Hack-O-Matic…some good ones and others not so much.
800 Schools
“Unless we have irrefutable evidence to suggest otherwise, we need to assume confidential data has been compromised,” Hamid Karimi, vice president of business development and the security expert at Beyond Security. “That should be a cause for concern. To remedy the situation, all schools and institutions that serve minors must submit to (a) stricter set of cybersecurity rules.”
The breached school websites, which spanned nationwide from New Jersey to Arizona and Virginia to Connecticut, are all powered by a company called SchoolDesk. The company since has handed over its server — which runs out of Georgia — to the FBI for investigation and also has hired external security firms to trace the hackers. The Atlanta-based company said after the hack that technicians detected that a small file had been injected into the root of one of its websites.
“The websites were redirected to an iframed YouTube video. No data was lost or altered in any way. Because we’re currently working with the FBI in an active investigation of this incident, as well as forensic team from Microsoft, we cannot yet discuss any technical details or exact methods of access to SchoolDesk’s network or software,” a spokesperson for SchoolDesk told Fox News.
The company has insisted that no personal or student information was exposed, but some security experts say the matter should be closely monitored, especially as minors are involved.
“In most hacks, organizations do not have full visibility into what happened or what information was compromised,” surmised Eric Cole, who served as commissioner on cyber security for President Barack Obama, and was formally a senior vice president at MacAfee and the chief scientist at Lockheed Martin. “In almost every breach, what is initially reported is usually extremely conservative and over the weeks following a breach, it is always worse than what was originally reported.”
The proud culprits of the hack? A shadowy pro-ISIS hacktivist outfit known as “Team System DZ.” Barely reported by Fox News, while other media outlets did nothing about about.
***
Pentagon Hackers for Hire
Just over a year ago, following the success of the pilot, we announced the U.S. Department of Defense was expanding its “Hack the Pentagon,” initiatives. To date, HackerOne and DoD have run bug bounty challenges for Hack the Pentagon, Hack the Army and Hack the Air Force.
The success of these programs has been undeniable and our amazing community of hackers continues to impress even us!
DoD has resolved nearly 500 vulnerabilities in public facing systems with bug bounty challenges and hackers have earned over $300,000 in bounties for their contributions — exceeding expectations and saving the DoD millions of dollars. You can read more in our recent case study “Defending the Federal Government from Cyber Attacks.”
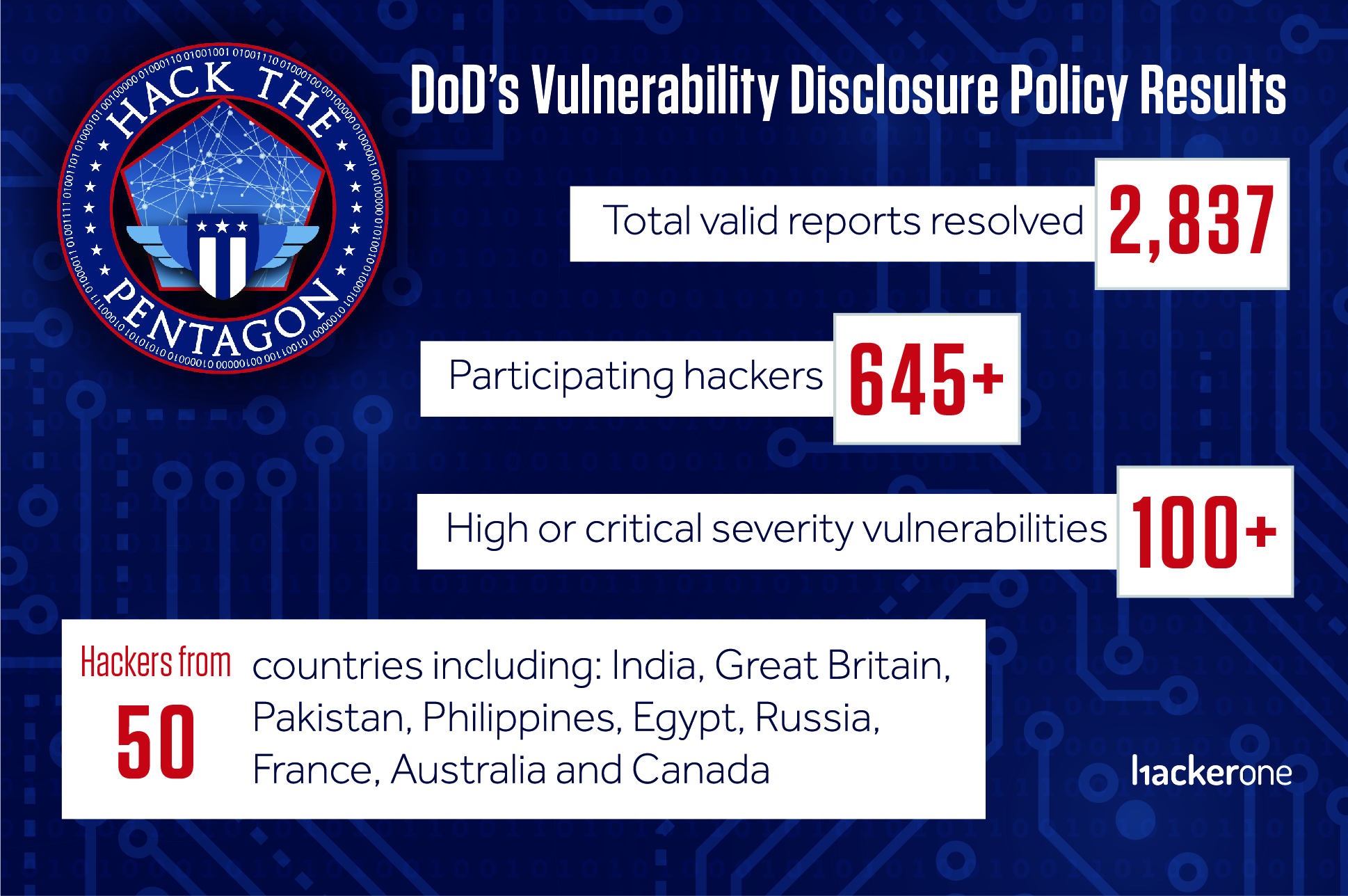
2,837 Bugs Resolved With DoD’s Vulnerability Disclosure Policy
The DoD’s Vulnerability Disclosure Policy (VDP) is another essential, likely less talked about, part of the Hack the Pentagon initiative pioneered by DoD’s Defense Digital Service team.
