For that matter, most of the mailboxes for all of government, the same is true including those in Congress. I have called at least 9 myself several times this past week. I was only able to speak to a real person in Congressman Ken Buck’s office, her name was Monica and she had some factual interesting things to say. I made a couple of requests and like wow….she said she would call me back…..SHE DID. Mission complete with my request.
Anyway….from Jim Geraghty at National Review:
This morning I heard from a longtime NR reader who spent years in Afghanistan working for a defense contractor. This reader’s company worked on the construction of camps and garrisons, parts of bases at Bagram and Kandahar, as well as several government buildings for the Afghan military and police.
“We directly employed thousands of Afghans,” he told me. “Their lives are in danger of retaliation by the Taliban because they helped the American military. Recognizing this, on August 2nd the U.S. government created another classification of asylum/visa processing called ‘Priority 2’.”
The announcement of the Priority 2 program can be found here. An unidentified senior state department official stated, “Many thousands of Afghans and their immediate family members are at risk due to these U.S. affiliations and are not eligible for a Special Immigrant Visa because either they did not have qualifying employment, or they have not met the time-in-service requirement to become eligible; however, they may be eligible for a P-2 referral, and thus, to the U.S. Refugee Admissions Program.” Priority 2 covers Afghans who worked with U.S. government-funded programs, as well as those who were employed in Afghanistan by a U.S.-based non-governmental or media organization that does not require U.S. government funding.
My reader said, “I’ve been busy the last week submitting referrals to the State Department on behalf of Afghans and their families who worked for us and whose very lives have been threatened. The submission is through email to a dedicated inbox at State. We began receiving messages that the inbox is full and that we should try later. This has been going on for half a day now.”
He shared with me an automatic reply e-mail that declared, “The recipient’s mailbox is full and can’t accept messages now. Please try resending your message later, or contact the recipient directly.”
My reader is furious. “Lives are in danger. Evacuations are in chaos — don’t believe a damn word any American spokesman says – they’re either making it up or they are lying. And the damn system for prioritizing our Afghan workers is a cluster because the DOS can’t manage a damn email inbox! I have never been so disappointed and angry at my government than today. It is maddening.”
My reader has contacted one of his senators – a Republican – but had to leave a message on the constituent line.
I rest my case on this fact…sadly. But to continue on.
All week long, officials in the Biden administration have told us they don’t know how many Americans are stuck in various locations around Afghanistan. Only part of that is true. They know how many Americans are in Afghanistan, that is a fact…where they may be at any particular moment could be true. Understand this: anyone from the United States that travels to Afghanistan must get a visa and ensure they have a passport. Both of those things are permanent records and are maintained at the State Department in a database. As simple keyboard inquiry is all that is needed. Going deeper on the matter, is your passport and boarding pass. The TSA scans both. And in most airports with international travel gates, those two documents at the time of travel are merged. For details on the chipped passports, e-Passport or biometric passports, go here.
Is there a chance the actual database may be off on the actual number? Sure based on the traveler’s movement, but you can be assured our State Department knows the number with at least above 90% accuracy. The reason the ‘don’t know answer’ is given is because it would admit we cannot possibly get Americans out of likely peril in Afghanistan within the Biden timeline.
Once Americans arrive in Afghanistan, they are to register with the US Embassy so officials there know who is in country and why. Well, that too may now be a big problem as we evacuated the embassy and removed the flag that that database still is held by some official or was likely uploaded to a cloud system.
 Building on the right is the US Embassy, Kabul – source
Building on the right is the US Embassy, Kabul – source
Now the Biden administration is telling us that anyone that is in Afghanistan and wants to leave, we will get them out. Really? ‘who wants to leave’? Who the hell would want to stay? C’mon are we that stupid?
Below is a map published by al Jazeera. While I have no use for this media source…at least it does given some timeline of the Taliban takeover of Afghanistan as of August 15.
