for U.S. assistance in anti-corruption efforts.
As part of his anti-corruption platform, Nalyvaichenko has called for the FBI to investigate the financial crimes of Ukraine’s current and former political leaders.
He also wants U.S. and EU prosecutors to oversee the adjudication of corruption investigations, and for the U.S. to press Ukrainian officials to make Ukraine’s newly minted National Anti-Corruption Bureau independent from the executive and judicial branches.
Nalyvaichenko said Ukraine has a chance to “show for the whole world, especially to the Russian people, that there is an opportunity, there is a plan B, to such nations after the Soviet Union time to be democratic, to be not corrupt, to live in a not corrupt state, to be independent.”
“Ukraine belongs to the Western world,” he added.
Nalyvaichenko added that Ukraine has “several months, two or three months” to show real progress in anti-corruption measures before Western partners begin to break ranks on measures such as maintaining punitive sanctions against Russia.
“It will be no tolerance from the new administration in the United States,” Nalyvaichenko said. And next year, “there might be many changes in the European Union,” he said. “That’s, I think, what is at stake when we’re talking about the European Union and the United States.”
Within Ukraine, Nalyvaichenko’s strategy is to reach out to civil society leaders working at the grassroots level. He wants to convince Ukrainians to believe in the democratic process, despite a quarter-century of oligarchic thug rule after the fall of the Soviet Union.
To that end, Nalyvaichenko’s two anti-corruption organizations—which comprise 10,000 activists across Ukraine—have provided pro bono legal assistance to more than 3,000 Ukrainian citizens involved in court cases against allegedly corrupt government officials.
Nalyvaichenko’s groups have also given free medical care to more than 9,000 civilians in the war zone.
“If you would like to stop Russian aggression, if you would like to get back not only territories but people…we have to show them what?” Nalyvaichenko said. “Believe me, not Kalashnikovs and not tanks. We have to show them a better life.”
Lifestyle
That better life has not yet materialized for many Ukrainians.
For one, the hryvnia, Ukraine’s national currency, is currently less than one-third its value against the dollar than it was before the revolution. Wages have not concurrently risen to match the falling currency, dramatically reducing Ukrainians’ spending power.
Also, corruption still taints almost every aspect of Ukrainian life. University students in Kiev, as an example, say it’s still common practice to pay their professors a bribe to pass exams.
Related: Nolan Peterson: Brothers in arms on the Ukraine front line
According to an October 2016 public opinion poll conducted by the International Republican Institute, and funded by the government of Canada, 30 percent of Ukrainians surveyed who had visited a doctor in the previous 12 months said they paid a bribe for service.
Among those who interacted with the police, 25 percent said they paid a bribe.
A large part of Ukraine’s economy is off the books—what Ukrainians refer to as the “shadow economy.” Ukraine’s Economic Development and Trade Ministry said the shadow economy was 40 percent of the country’s gross domestic product in 2015.
This black market economy robs the government of valuable tax revenue. It also leaves many returning combat veterans, many of whom were drafted, no legal recourse to recover their jobs at the conclusion of their military service.
Many veterans previously worked off the books and were paid in cash so their employers could skirt payroll taxes.
According to the 2016 International Republican Institute study, 72 percent of Ukrainians surveyed said the country was moving in the wrong direction, while 11 percent said the country was on the right track.
As a point of comparison, a year prior to the revolution in May 2013, 69 percent of Ukrainians surveyed said the country was moving in the wrong direction, and 15 percent said the country was moving in the right direction.
According to the same poll, 73 percent of Ukrainians disapprove of Poroshenko’s performance as president, and 87 percent of Ukrainians have an unfavorable opinion of their parliament.
Nalyvaichenko said he no longer has faith in Poroshenko.
“For me this is not personal,” he said. “Whoever becomes president or prime minister is immediately part of a corrupt and not transparent system. Immediately they are reproducing the same Soviet or simply corrupt practices and environment…. So, to get rid of that, to dismantle, to change the system, to reboot the country [we need to] get new people with absolutely different minds and mentality into the governmental offices.”
