Keep this post in your bookmarks as we enter into the 2020 general election….
Primer:
1. China plants industrial espionage operatives in the U.S. that steal government contract secrets and sell them back to China. FBI caught at least one.
2. Through cyber espionage, China has stolen much of the F-35 technology, more than 50 terabytes.
3. John Kerry and Joe Biden did exactly the same thing as Hillary…sold access for money while exploiting it all as diplomatic missions with the title(s) of bi-lateral agreements.
4. Subpoena former Treasury Secretary Jack Lew and ask him about the CFIUS approvals of Chinese back enterprises. We may surely need to go back to former Treasury Secretary, Tim Geithner, did he set the table for all this with Obama’s approval creating that ‘Asia Pivot‘?
5. What does Congress know about foreign investments and when do they know it? They get reports, but who is asking questions, anyone?
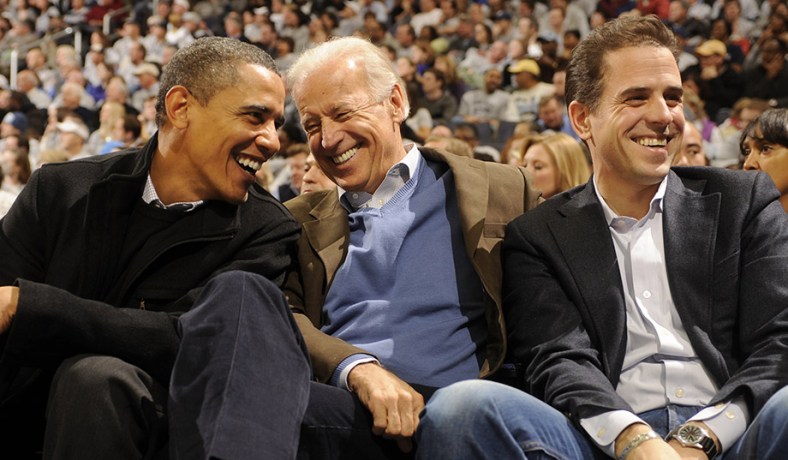
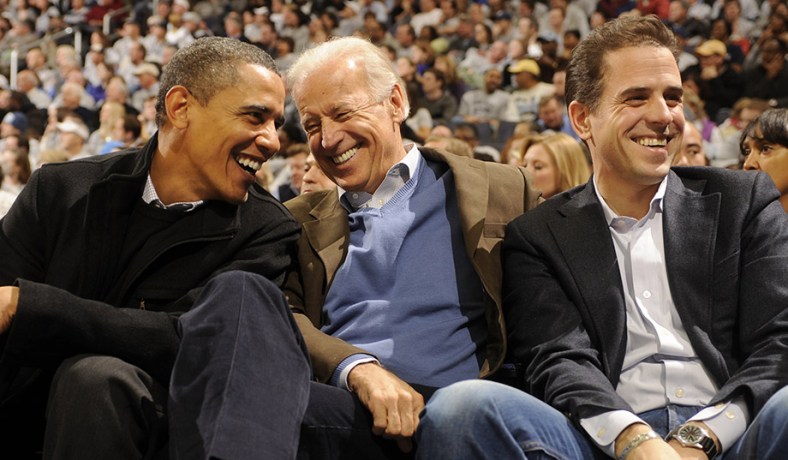 photo
photo
NYP: Joe Biden and John Kerry have been pillars of the Washington establishment for more than 30 years. Biden is one of the most popular politicians in our nation’s capital.
His demeanor, sense of humor, and even his friendly gaffes have allowed him to form close relationships with both Democrats and Republicans. His public image is built around his “Lunch Bucket Joe” persona. As he reminds the American people on regular occasions, he has little wealth to show for his career, despite having reached the vice presidency.
One of his closest political allies in Washington is former senator and former Secretary of State John Kerry. “Lunch Bucket Joe” he ain’t; Kerry is more patrician than earthy. But the two men became close while serving for several decades together in the US Senate. The two “often talked on matters of foreign policy,” says Jules Witcover in his Biden biography.
So their sons going into business together in June 2009 was not exactly a bolt out of the blue.
But with whom their sons cut lucrative deals while the elder two were steering the ship of state is more of a surprise.
