Ex-CIA engineer charged with massive leak to WikiLeaks
A former CIA computer engineer has been indicted on charges he masterminded what appears to be the largest leak of classified information in the spy agency’s history.
Joshua Schulte, 29, was charged in a new grand jury indictment with providing WikiLeaks with a massive trove of U.S. government hacking tools that the online publisher posted in March 2017, the Justice Department announced on Monday.
Schulte was previously facing child pornography charges in federal court in New York, but the indictment broadens the case to accuse him of illegally gathering classified information, damaging CIA computers, lying to investigators and numerous other offenses.
In January, attorneys involved in the child porn case revealed in court that Schulte was the target of a major investigation into WikiLeaks’ release of a CIA collection known as “Vault 7.”
The Justice Department’snews release announcing Schulte’s indictment does not mention WikiLeaks by name, signaling that it has not been charged in the case. There was no mention of any other individuals being charged.
Attorneys for Schulte did not immediately respond to requests for comment.
The new charges make Schulte the fourth individual to face charges related to classified leaks since President Donald Trump took office and vowed a crackdown on leaks.
Last June, a National Security Agency contractor, Reality Winner, was arrested on charges of leaking to the online publication The Intercept a top secret report on the techniques that Russian government agents allegedly used to target computers of state election officials. She has pleaded not guilty and has been held without bail. Her trial is set for October.
In March, an FBI agent based in Minneapolis, Terry Albury, was charged with a leak to The Intercept of the FBI’s procedures for handling informants. He was also accused of retaining classified information at his home. He pleaded guilty to both charges and is free awaiting sentencing.
Earlier this month, the longtime head of security for the Senate Intelligence Committee, James Wolfe, was indicted on three felony counts of lying during the course of an FBI investigation into unauthorized disclosures of classified information. He was not charged with any leaks, but the indictment contends that he provided confidential committee information to at least one reporter. Wolfe pleaded not guilty to the charges last week. No trial date has been set.
Criminal complaint found here.
