No one in Washington DC or media talks about the ever constant cyber attacks against all things United States.
There have been countless hearings on The Hill about Russian operations against the election architecture in the United States as well as other allied countries. While Russia is one of the top threats, Iran and North Korea are also guilty, yet China likely ranks number two behind Russia.
So, anti-Trump people inside the Beltway blame the Trump White House for the lack of leadership on the issue(s) especially when it comes to protections on the voter-roll databases at the state level and the learning curve of vulnerabilities of the voting machines themselves. So…where are these lawmakers and the bills they have introduced for debate, committee and eventual passage in both Houses of Congress anyway?
Who is protecting data across the board, our data? Where is the Department of Homeland Security and the FBI on the matter? Both those agencies were assigned to collaborate with threatened State Elections Commissions during the General election. Remember that?
This all began during the Obama administration where the ultimate punishment was to expel Russian diplomatic officials, close two dachas and the Russian compound in San Francisco. Has that sent a message to Moscow and fixed the problem(s)? NO….
There are thousands of experts outside the Federal government that do offer assistance with investigations and attributions and they too can offer some in sight into legislative frameworks and yet no one knows if that has been forthcoming.
*** Russian Attacks Will Continue
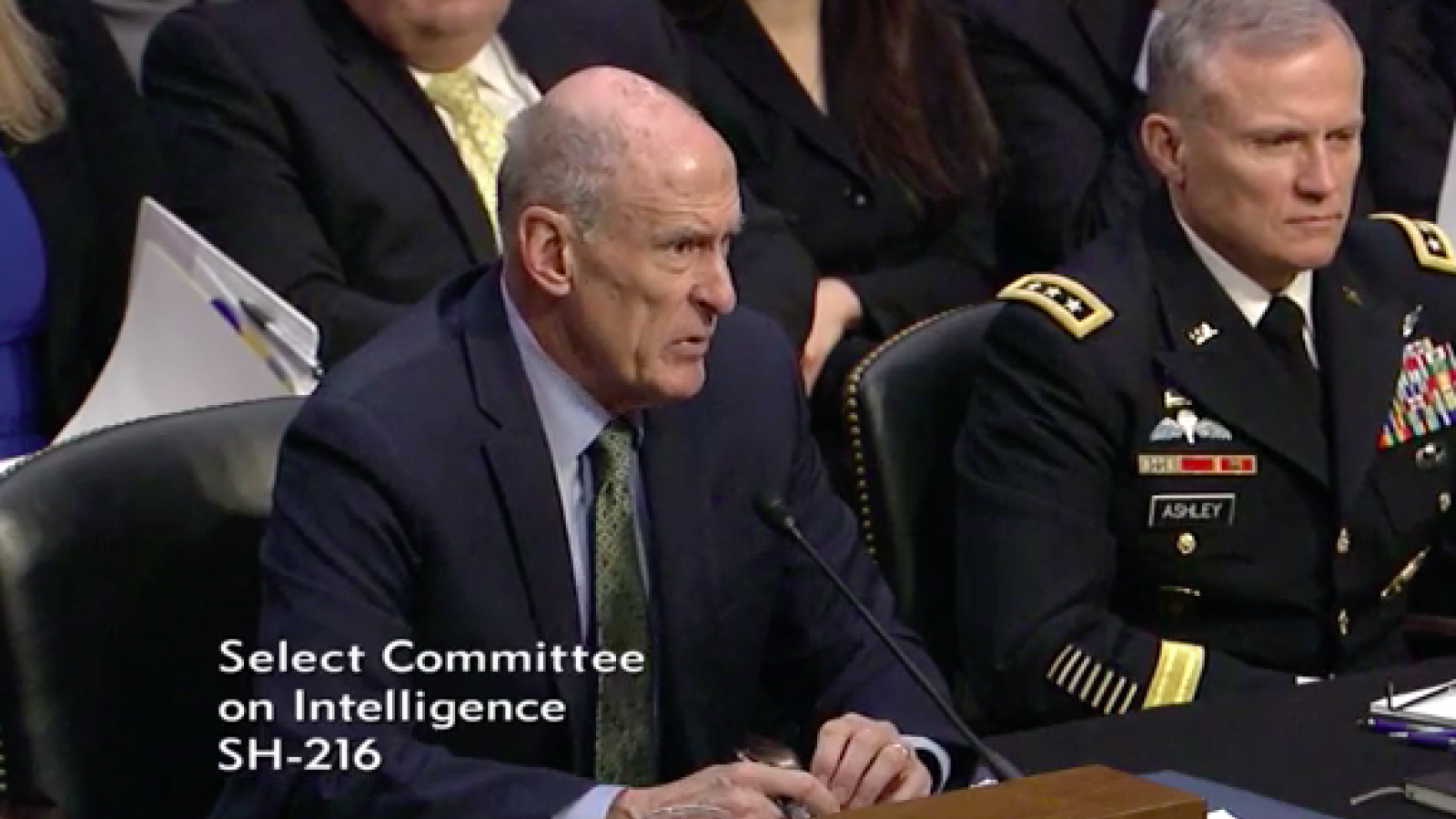
UPDATE: As the nation’s top intelligence chiefs testified before the Senate Intelligence Committee Tuesday, spelling out the very real threat Russia continues to pose to our democracy, Director of National Intelligence Dan Coats admitted “there is no single agency leading the United States’ efforts to respond to and combat Russian election meddling.”