What Hunter Biden, the son of America’s vice president, and Christopher Heinz, the stepson of the chairman of the Senate Committee on Foreign Relations (later to be secretary of state), were creating was an international private equity firm. It was anchored by the Heinz family alternative investment fund, Rosemont Capital. The new firm would be populated by political loyalists and positioned to strike profitable deals overseas with foreign governments and officials with whom the US government was negotiating.
Hunter Biden, Vice President Joe Biden’s youngest son, had gone through a series of jobs since graduating from Yale Law School in 1996, including the hedge-fund business.
By the summer of 2009, the 39-year-old Hunter joined forces with the son of another powerful figure in American politics, Chris Heinz. Senator John Heinz of Pennsylvania had tragically died in a 1991 airplane crash when Chris was 18. Chris, his brothers, and his mother inherited a large chunk of the family’s vast ketchup fortune, including a network of investment funds and a Pennsylvania estate, among other properties. In May 1995, his mother, Teresa, married Senator John Kerry of Massachusetts. That same year, Chris graduated from Yale, and then went on to get his MBA from Harvard Business School.
Joining them in the Rosemont venture was Devon Archer, a longtime Heinz and Kerry friend.
The three friends established a series of related LLCs. The trunk of the tree was Rosemont Capital, the alternative investment fund of the Heinz Family Office. Rosemont Farm is the name of the Heinz family’s 90-acre estate outside Fox Chapel, Pennsylvania.
The small fund grew quickly. According to an email revealed as part of a Securities and Exchange Commission investigation, Rosemont described themselves as “a $2.4 billion private equity firm co-owned by Hunter Biden and Chris Heinz,” with Devon Archer as “Managing Partner.”
The partners attached several branches to the Rosemont Capital trunk, including Rosemont Seneca Partners, LLC, Rosemont Seneca Technology Partners, and Rosemont Realty.
Of the various deals in which these Rosemont entities were involved, one of the largest and most troubling concerns was Rosemont Seneca Partners.
Rather than set up shop in New York City, the financial capital of the world, Rosemont Seneca leased space in Washington, DC. They occupied an all-brick building on Wisconsin Avenue, the main thoroughfare of exclusive Georgetown. Their offices would be less than a mile from John and Teresa Kerry’s 23-room Georgetown mansion, and just two miles from both Joe Biden’s office in the White House and his residence at the Naval Observatory.
Over the next seven years, as both Joe Biden and John Kerry negotiated sensitive and high-stakes deals with foreign governments, Rosemont entities secured a series of exclusive deals often with those same foreign governments.
Some of the deals they secured may remain hidden. These Rosemont entities are, after all, within a private equity firm and as such are not required to report or disclose their financial dealings publicly.
Some of their transactions are nevertheless traceable by investigating world capital markets. A troubling pattern emerges from this research, showing how profitable deals were struck with foreign governments on the heels of crucial diplomatic missions carried out by their powerful fathers. Often those foreign entities gained favorable policy actions from the United States government just as the sons were securing favorable financial deals from those same entities.
Nowhere is that more true than in their commercial dealings with Chinese government-backed enterprises.
Rosemont Seneca joined forces in doing business in China with another politically connected consultancy called the Thornton Group. The Massachusetts-based firm is headed by James Bulger, the nephew of the notorious mob hitman James “Whitey” Bulger. Whitey was the leader of the Winter Hill Gang, part of the South Boston mafia. Under indictment for 19 murders, he disappeared. He was later arrested, tried, and convicted.
James Bulger’s father, Whitey’s younger brother, Billy Bulger, serves on the board of directors of the Thornton Group. He was the longtime leader of the Massachusetts state Senate and, with their long overlap by state and by party, a political ally of Massachusetts Senator John Kerry.
Less than a year after opening Rosemont Seneca’s doors, Hunter Biden and Devon Archer were in China, having secured access at the highest levels. Thornton Group’s account of the meeting on their Chinese-language website was telling: Chinese executives “extended their warm welcome” to the “Thornton Group, with its US partner Rosemont Seneca chairman Hunter Biden (second son of the now Vice President Joe Biden).”
The purpose of the meetings was to “explore the possibility of commercial cooperation and opportunity.” Curiously, details about the meeting do not appear on their English-language website.