A New Fight
Nalyvaichenko is among a new breed of Ukrainian reformers who have emerged after the 2014 revolution.
Among Nalyvaichenko’s allies is former Georgian President Mikheil Saakashvili, who resigned as governor of Ukraine’s Odessa Oblast in November. The move was a protest against what Saakashvili claimed was stonewalling by Poroshenko and the majority of Ukraine’s political class in implementing anti-corruption reforms.
Saakashvili has since launched his own anti-corruption, opposition party called Wave.
“We had a revolution with lots of casualties,” Saakashvili told The Daily Signal in an earlier interview. “And every time a revolution happens, people have a right to expect revolutionary changes.”
One bright spot for Ukraine is its budding civil society. Across the country, political activists and humanitarian workers, including many millennials, have enabled the spread of democratic norms and are pushing for government accountability at the grassroots level.
“Across the country there is real willingness at the local level, at the grassroots level to stop corruption,” Nalyvaichenko said. “Fifteen or 20 years ago it was unimaginable that Ukraine would have such a powerful civil society.”
He continued:
I remember my parents and how modest the family used to be. How we young, young kids in Zaporizhia and other regions dreamed about another life. And to really have a chance with a free market, with the rule of law … for our children to create a new country with more opportunities. Our better future is here, and we should fight for that. I will not take no for an answer—from anyone.
Sacked
As head of the SBU, Nalyvaichenko endeavored to purge the security agency of its Soviet KGB past. He booted many personnel who had served in the SBU when it was the Ukrainian Soviet Socialist Republic’s branch of the KGB.
Nalyvaichenko spearheaded an effort to open up the SBU’s KGB archives, launching fresh investigations into Soviet crimes in Ukraine, including Joseph Stalin’s organized mass famine in the 1930s known as the Holodomor.
Related: Nolan Peterson: Dispatches from the forgotten war in Ukraine
He also hunted down and expelled Russian spies in Ukraine who were working for Russia’s successor agency to the KGB, the Federal Security Service of Russia, or FSB.
“With SBU, what I started with was to stop KGB practices,” Nalyvaichenko said. “I was the first and only chief of the SBU who actually started to detain FSB officers in Ukraine.”
The intent of Nalyvaichenko’s personnel scrub at the SBU went beyond security concerns. He wanted to shed the agency of its “Soviet mindset.”
To fill out the SBU’s thinned ranks, Nalyvaichenko tapped young political activists and reformers who had no living memory of life in the Soviet Union.
“That is my approach and my understanding of how it could be done in all the country,” Nalyvaichenko said, explaining how his SBU scrub could be used as a model for nationwide reforms.
The solution to beating corruption in Ukraine, according to Nalyvaichenko, is to elevate a new generation of political and business leaders.
“Let the generation shift happen in Ukraine,” Nalyvaichenko said. “For the new generation to be in the offices, to let them finally rule the country … it’s high time to finally stop with old practices.”
Nalyvaichenko’s second term as head of the SBU came at a tumultuous time for Ukraine. In the months following the February 2014 revolution, Russia launched a hybrid invasion of Ukraine’s Crimean Peninsula, ultimately annexing the territory.
Russia followed up the seizure of Crimea with a proxy war in the Donbas. A combined force of pro-Russian separatists and Russian regulars was on the march in eastern Ukraine in 2014, and there were worries then that Ukraine could be cleaved in two, or that Russian forces massed on Ukraine’s borders might stage a large-scale invasion.
In Kiev, the post-revolution government was at the time trying to establish its legitimacy and follow through on the pro-democratic promise of the revolution.
Meanwhile, officials were piecing together a military campaign out of the remnants of Ukraine’s armed forces, which had been gutted by decades of corruption and purposeful neglect.
Amid all of this, Nalyvaichenko pushed to prosecute corrupt government officials.
A New Fight
In Ukraine, opinions diverge about the hierarchy of threats facing the country.
A nearly three-year-old war between Ukrainian troops and a combined force of pro-Russian separatists and Russian regulars continues to simmer in the Donbas, Ukraine’s embattled eastern territory on the border with Russia.
