It was a very real condition until just hours ago where the United States Secret Service found the threat. W can only hope it has been neutralized and there is no more threat…but read on…
After checking several sources for as much complete information, below are some terrifying details. There are likely more to be revealed in coming days as the investigation continues.
Per the Secret Service website:
NEW YORK – The U.S. Secret Service dismantled a network of electronic devices located throughout the New York tristate area that were used to conduct multiple telecommunications-related threats directed towards senior U.S. government officials, which represented an imminent threat to the agency’s protective operations.
This protective intelligence investigation led to the discovery of more than 300 co-located SIM servers and 100,000 SIM cards across multiple sites.
In addition to carrying out anonymous telephonic threats, these devices could be used to conduct a wide range of telecommunications attacks. This includes disabling cell phone towers, enabling denial of services attacks and facilitating anonymous, encrypted communication between potential threat actors and criminal enterprises.
While forensic examination of these devices is ongoing, early analysis indicates cellular communications between nation-state threat actors and individuals that are known to federal law enforcement.
“The potential for disruption to our country’s telecommunications posed by this network of devices cannot be overstated,” said U.S. Secret Service Director Sean Curran. “The U.S. Secret Service’s protective mission is all about prevention, and this investigation makes it clear to potential bad actors that imminent threats to our protectees will be immediately investigated, tracked down and dismantled.”
These devices were concentrated within 35 miles of the global meeting of the United Nations General Assembly now underway in New York City. Given the timing, location and potential for significant disruption to New York telecommunications posed by these devices, the agency moved quickly to disrupt this network. The U.S. Secret Service’s Advanced Threat Interdiction Unit, a new section of the agency dedicated to disrupting the most significant and imminent threats to our protectees, is conducting this investigation. This investigation is currently ongoing.
The Department of Homeland Security’s Homeland Security Investigations, the Department of Justice, the Office of the Director of National Intelligence and the NYPD, as well as other state and local law enforcement partners, provided valuable technical advice and assistance in support of this investigation.
This is an ongoing investigation.
***
The BBC in part also adds this:
The devices were seized from SIM farms at abandoned apartment buildings across more than five sites. Officials did not specify the locations.
The discovery followed an investigation into anonymous “telephonic threats” directed at three US government officials this spring, unnamed officials told the New York Times.
One of the officials works in the Secret Service and the other two work at the White House, according to the newspaper.
Investigators also told CBS News they found 80g of cocaine, illegal firearms, computers and phones.
***
CBS includes in part:Telephonic threats to multiple senior U.S. officials this past spring – including multiple people protected by the Secret Service – first triggered the investigation, but officials say the network was seized within the last three weeks.
Still, another official added that “it would be unwise to assume” there aren’t other such networks in the U.S.
The investigation remains ongoing, according to the U.S. Secret Service. There have been no arrests yet, but officials said, “there could be arrests down the road,” adding that “from an operational perspective, we want those behind the network to know that the Secret Service is aware and that we’re kind of coming for them.”