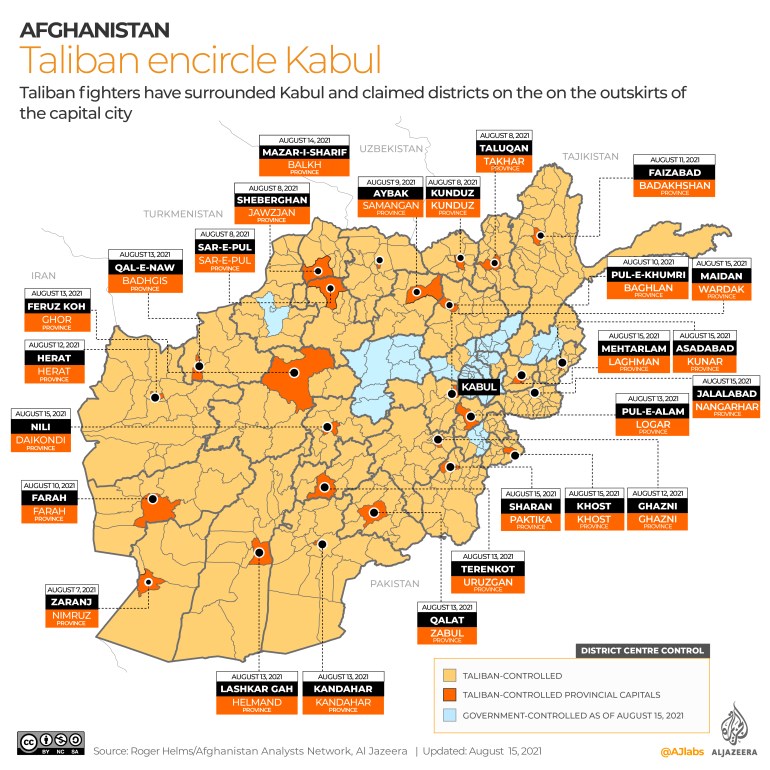
The Taliban has captured 26 of the 34 provincial capitals in Afghanistan, with more than half of them falling to the armed group in less than two weeks.
The armed group is now at the gate of the capital Kabul after taking major cities such as Herat, Kandahar and Mazar-i-Sharif.
The group had already gained vast parts of rural Afghanistan since launching a series of offensives in May to coincide with the start of the final withdrawal of US-led foreign forces after 20 years of war.
***
Many in the diplomatic staff at our Kabul embassy knew precisely what the conditions on the ground were as far back as at least June. As it was getting more threatening, many of their warnings went unheard so they wrote a letter of dissent in July. Still our Secretary of State ignored the level of the threat and hence the Biden White House ignored all the same but slowly began a process.
WASHINGTON — Last month, two dozen diplomats at the U.S. Embassy in Kabul, Afghanistan, warned about the possibility of a Taliban takeover and urged the State Department to begin an airlift operation in a dissent cable sent to Secretary of State Antony Blinken, according to a source familiar with the situation.
The July 13 cable called on Washington to be firm and direct in describing atrocities by the Taliban, the source said. NBC News has not seen the cable.
A dissent channel cable is a confidential, formal way for State Department diplomats to voice disagreement or concern about U.S. policies without fear of retribution.
The cable was first Thursday by The Wall Street Journal.
The day after the cable was sent, the Biden administration announced Operation Allies Refuge, a program to transport Afghans and their families at risk of retaliation from the Taliban for their work with U.S. troops. State Department leaders sent a response a few days later thanking the writers of the dissent cable and describing the task force set up to facilitate evacuations of Special Immigrant Visa applicants, the source said.
“We value constructive internal dissent. It’s patriotic. It’s protected. And it makes us more effective,” State Department spokesman Ned Price said Thursday. “Maintaining the channel’s integrity and the notion of disciplined dissent is key to that revitalization. It’s why we keep communication strictly between the Department’s leadership and the authors of the dissent messages and why we don’t comment publicly on the substance of messages or the replies, regardless of the classification.”
Once the Taliban began the march to take over capitols and provinces, all actions needed to be launched. Nah…not until August did that even begin. Get the picture?