About 10,000 Ukrainians have so far died in the conflict, which has also displaced about 1.7 million people. The war cost Ukraine an equivalent 20 percent of its gross national product in 2015, according to a 2016 report by the Institute for Economics and Peace.
The February 2015 cease-fire has failed. Military and civilian casualties still occur almost every day from landmines, artillery fire, rocket attacks, and small arms gun battles.
Ukraine’s military has rebuilt itself since 2014, but many front-line soldiers complain that after nearly three years of combat, they still aren’t getting basic supplies.
Despite the war’s cost in blood and treasure, Nalyvaichenko said the greatest threat facing Ukraine today is not on the battlefields of the Donbas, but within Kiev’s government halls.
“If you don’t understand how deep and how destroying the corruption is, you’ll never win the war,” Nalyvaichenko said. “This system, as I understand it, is not workable anymore. And because of war, because of Russian aggression, we now understand why. We simply, as a country, as a nation, have no time and no space anymore to continue with such corrupt practices.”
There is, however, a countervailing, quieter faction, particularly among Ukraine’s military brass, which says the war effort should take priority over any anti-corruption crusades.
Ukrainian military officials who spoke to The Daily Signal on background cautioned against ambitious anti-corruption agendas while the country is still at war.
And, according to the October 2016 International Republican Institute poll, most Ukrainians consider the war to be the biggest threat to the country.
Of the Ukrainians surveyed in the poll, 53 percent said the war in the Donbas was the country’s most important issue, compared with 38 percent who singled out corruption as the top issue.
“The tens of thousands of Russian soldiers, tanks, and artillery sitting along Ukraine’s southern and eastern borders are Ukraine’s sole existential threat,” Alexander Motyl, professor of political science at Rutgers University-Newark, wrote in OZY. “If [Russian President] Vladimir Putin gives the command, they could invade and possibly destroy large parts of the country. Corruption, by comparison, could eviscerate Ukraine’s institutions, but only in the long term.”
Outsider
As SBU chief, Nalyvaichenko spearheaded an investigation into a June 8, 2015, fire at an oil depot near Vasylkiv, Ukraine. The investigation allegedly implicated government officials in financial crimes, according to Nalyvaichenko’s account of events.
The investigation also revealed the undisclosed involvement of a Russian company in the oil depot.
Nalyvaichenko said he personally presented Poroshenko with the evidence and pushed for the issuance of arrest warrants.
Then, on June 15, 2015, Poroshenko fired Nalyvaichenko as head of the SBU. And three days later, Ukraine’s parliament voted to approve Nalyvaichenko’s ouster.
“That’s why I decided to be outside the government,” Nalyvaichenko said. “I really understood and understand for sure that to be subordinated and to fight the corruption, which is above you, is impossible. You become a part of this corrupt group of people, or you are outside. Here’s a red line. For me it was a clear decision.”
The Poroshenko administration declined a request for comment for this article. But, in an emailed statement to The Daily Signal, the SBU defended its track record of investigating and prosecuting corrupt officials.
“After the Revolution of Dignity, state leadership gave a clear indication to law enforcement authorities to begin the real fight against corruption, regardless of position, party affiliation, and the number of stars on one’s epaulets,” the SBU wrote in its statement to The Daily Signal.
According to the SBU, the security agency investigated 673 Ukrainian officials for corruption in 2016, compared with 545 in 2015, and 359 in 2014. The SBU said its investigations led to 256 convictions in 2016, an increase from 184 in 2015, and 181 in 2014.
“This suggests an increase in the intensity of the intelligence agencies in this cause,” the SBU said in its statement.
Nalyvaichenko acknowledged that Ukraine has made some progress in fighting corruption, but he said the past few years of investigations have largely targeted mid- and low-level government officials.
“The worst thing, I think, is that no single person from the top of the previous government [has been] prosecuted,” Nalyvaichenko said. “No single trial, or public hearings, or other procedures were organized by this government, by these officials. That’s I think the worst thing for the country and for Ukrainians.”
Nolan Peterson, a former special operations pilot and a combat veteran of Iraq and Afghanistan, is The Daily Signal’s foreign correspondent based in Ukraine.