A VDP is the, “see something say something of the internet”. DoD’s policy, and others like it, provide clear guidance for any hacker anywhere in the world to safely report a potential vulnerability so it can be resolved. Maintaining the security of the DoD’s networks is a top priority and their VDP is another proven way to resolve unknown security issues.
While a bounty or cash incentives are not awarded for vulnerabilities reported through the VDP, that has not stopped hackers eager to do their part to help protect the DoD’s assets. Nearly 650 hackers from more than 50 countries have successfully reported valid vulnerabilities through the VDP.
Thanks to these hackers and the pioneering team at DoD, 2,837 security vulnerabilities have been resolved in nearly 40 DoD components. Of these vulnerabilities, over 100 have been high or critical severity issues, including remote code executions, SQL injections, and ways to bypass authentication.
While the majority of participating hackers have been from United States, the top contributing countries include India, Great Britain, Pakistan, Philippines, Egypt, Russia, France, Australia and Canada. More here, at least this was a positive objective, we think.
*** Related reading: Boeing 757 Testing Shows Airplanes Vulnerable to Hacking, DHS Says
Hacking Through Aircraft Wi-Fi
A Department of Homeland Security official admitted that a team of experts remotely hacked a Boeing 757 parked at an airport.
During a keynote address on Nov. 8 at the 2017 CyberSat Summit, a Department of Homeland Security (DHS) official admitted that he and his team of experts remotely hacked into a Boeing 757.
This hack was not conducted in a laboratory, but on a 757 parked at the airport in Atlantic City, N.J. And the actual hack occurred over a year ago. We are only now hearing about it thanks to a keynote delivered by Robert Hickey, aviation program manager within the Cyber Security Division of the DHS Science and Technology (S&T) Directorate.
“We got the airplane on Sept. 19, 2016. Two days later, I was successful in accomplishing a remote, non-cooperative, penetration,” Hickey said in an article in Avionics Today. “[That] means I didn’t have anybody touching the airplane; I didn’t have an insider threat. I stood off using typical stuff that could get through security, and we were able to establish a presence on the systems of the aircraft.”
While the details of the hack are classified, Hickey admitted that his team of industry experts and academics pulled it off by accessing the 757’s “radio frequency communications.”
We’ve been hearing about how commercial airliners could be hacked for years.
You might remember when a governmental watchdog admitted that the interconnectedness of modern commercial airliners could “potentially provide unauthorized remote access to aircraft avionics systems.” The concern was that a hacker could go through the Wi-Fi passenger network to hijack a plane while it was in flight.
And in a 2015 report by the U.S. Government Accountability Office (pdf), the agency warned, “Internet connectivity in the cabin should be considered a direct link between the aircraft and the outside world, which includes potential malicious actors.”
At the time, U.S. Rep. Peter DeFazio (D-Ore.) said, the “FAA must focus on aircraft certification standards that would prevent a terrorist with a laptop in the cabin or on the ground from taking control of an airplane through the passenger Wi-Fi system.”
The same year, security researcher Chris Roberts ended up in hot water with the feds after tweeting about hacking the United Airlines plane he was traveling on. The FBI claimed Roberts said he took control of the navigation.
A Hack In The Box presentation by Hugo Teso in 2013 suggested that thanks to the lack of authentication features in the protocol Aircraft Communications Addressing and Report System (ACARS), an airliner could be controlled via an Android app. Flight management software companies, as well as the FAA, disputed Teso’s claims.
All of that means that airline pilots have heard of those vulnerabilities before, too. Yet at a technical meeting in March 2017, several shocked airline pilot captains from American Airlines and Delta were briefed on the 2016 Boeing 757 hack. Hickey said, “All seven of them broke their jaw hitting the table when they said, ‘You guys have known about this for years and haven’t bothered to let us know because we depend on this stuff to be absolutely the bible.’”
As CBS News pointed out, Boeing stopped producing 757s in 2004, but that aircraft is still used by major airlines, such as American, Delta and United. President Trump has a 757, and Vice President Pence also uses one. In fact, Avionics Today claimed 90 percent of commercial planes in the sky are legacy aircraft that were not designed with security in mind.
Boeing told CBS that it firmly believes the test “did not identify any cyber vulnerabilities in the 757, or any other Boeing aircraft.”
Furthermore, an unnamed official briefed on the test told CBS the results of the hack on an older aircraft was good information to have, adding, “but I’m not afraid to fly.” (Not feeling good about this aircraft hack at all, dont we have a missing plane or one that crashed where it was suspected there may have been a hack involved?)