Hillary Clinton Says the Women’s Marches Were ‘Awe-Inspiring’
Clinton, 69, who was the first-ever female presidential nominee for a major political party and won the popular vote, tweeted about the peaceful rallies on Saturday, January 21. “Thanks for standing, speaking & marching for our values @womensmarch. Important as ever. I truly believe we’re always Stronger Together,” she wrote to her more than 12 million followers. “Scrolling through images of the #womensmarch is awe-inspiring. Hope it brought joy to others as it did to me.”
Protesters walk during the Women’s March on Washington, with the U.S. Capitol in the background, on Jan. 21, 2017. Mario Tama/Getty Images
Hillary ClintonVerified account
@HillaryClinton 18 hours agoScrolling through images of the
#womensmarchis awe-inspiring. Hope it brought joy to others as it did to me.
**** Some of her closets political allies also echoed the same sentiments. Read more here.
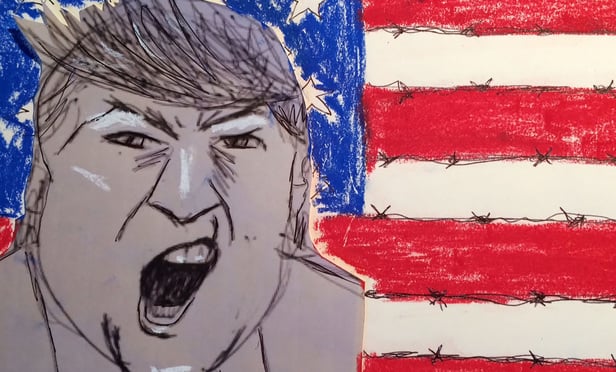
Related reading: Opposing Trump Admin, When Documents Matter
Hillary Clinton plots her next move
The Democrat has been studying election presentations, including reports on where she underperformed.
Politico: LITTLE ROCK, Ark. — In a series of private meetings and phone calls at their home in Chappaqua, in New York City and in Washington, Bill and Hillary Clinton are slowly starting to puzzle through their political future, according to over a dozen people who have spoken directly with them, and nearly two dozen other Democrats who have been briefed on their thinking.
The recently vanquished candidate has told some associates she’s looking at a spring timeline for mapping out some of her next political steps. Still recovering from her stunning loss, a political return is far from the top of Clinton’s mind, with much of her planning focused around the kinds of projects she wants to take on outside the partisan arena, like writing or pushing specific policy initiatives.
Just as the Democratic Party feels its way through a landscape without either Clinton looming over its future for the first time in nearly a quarter century, Clinton herself is working through the uncertainty surrounding how to best return to the fold.
There have been no conversations about starting her own political group but Clinton has spoken with leaders of emerging Democratic-leaning organizations about their work, and has discussed possible opportunities to work with Organizing For Action, former President Barack Obama’s initiative. Among the potential political priorities she has mentioned to associates are building pipelines for young party leaders to rise and ensuring that a reconstructed Democratic National Committee functions as an effective hub that works seamlessly with other party campaign wings.
The one-time secretary of state has been in contact with a range of ex-aides, studying presentations as she tries to better understand the forces behind her shocking November defeat.
Included among those presentations has been a series of reports pulled together by her former campaign manager Robby Mook and members of his team, who have updated her not just on data and polling errors, but also on results among segments of the electorate where she underperformed, according to Democrats familiar with the project.
“She understands that a forensic exam of the campaign is necessary, not only for her, but for the party and other electeds, and for the investors in the campaign,” said a close Hillary Clinton friend in Washington who, like several others, declined to speak on the record because their conversations with one or both Clintons were private. “People want to know that their investment was treated with respect, but that their mistakes wouldn’t be repeated.”
For his part, Bill Clinton has spent considerable time poring over precinct-level results from the 2016 race while meeting with and calling longtime friends to rail against FBI Director James Comey’s late campaign intervention and Russia’s involvement, say a handful of Democrats who have spoken with him.
