 Techviral
Techviral
A Glimpse Into How Much Google Knows About Russian Government Hackers
A 2014 leaked private report from Google shows how much the internet giant knows about government hacking groups.
Motherboard: In October of 2014 an American security company revealed that a group of hackers affiliated with the Russian government, dubbed APT28, had targeted Georgia and other Eastern European countries in a wide-ranging espionage campaign. Two and a half years later, APT28—also known as “Fancy Bear” or “Sofacy”—is a household name not just in the cybersecurity industry, but in the mainstream too, thanks to its attack on the US Democratic party and the ensuing leaks of documents and emails.
Before that report by FireEye, APT28 was a well-kept secret within the cybersecurity industry. At the time, several companies were willing to share information about the hacking group. Even Google investigated the group, and penned a 40-page technical report on the hacking group that has never been published before.
This sort of document, which Motherboard obtained from two independent sources, may be a common sight in the threat intelligence industry, but the public rarely gets to see what such a report from Google looks like. The report draws from one of Google’s most interesting sources of data when it comes to malware and cybersecurity threats: VirusTotal, a public malware repository that the internet giant acquired in 2012.
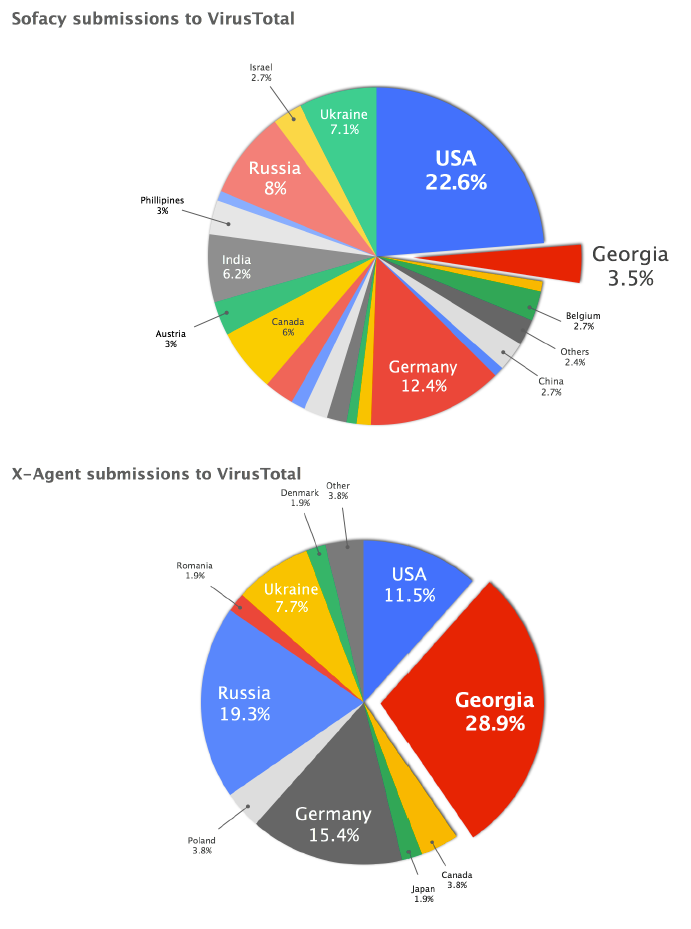
Sofacy and X-Agent, the report read, referring to the malware used by APT28, “are used by a sophisticated state-sponsored group targeting primarily former Soviet republics, NATO members, and other Western European countries.”
“It looks like Google researchers were well aware of Sofacy before it was publicly disclosed.”
While Google security researchers don’t dwell into who’s really behind these operations, they do hint that they agree with the now widespread belief that APT28 works for the Russian government in a clever, indirect, way—in the very title of the report: “Peering into the Aquarium.”
While that might seem like an obscure title, for those who follow Russian espionage activities, it’s a clear reference to the headquarters of the military intelligence agency known as GRU or Glavnoye Razvedyvatel’noye Upravleniye, which are popularly known as “The Aquarium.”
