Illegally Export Fighter Jet Engines and Unmanned Aerial Vehicle to China
Wenxia Man, aka Wency Man, 45, of San Diego, was sentenced today to 50 months in prison for conspiring to export and cause the export of fighter jet engines, an unmanned aerial vehicle – commonly known as a drone – and related technical data to the People’s Republic of China in violation of the Arms Export Control Act.
The sentence was announced by Assistant Attorney General for National Security John P. Carlin, U.S. Attorney Wifredo A. Ferrer of the Southern District of Florida, Special Agent in Charge Mark Selby of the U.S. Immigration and Customs Enforcement’s Homeland Security Investigations (ICE-HSI) in Miami and Special Agent in Charge John F. Khin of the Department of Defense’s Defense Criminal Investigative Service (DCIS).
On June 9, 2016, Man was convicted by a federal jury in the Southern District of Florida of one count of conspiring to export and cause the export of defense articles without the required license.
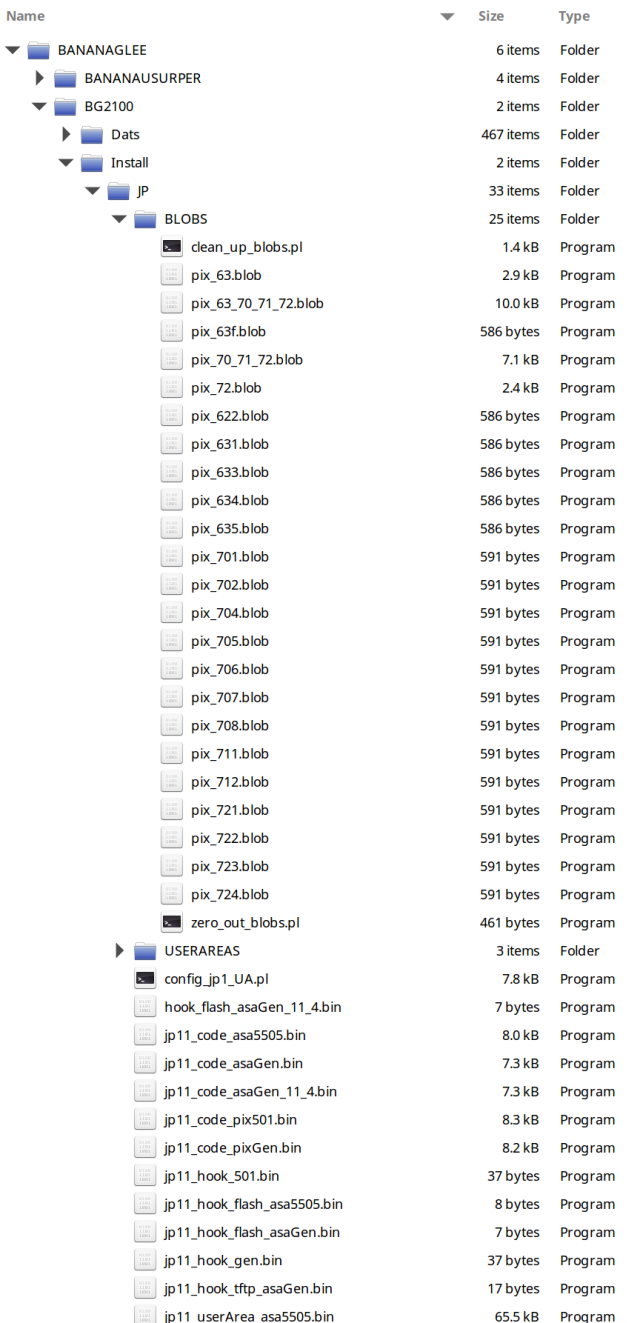
According to evidence presented at trial, between approximately March 2011 and June 2013, Man conspired with Xinsheng Zhang, who was located in China, to illegally acquire and export to China defense articles including: Pratt & Whitney F135-PW-100 engines used in the F-35 Joint Strike Fighter; Pratt & Whitney F119-PW-100 turbofan engines used in the F-22 Raptor fighter jet; General Electric F110-GE-132 engines designed for the F-16 fighter jet; the General Atomics MQ-9 Reaper/Predator B Unmanned Aerial Vehicle, capable of firing Hellfire Missiles; and technical data for each of these defense articles. During the course of the investigation, when talking to an undercover HSI agent, Man referred to Zhang as a “technology spy” who worked on behalf of the Chinese military to copy items obtained from other countries and stated that he was particularly interested in stealth technology.
