Founderscode wrote about this December of 2020 in detail.
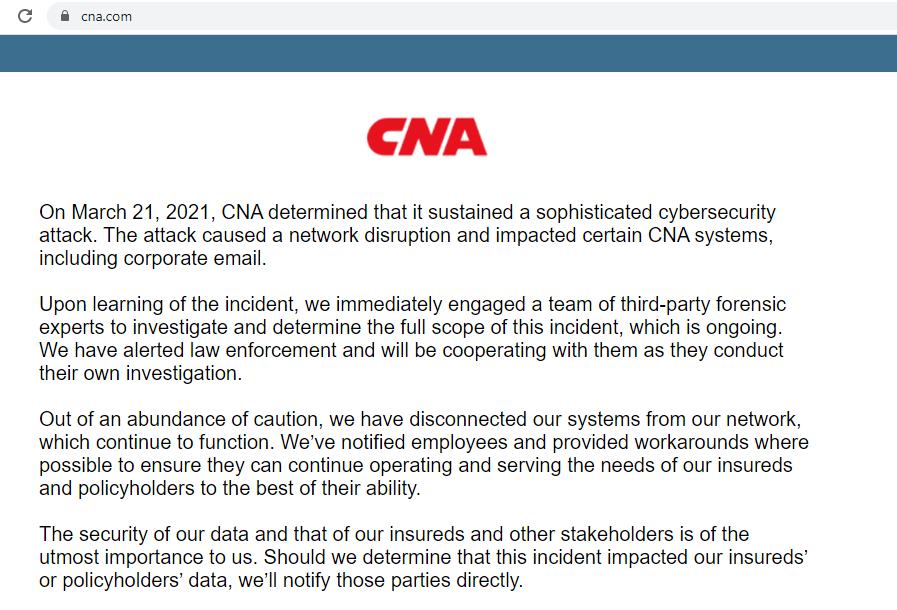
RCP, in part: In the months leading up to November’s election, voting officials in major cities and counties worked with a progressive group funded by Facebook founder Mark Zuckerberg and its allies to create ballots, strategically target voters and develop “cure” letters in situations where mail-in ballots were in danger of being tossed out.
The Center for Tech and Civic Life, or CTCL, provided millions of dollars in private funding for the elections that came from a $350 million donation from Zuckerberg and his wife, Priscilla Chan. The CTCL gave “COVID-19 response” grants of varying amounts to 2,500 municipalities in 49 states.

In exchange for the money, elections divisions agreed to conduct their elections according to conditions set out by the CTCL, which is led by former members of the New Organizing Institute, a training center for progressive groups and Democratic campaigns.
A CTCL partner, the Center for Civic Design, helped design absentee ballot forms and instructions, crafted voter registration letters for felons and tested automatic voter registration systems in several states, working alongside progressive activist groups in Michigan and directly with elections offices in Georgia and Utah.
Still other groups with a progressive leaning, including the Main Street Alliance, The Elections Group and the National Vote at Home Institute, provided support for some elections offices.

Facebook, with the CTCL, was also part of the effort, providing a guide and webinar for election officials on how to engage voters. Included were directions to report “voter interference” to Facebook authorities. The company also provided designated employees in six regions of the U.S. to handle questions. Together, the groups strategically targeted voters and waged a voter assistance campaign aimed at low-income and minority residents who typically shun election participation, helping Democratic candidates win key spots all over the U.S.
The little-explored roles of CTCL and other such groups emerged in emails and other records obtained by RealClearInvestigations and public documents secured by conservative litigants and groups, including the Foundation for Government Accountability, which has filed more than 800 public records requests with elections offices accepting the grants.
Previously, the Zuckerberg-funded effort has been described in generally positive terms, notably when NPR reported in December on “How Private Money From Facebook’s CEO Saved The 2020 Election” — in the face of the coronavirus pandemic, President Trump’s doubts about the legitimacy of the process and “Congress’ neglect.”
Zuckerberg did not respond to an emailed request from RCI for comment. In a post-election interview, he praised Facebook’s security work during the election and singled out its policing of “misinformation.” He noted working with polling officials to watch for information that might lead to “voter suppression” and said Facebook had strengthened its enforcement “against militias and conspiracy networks like Q-Anon.”



/cdn.vox-cdn.com/uploads/chorus_image/image/69328731/1142319105.0.jpg)