Multiple Senators on the panel expressed their concern for President Trump’s ongoing unwillingness to acknowledge Russian interference in the 2016 election, echoing a common sentiment among national security experts that an absence of leadership at the top is hindering U.S. efforts to fight back.
CNN:
… Coats said Tuesday “there should be no doubt” that Russia sees the 2018 US elections as a target.
Coats and the other top national security officials told the Senate Intelligence Committee on Tuesday that they still view Moscow as a threat to the 2018 elections, a stance that appears at odds with President Donald Trump’s repeated dismissals of Russian election meddling.
“We expect Russia to continue using propaganda, social media, false-flag personas, sympathetic spokesmen and other means to influence, to try to build on its wide range of operations and exacerbate social and political fissures in the United States,” Coats said at a hearing on worldwide threats. “There should be no doubt that Russia perceives its past efforts as successful and views the 2018 US midterm elections as a potential target for Russian influence operations.”
(…)
Sen. Angus King, I-Maine, pressed on the disparity between the intelligence community’s viewpoint and the president’s — urging the intelligence chiefs to persuade the president to accept their findings that Russia interfered in the 2016 election.
“My problem is, I talk to people in Maine who say the whole thing is a witch hunt and a hoax ‘because the President told me’,” King said. “There’s no doubt, as you all have testified today, we cannot confront this threat, which is a serious one, with a whole of government response when the leader of the government continues to that deny it exists.”
John Sipher, a former chief of station for the CIA who served for 28 years in Russia, Europe, and Asia, told me that the intelligence community will continue to be focused on Russia’s threat “no matter what the White House says or doesn’t say.” Ultimately, though, it will be up to Trump to implement meaningful changes.
“The IC is not the most important in this case,” Sipher said, referring to the intelligence community. “They may uncover what the Russians are up to but they can’t really defend against it or take actions to deter it, unless the President supports a covert action effort to screw with the Russians, like with a cyber attack.”
“Tightening up our social media, protecting voter-registration systems and procedures—those things are beyond the ability or mandate of the IC,” Sipher said. “And I don’t think we have done nearly enough to deter or defend against Russian attacks.
US intel chiefs unanimous that Russia is targeting 2018 elections (CNN)
Russia Will Meddle in the Midterms (The Atlantic)
No Agency Leading U.S. Response to Russian Election Meddling, Says Intel Chief (The Daily Beast)
As the Senate Intelligence Committee hears from the nation’s top intelligence and national security officials on worldwide threats, a prepared written assessment warns of ongoing Russian efforts to undermine democracy.
“Foreign elections are critical inflection points that offer opportunities for Russia to advance its interests both overtly and covertly,” says the assessment. “The 2018 US mid-term elections are a potential target for Russian influence operations.”
(…)
“We assess that the Russian intelligence services will continue their efforts to disseminate false information via Russian state-controlled media and covert online personas about US activities to encourage anti-US political views,” the statement says.
“Moscow seeks to create wedges that reduce trust and confidence in democratic processes, degrade democratization efforts, weaken US partnerships with European allies, undermine Western sanctions, encourage anti-US political views, and counter efforts to bring Ukraine and other former Soviet states into European institutions.”
In his opening statement, Vice Chairman Mark Warner (D-VA) noted President Trump’s absence of leadership on the issue.
Sen. Mark Warner, D-Va., the top Democrat on the committee, said in prepared remarks that “the President inconceivably continues to deny the threat posed by Russia. He didn’t increase sanctions on Russia when he had a chance to do so. He hasn’t even Tweeted a single concern. This threat demands a whole-of-government response, and that needs to start with leadership at the top.”
U.S. intel agencies expect Russia to escalate election meddling efforts (NBC News)