HSI and DCIS investigated the case. Assistant U.S. Attorney Michael Walleisa of the Southern District of Florida and Trial Attorney Thea D. R. Kendler of the National Security Division’s Counterintelligence and Export Control Section prosecuted the case.
Photo: balicad24.com
Announcement by the Justice Department
Related reading: 5 Weapons China Stole & Copied from the US
Related reading: Chinese cyber spies may be watching you, experts warn
In part from FreeBeacon:
Michael Walleisa, assistant U.S. Attorney for the Southern District of Florida, asked the judge to impose the maximum sentence of 78 months for the weapons conspiracy conviction.
“There is hardly a more serious case than a case such as this that involves some of our most sophisticated fighter jet engines and unmanned weaponized aerial drones,” Walleisa said in a sentencing memorandum.
“The potential for harm to the safety of our fighter pilots, military personnel, and national security which would occur had the defendant been successful is immeasurable, particularly where, as here the clear intent of the co-conspirators was to enable the People’s Republic of China to reverse engineer the defense articles and manufacture fighter jets and UAV’s.”
The conspiracy revealed that China was seeking to “increase its military capabilities and might to the potential detriment of the United States,” Walleisa said.
The U.S. government imposed an arms embargo on China in 1990 following the Chinese military’s massacre of unarmed pro-democracy protesters in Beijing’s Tiananmen Square a year earlier.
Between 2011 and 2013, Man and Zhang worked together to solicit three sets of General Electric and Pratt and Whitney turbofan engines for the F-35, F-22, and F-16 jets, as well as a General Atomics Reaper drone and technical details of the equipment. The Chinese were prepared to pay $50 million for the embargoed items.
Authorities launched an investigation of the case after Man contacted a defense industry source who alerted U.S. Immigration and Customs Enforcement’s Homeland Security Investigations unit in Miami. The Pentagon’s Defense Criminal Investigative Service also investigated the case.
Man used a company called AFM Microelectronics, Inc. in trying to buy the military equipment. She disclosed to an undercover federal agent in 2012 that the jet engines were meant for the Chinese government and that she knew it was illegal to export them, according to court papers.
China is engaged in a major military buildup that includes two new advanced stealth jet fighters that U.S. intelligence agencies say benefitted from stolen American aircraft technology.
The attempt to buy embargoed jet fighter engines highlights what military analysts say is China’s major technology shortfall—its inability to manufacture high-quality jet engines. Turbofan engines require extremely precise machine work and parts because of the high speeds of their spinning engine fans.
Zhang was described by the government in court papers as a “technology spy” working for China’s military-industrial complex. The Chinese government buys arms and military technology from Russia and other states “so that China can obtain sophisticated technology without having to conduct its own research,” the indictment in the case states.
The name of the Chinese entity was not disclosed. China’s government defense industry group is SASTIND, an acronym for State Administration for Science, Technology and Industry for National Defense.
Zhang sought to buy the operating system and aircraft control system for the MQ-9 Reaper as well as the unmanned aerial vehicle itself and the technical design data for the aircraft. The drone sought was an armed version capable of firing Hellfire missiles.
Man, 45, was convicted of one count of conspiracy to export defense goods with a license.
At sentencing on Friday, U.S. District Judge Beth Bloom told the court that Man hoped to get a $1 million commission on the illegal export and that she wanted to help China compete with the United States militarily.
“I’m innocent,” Man told the judge, the South Florida Sun-Sentinel newspaper reported. “This is my country, too.” She plans to appeal the conviction that was reached after a jury trial in June.
Michael Pillsbury, a China specialist at the Hudson Institute, said the Man case highlights China’s large-scale technology theft program.
“The scope and the ambition of their technology intelligence collection is breathtaking,” said Pillsbury. “They’re not after petty secrets.”
The Man case is similar to an earlier Chinese technology acquisition operation headed by Chi Mak, another naturalized Chinese citizen. In 2007, Mak, an electrical engineer at the U.S. firm Power Paragon, was convicted of conspiracy to export sensitive electronics defense technology to China.
Mak was a long-term technology spy who operated for 20 years. U.S. officials believe Mak provided China with secrets to the Aegis battle management system, the heart of current Navy warships.
China has deployed a similar version of the Aegis ship, known as the Type 052D warship.

 CNN reported Wednesday that Cabrera’s attorney, Stephen Bronis, said $20,000(given to the Clinton-Gore campaign) was not intended to buy protection for drug smuggling.
CNN reported Wednesday that Cabrera’s attorney, Stephen Bronis, said $20,000(given to the Clinton-Gore campaign) was not intended to buy protection for drug smuggling.