“Many Democratic politicians have been personally influenced or share direct ties to President Clinton, Secretary Clinton, or both. That history goes back decades,” said Mack McLarty, Bill Clinton’s first White House chief of staff and a lifelong friend, predicting their eventual return to the scene. “And, despite the grave disappointment, resilience is in the Clintons’ DNA. So, while I certainly don’t expect to see them trying to assert their authority, I think there will be natural and welcome opportunities for them to engage.”
Wary of the complex political moment as Donald Trump assumes the presidency and supporters of Bernie Sanders assert themselves more forcefully within the Democratic Party, however, the Clintons have been letting the political discussions come to them, rarely bringing it up unprompted in their conversations, and for the moment focusing more on other projects.
Bill Clinton, for example, has dived back into his work with the Clinton Foundation, while Hillary Clinton — spotted recently resuming her social life on Broadway and at trendy dinners in New York and Washington — is considering doing some writing.
For weeks leading up to Trump’s swearing in, the constant refrain among friends and former aides who are struggling with the question of their next political step has been, “Let’s get through the inauguration first.” The Clintons have been careful not to step into the party-shaping territory now occupied by Obama as the most recent Democratic president. And that posture is unlikely to change until at least late February, as the couple studiously stays away from a race for the DNC chairmanship that is widely seen as a Clinton-Sanders proxy fight.
Still, party leaders and friends alike expect them to jump back into the political fundraising and campaigning circuit in some form by the 2018 midterms — and perhaps in time for 2017’s two gubernatorial elections in New Jersey and Virginia. A number of Hillary Clinton’s most prominent 2016 supporters are likely to need the help soon, including Florida Sen. Bill Nelson, Miami Beach Mayor Philip Levine and Orlando attorney John Morgan — both likely gubernatorial candidates in 2018 — as well as Ohio Sen. Sherrod Brown, Pennsylvania Sen. Bob Casey, and New Jersey governor hopeful Phil Murphy.
“I would be surprised [to see Bill Clinton step away from politics] only because he has so many friends who are still involved, who he’s worked with for so many years,” said Skip Rutherford, the dean of the University of Arkansas’ Clinton School of Public Service and the founding president of the Clinton Foundation. “Many of the people who are involved in the political world got their starts in the Clinton world, so there’s a whole base of people who are connected to both Clintons.”
“If someone they knew was running for the Senate or the Statehouse or City Hall, it would be out of character for them not to be supportive,” added McLarty.
But before that lies a set of more immediate concerns that includes determining the fate of Hillary Clinton’s campaign email list and figuring out which new Democratic efforts — if any — to support.
“On a personal level, I lost a race in 2014 and it was on a much, much smaller scale than what she lost. But I know there’s a time of healing that has to happen. So on a personal level I know she just needs to get away for a while,” said former Democratic Arkansas Senator Mark Pryor.
There’s no obvious model for the pair to follow in the months and years ahead: Bill Clinton has been uniquely involved in electoral politics in his post-presidency, and recent losing nominees have either returned to their Senate day jobs — like John Kerry and John McCain — or continued to flirt with another presidential run — like Mitt Romney.
But neither Clinton is likely to run for office again, never mind the New York City mayoral rumors that Hillary Clinton’s friends routinely laugh off.
“The Democratic Party does need new blood, new faces, and I don’t think Bill or Hillary Clinton would ever want to get back and run for anything — I don’t think a team of mules could drag them to do that,” said Pryor.
Their current political standing within the party is somewhat precarious, defined by a mixture of admiration for the family balanced with frustration, and in some cases, anger. Many supporters of Sanders, for instance, are still licking their wounds from the bruising primary, and have seized the post-election moment to gain power in local Democratic party committees across the country — often by dismissing the more establishment-oriented Clintonian way of doing business.
And some Clinton supporters in the states are irritated by the lack of a formal, public-facing autopsy from her campaign since the absence of even a preliminary acknowledgment of fault has made it harder for the party to raise money on a local level — donors feel burned.
“There’s huge annoyance in the states,” said one swing-state party leader. “People assume they’re done, and they’re more powerful if they take that back seat. [For now] there’s short-term fatigue, but it will settle into respect.”
Clinton allies have been careful not to engage in direct fights with detractors that could turn into referenda on the family’s legacy, but national leaders acknowledge some lingering post-election tension.