Also, according to the Thornton Group, the three Americans met with the largest and most powerful government fund leaders in China — even though Rosemont was both new and small.
The timing of this meeting was also curious. It occurred just hours before Hunter Biden’s father, the vice president, met with Chinese President Hu in Washington as part of the Nuclear Security Summit.
There was a second known meeting with many of the same Chinese financial titans in Taiwan in May 2011. For a small firm like Rosemont Seneca with no track record, it was an impressive level of access to China’s largest financial players. And it was just two weeks after Joe Biden had opened up the US-China strategic dialogue with Chinese officials in Washington.
On one of the first days of December 2013, Hunter Biden was jetting across the Pacific Ocean aboard Air Force Two with his father and daughter Finnegan. The vice president was heading to Asia on an extended official trip. Tensions in the region were on the rise.
The American delegation was visiting Japan, China, and South Korea. But it was the visit to China that had the most potential to generate conflict and controversy. The Obama administration had instituted the “Asia Pivot” in its international strategy, shifting attention away from Europe and toward Asia, where China was flexing its muscles.
For Hunter Biden, the trip coincided with a major deal that Rosemont Seneca was striking with the state-owned Bank of China. From his perspective, the timing couldn’t have been better.
Vice President Biden, Hunter Biden and Finnegan arrived to a red carpet and a delegation of Chinese officials. Greeted by Chinese children carrying flowers, the delegation was then whisked to a meeting with Vice President Li Yuanchao and talks with President Xi Jinping.
Hunter and Finnegan Biden joined the vice president for tea with US Ambassador Gary Locke at the Liu Xian Guan Teahouse in the Dongcheng District in Beijing. Where Hunter Biden spent the rest of his time on the trip remains largely a mystery. There are actually more reports of his daughter Finnegan’s activities than his.
What was not reported was the deal that Hunter was securing. Rosemont Seneca Partners had been negotiating an exclusive deal with Chinese officials, which they signed approximately 10 days after Hunter visited China with his father. The most powerful financial institution in China, the government’s Bank of China, was setting up a joint venture with Rosemont Seneca.
The Bank of China is an enormously powerful financial institution. But the Bank of China is very different from the Bank of America. The Bank of China is government-owned, which means that its role as a bank blurs into its role as a tool of the government. The Bank of China provides capital for “China’s economic statecraft,” as scholar James Reilly puts it. Bank loans and deals often occur within the context of a government goal.
Rosemont Seneca and the Bank of China created a $1 billion investment fund called Bohai Harvest RST (BHR), a name that reflected who was involved. Bohai (or Bo Hai), the innermost gulf of the Yellow Sea, was a reference to the Chinese stake in the company. The “RS” referred to Rosemont Seneca. The “T” was Thornton.
The fund enjoyed an unusual and special status in China. BHR touted its “unique Sino-US shareholding structure” and “the global resources and network” that allowed it to secure investment “opportunities.” Funds were backed by the Chinese government.
In short, the Chinese government was literally funding a business that it co-owned along with the sons of two of America’s most powerful decision makers.
The partnership between American princelings and the Chinese government was just a beginning. The actual investment deals that this partnership made were even more problematic. Many of them would have serious national security implications for the United States.
In 2015, BHR joined forces with the automotive subsidiary of the Chinese state-owned military aviation contractor Aviation Industry Corporation of China (AVIC) to buy American “dual-use” parts manufacturer Henniges.
AVIC is a major military contractor in China. It operates “under the direct control of the State Council” and produces a wide array of fighter and bomber aircraft, transports, and drones — primarily designed to compete with the United States.
The company also has a long history of stealing Western technology and applying it to military systems. The year before BHR joined with AVIC, the Wall Street Journal reported that the aviation company had stolen technologies related to the US F-35 stealth fighter and incorporated them in their own stealth fighter, the J-31. AVIC has also been accused of stealing US drone systems and using them to produce their own.
In September 2015, when AVIC bought 51 percent of American precision-parts manufacturer Henniges, the other 49 percent was purchased by the Biden-and-Kerry-linked BHR.
Henniges is recognized as a world leader in anti-vibration technologies in the automotive industry and for its precise, state-of-the-art manufacturing capabilities. Anti-vibration technologies are considered “dual-use” because they can have a military application, according to both the State Department and Department of Commerce.