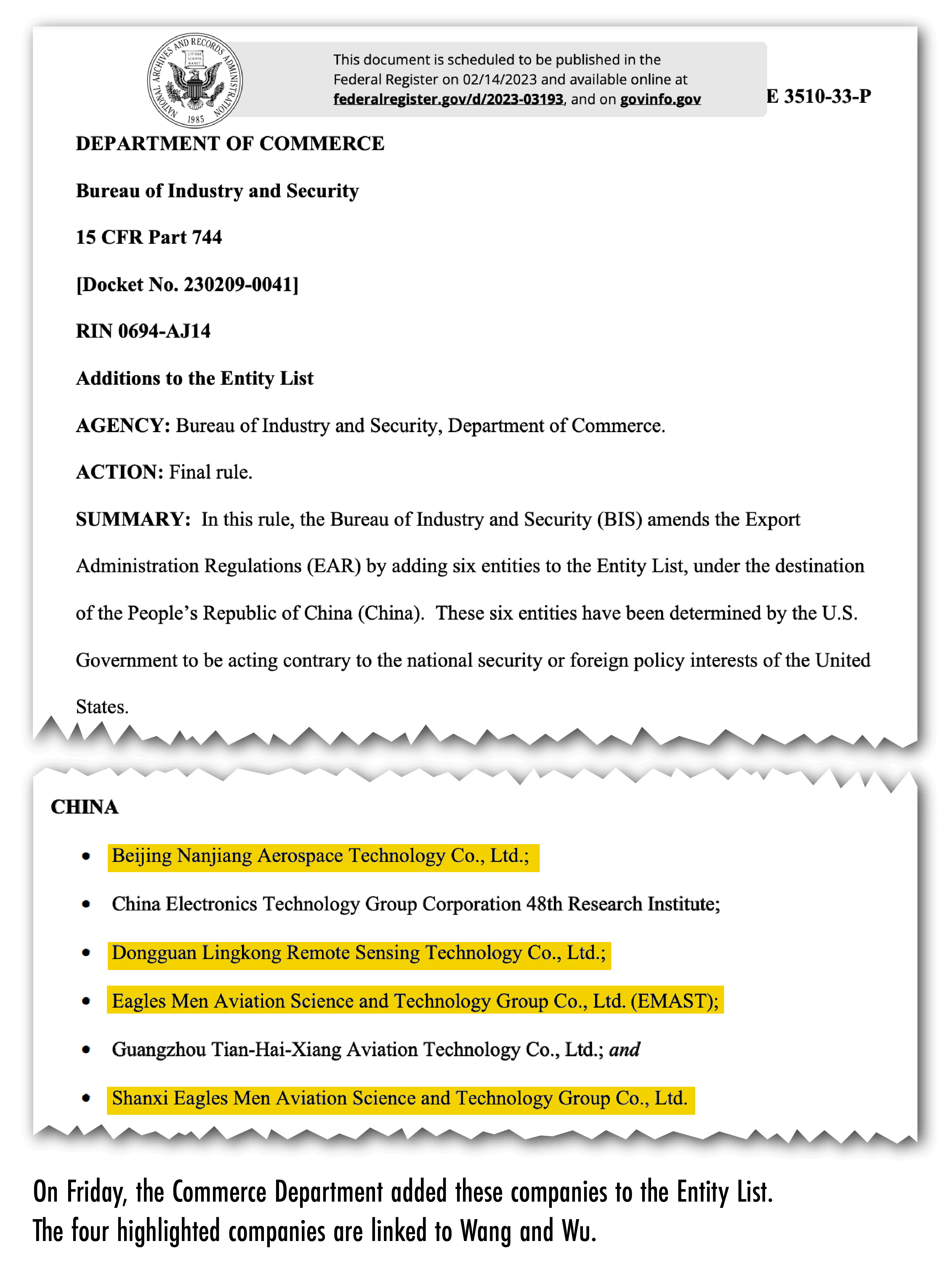
This photo provided by the U.S. Secret Service, in New York, Monday, Sept. 22, 2025, shows part of a wall of SIM boxes that were seized by the agency. (U.S. Secret Service via AP)
Then from the Associated Press in part:
The operation had the capability of sending up to 30 million text messages a minute, McCool said.
“The U.S. Secret Service’s protective mission is all about prevention, and this investigation makes it clear to potential bad actors that imminent threats to our protectees will be immediately investigated, tracked down and dismantled,” the agency’s director, Sean Curran, said in a statement.
Officials also warned of the havoc the network could have caused if left intact. McCool compared the potential impact to the cellular blackouts that followed the Sept. 11 attacks and the Boston Marathon bombing, when networks collapsed under strain. In this case, he said, attackers would have been able to force that kind of shutdown at a time of their choosing.


 .Satellite imagery of Ream Naval Base from 5 February 2023, annotated to show the shape of the pier extension. Original image courtesy of BlackSky
.Satellite imagery of Ream Naval Base from 5 February 2023, annotated to show the shape of the pier extension. Original image courtesy of BlackSky