“The problem with circular firing squads is everyone gets hit. I don’t think there’s any room in the party right now for a circular firing squad. The party has a long way to go in order to regain its proverbial political footing across the country,” said interim DNC chair Donna Brazile — a Bill Clinton campaign advisor in 1992 and 1996 — adding that Hillary Clinton’s victory over Trump in the popular vote underscores the potential use of promoting her as a surrogate for the next crop of candidates.
Not relying on Clinton, she said, would be “like taking your running back and placing them on the sideline just because you lost the season. As Democrats, we need to keep everyone on the roster — to recruit, raise funds, and more — even if they are no longer part of the starting lineup.”
The ongoing competition to lead the DNC makes the situation all the more delicate as the couple monitors the situation from New York: the candidates for chair rarely mention either Clinton, sensing a level of impatience with them among voting members of the committee and elected officials who want to see a younger generation of Democrats take power.
“New ideas and new approaches and new direction, that’s really needed right now,” said Ohio Rep. Tim Ryan, a prominent Clinton supporter during the campaign who challenged Nancy Pelosi’s House leadership position after the election. Ryan said the Clintons would remain useful to the party moving forward, but “it’s just the natural cycle of political parties, and I think Republicans have done a better job than we have in trying to engage young voices to get into the mix.”
For the moment, the Clintons’ closest political allies are counseling a “wait-and-see” approach when it comes to the nature of their public-facing role. Well acquainted with fluctuating public perceptions after three decades of sine curve-style approval ratings, they are watching Trump’s numbers closely, aware that their own popularity could rebound — especially when the Trump administration runs up against popular pieces of Bill Clinton’s White House and Hillary Clinton’s State Department legacies.
Whatever role they choose, however, their shadow will continue to loom over the party’s infrastructure. A number of the major left-leaning organizations that are relaunching in opposition to Trump are run by operatives who are closely associated with the Clintons, including the Priorities USA super PAC run by Guy Cecil, the Center for American Progress under Neera Tanden, and the network of liberal groups steered by David Brock.
Outside Washington, meanwhile, Democrats are considering ways Clinton could emerge as a prominent potential ally for local-level officials. For example, a major problem faced by Democratic state parties in red states is the reluctance of national party leaders to travel and help them raise money, due to those state’s lack of relevance in national races. But such a fundraising role would be natural for Clinton, said multiple Democrats who are piecing together the party’s map ahead.
“They believe in the party and they want to leave this party in a better position than where they found it, and I think [they and the Obamas] have an obligation to the party, because the party has given them so much,” said South Carolina Chairman Jaime Harrison, a candidate to lead the national committee. “If I’m DNC chair, that’s one of the first calls I’m going to make, to ask them to play that ambassador role.”
Colorado Gov. John Hickenlooper, who was considered for Clinton’s running-mate position last summer, said Hillary Clinton — like her husband — will have much to offer as a party elder, a sentiment repeated by up-and-coming liberals and veteran moderates alike. “Thirty-four states have both their House and Senate in Republican hands, so there’s a larger discussion [to be had]. It involves not just policy, but it involves funding, and she’s going to be a respected voice who’s been in just about every situation imaginable.”
So while the Clintons’ short-term priorities remain apolitical, their allies and the people surrounding them are skeptical that can last too long.
Predicted former Pennsylvania governor and DNC chair Ed Rendell, a longtime family friend: “I’m certain Trump will screw up enough that by the fall of ’18, Hillary’s numbers will be way up again.”


 The Navy Memorial stage will feature leaders from every grassroots movement — immigrant rights, labor, environmental justice, women’s rights, Movement for Black Lives, LGBTQ equality, anti-war and others — as well as progressive leaders from the whole spectrum of faith communities. Artists, musicians and DJs will be performing throughout the day.
The Navy Memorial stage will feature leaders from every grassroots movement — immigrant rights, labor, environmental justice, women’s rights, Movement for Black Lives, LGBTQ equality, anti-war and others — as well as progressive leaders from the whole spectrum of faith communities. Artists, musicians and DJs will be performing throughout the day.