The technology is also on the restricted Commerce Control List used by the federal government to limit the exports of certain technologies. For that reason, the Henniges deal would require the approval of the Committee on Foreign Investment in the United States (CFIUS), which reviews sensitive business transactions that may have a national security implication.
According to BHR internal documents, the Henniges deal included “arduous and often-times challenging negotiations.” The CFIUS review in 2015 included representatives from numerous government agencies including John Kerry’s State Department.
The deal was approved in 2015.
Excerpted with permission from “Secret Empires: How the American Political Class Hides Corruption and Enriches Family and Friends,” by Peter Schweizer, published by Harper Collins. The book goes on sale March 20.
 Electronic attack J-16
Electronic attack J-16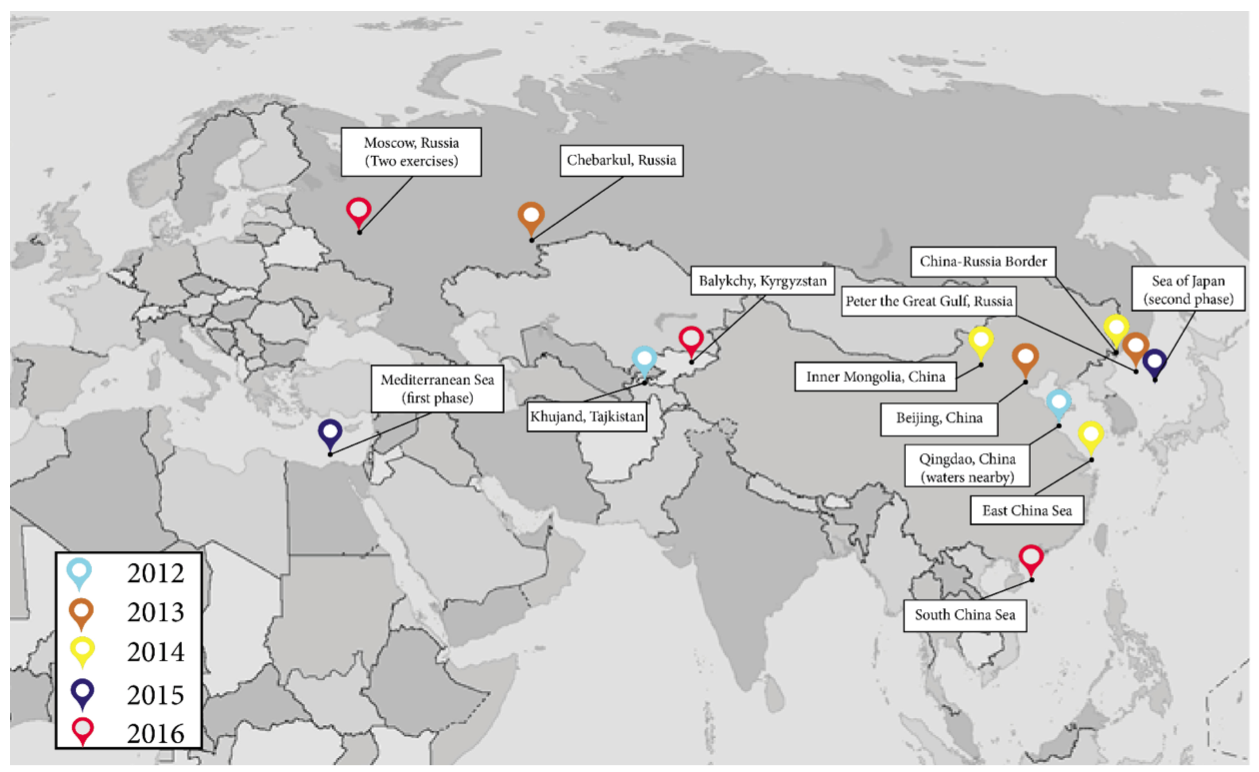 Before Russia and China began their recent series of bilateral exercises, the key tie between Moscow and Beijing was arms sales and military technology cooperation — totaling about $26 billion from 1992 to 2006 — according to estimates cited in the report.
Before Russia and China began their recent series of bilateral exercises, the key tie between Moscow and Beijing was arms sales and military technology cooperation — totaling about $26 billion from 1992 to 2006 — according to estimates cited in the report.