“It looks like Google researchers were well aware of Sofacy before it was publicly disclosed,” Matt Suiche, a security researcher and the founder of Comae Technologies and the OPCDE conference, told Motherboard in an online chat after reviewing the report. “And also attributed Sofacy and X-Agent to Russia before it was publicly done by FireEye, ESET or CrowdStrike.”
In its report Google security researcher note that APT28 attacks a large number of targets with its first-stage malware Sofacy, but only uses the more tailored and sophisticated X-Agent, which was recently used against Ukraine’s military units, for “high-priority targets.”
“Sofacy was three times more common than X-Agent in the wild, with over 600 distinct samples,” Google’s report stated.
Asked for comment, a Google spokesperson said via email that the company’s “security teams are constantly monitoring potential threats to internet users, and regularly publish information to better protect them.”
The report noted that Georgia had the highest ratio of submissions of Sofacy malware, followed by Romania, Russia and Denmark.
While this report is now a bit dated, it shows that for all its sophistication, APT28 has been often caught in the act of hacking politically interesting targets, betraying the origin of the hackers behind the dry nickname. It also reveals how much a company like Google, which doesn’t have software installed on thousands of customers computers like other antivirus and security vendors that is designed to specifically detect malware, can still learn a lot about government hacking groups thanks to the other data it has access to.
*** Related reading:
State-sponsored hackers targeting prominent journalists, Google warns
Politico: Google has warned a number of prominent journalists that state-sponsored hackers are attempting to steal their passwords and break into their inboxes, the journalists tell POLITICO.
Jonathan Chait of New York Magazine said he received several messages from Google warning him about an attack from a government-backed hacker starting shortly after the election. He said the most recent warning came two to three weeks ago.
Julia Ioffe, who recently started at The Atlantic and has covered Russia for years, said she got warnings as recently as two weeks ago. (See one of the warnings: http://bit.ly/2kMUyRb)
Some journalists getting the warnings say they suspect the hackers could be Russians looking to find incriminating emails they could leak to embarrass journalists, either by revealing alleged liberal bias or to expose the sausage-making of D.C. journalism.
“The fact that all this started right after the election suggests to me that journalists are the next wave to be targeted by state-sponsored hackers in the way that Democrats were during it,” said one journalist who got the warning. “I worry that the outcome is going to be the same: Someone, somewhere, is going to get hacked, and then the contents of their gmail will be weaponized against them — and by extension all media.”
The Russian embassy did not respond to a request for comment.
Russian embassy Washington DC
Google cautioned that the warnings did not mean the accounts had been compromised already and were sent due to “an abundance of caution.”
“Since 2012, we’ve notified users when we believe their Google accounts are being targeted by government-backed attackers,” said a Google spokesperson in a statement. “We send these warnings out of an abundance of caution — they do not indicate that a user’s account has already been compromised or that a more widespread attack is occurring when they receive the notice.”
Ezra Klein, the founder of Vox, said he had received the warning as recently as a few days back. CNN senior media reporter Brian Stelter said he has been getting the alerts for the past few months.
Other journalists who confirmed they’ve recently gotten the warnings include New York Times national security correspondent David Sanger, Times columnist Paul Krugman and Yahoo Washington bureau chief Garance Franke-Ruta.
GQ special contributor Keith Olbermann said the warnings started a few weeks after the election, and he received the most recent alert earlier this week, a “big bright red bar” across the top of his Gmail. Some of the reporters say they are tightening up their email security to try to prevent the hackers from getting in.
Chait also said he was “contacted over email by a stranger who offered to help me by giving me an encryption key to protect me from hackers. He would not give me his name, meet me or talk on the phone, despite repeated requests.”
The stranger also emailed The Atlantic’s David Frum, James Fallows and Adam Serwer, Andrew Sullivan and Ars Technica’s Dan Goodin.
Stanford professor Michael McFaul, the former U.S. ambassador to Russia, said he also received hacking warnings from Google. He added: “Given my background, one would have to guess that it’s the Russians.”






























 NBC
NBC According to an
According to an 