*** More background detail:
Joshua Adam Schulte, the former CIA worker suspected of passing the agency’s hacking secrets to WikiLeaks, previously posted the source code for an internal CIA tool to his account on the public code-sharing site GitHub, The Daily Beast has learned.
That potential red flag was apparently missed by the spy agency just months after Edward Snowden walked out of the National Security Agency with a thumb drive of secrets in 2013. A spokesman for the CIA declined to comment.
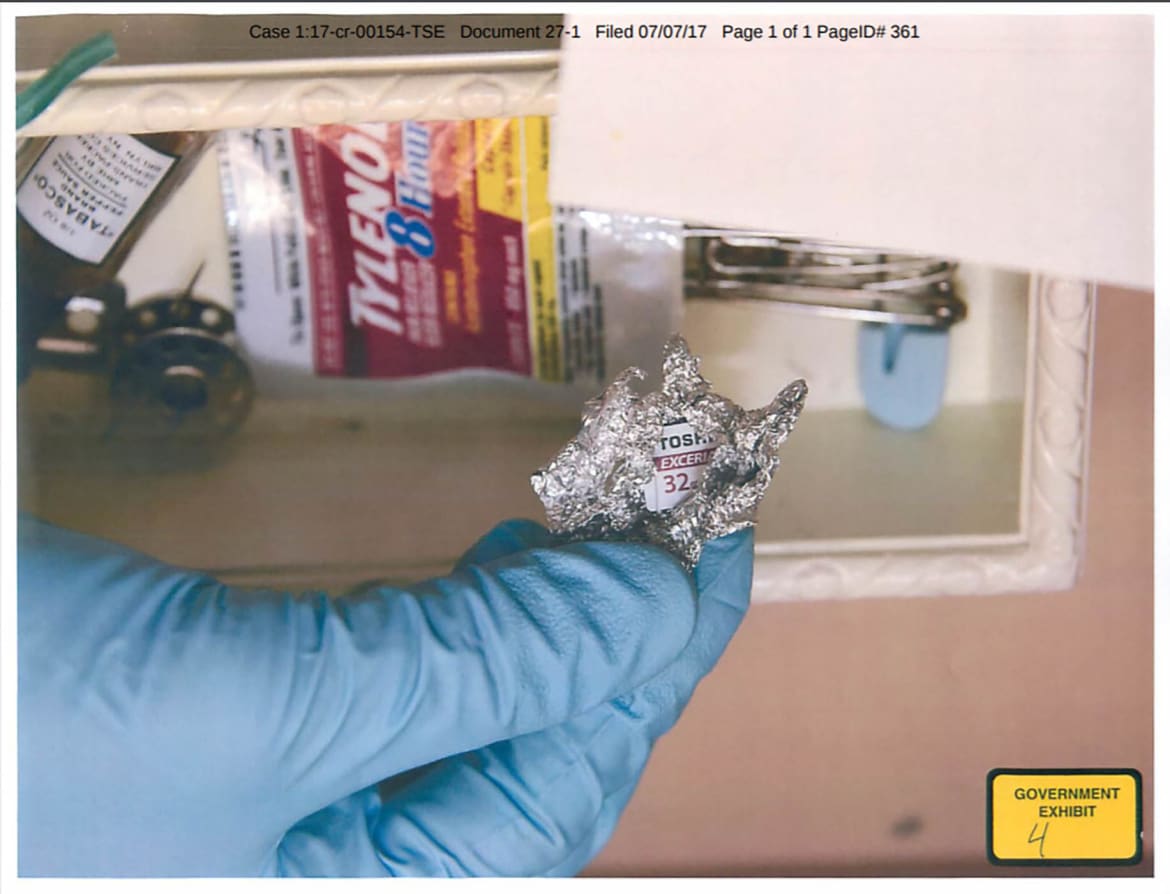
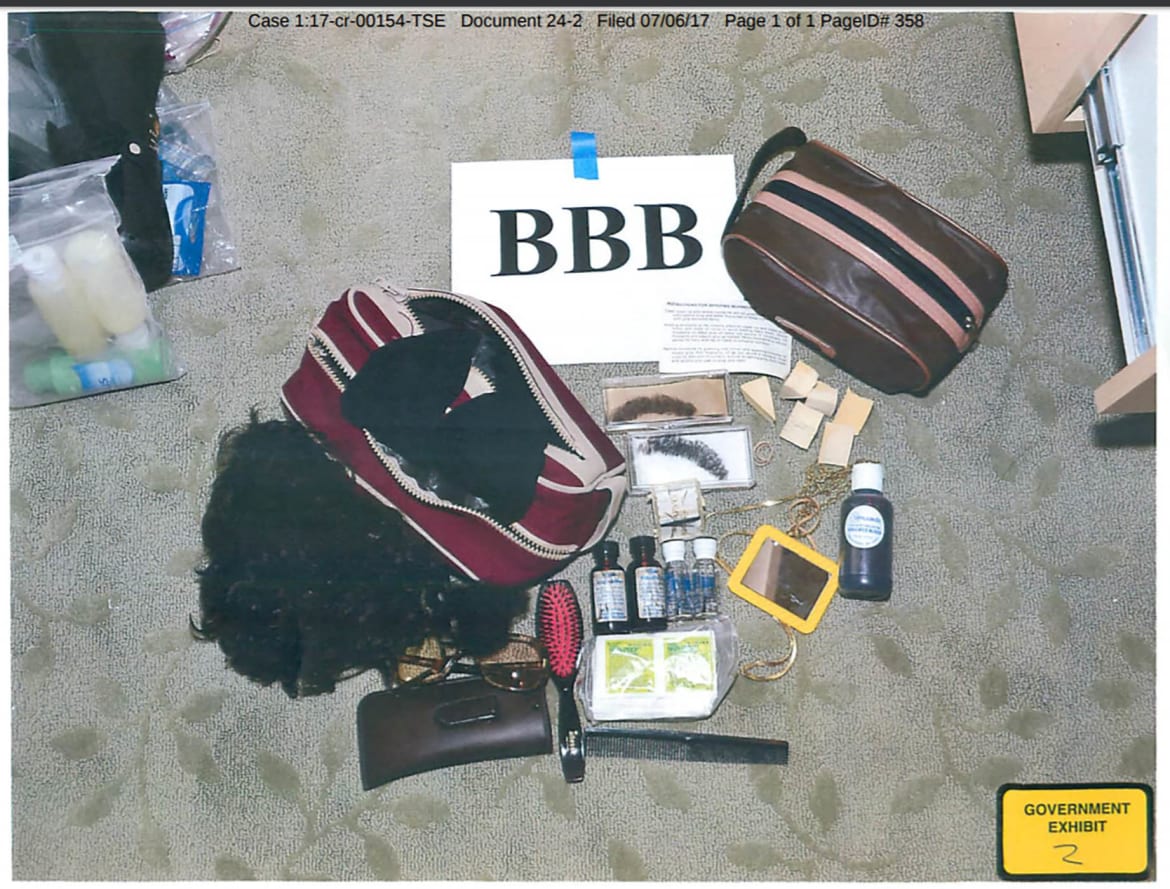
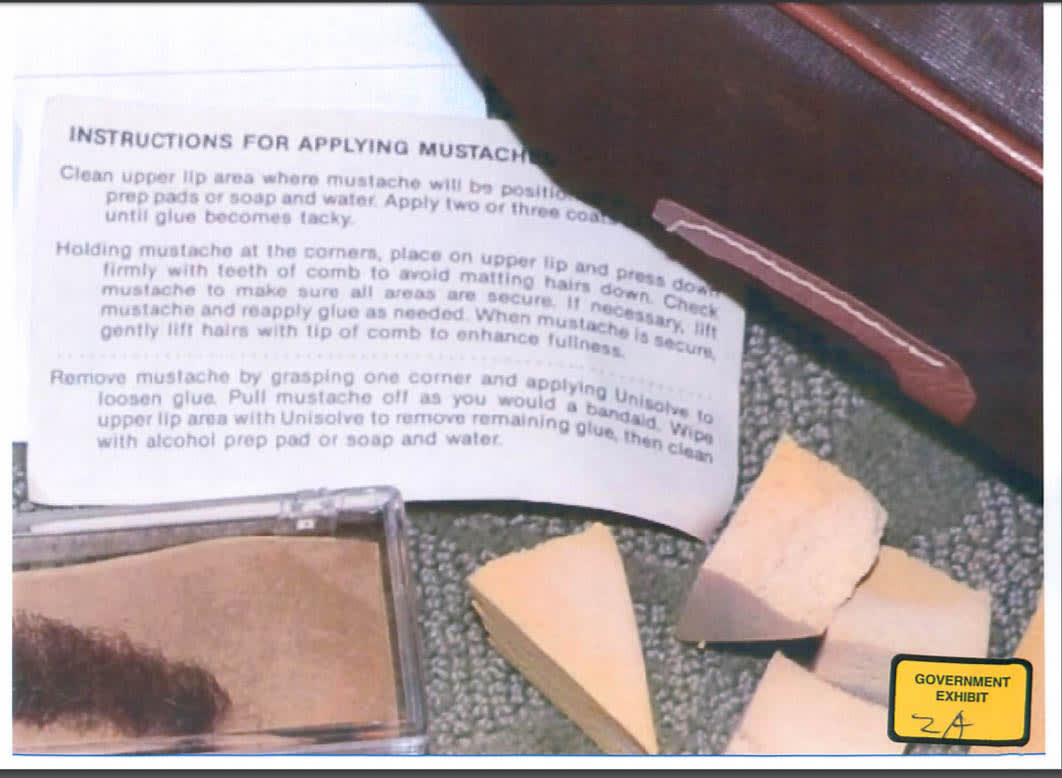
Schulte, 29, worked at the CIA from 2010 to 2016. He was raided by the FBI on March 23, 2017, roughly two weeks after Julian Assange began releasing 8,000 CIA files under the rubric “Vault 7.” The files had been copied from an internal agency wiki sometime in 2016, and contained documentation and some source code for the hacking tools used by the CIA’s intrusion teams when conducting foreign surveillance.
When FBI agents examined Schulte’s hard drive, they found only a single classified document, but allegedly turned up 10,000 images of child pornography. Today Schulte is being held in a federal holding facility in Manhattan on one count each of possessing, receiving, and transporting child porn. He has not been charged with the Vault 7 leak, but, in January the FBI was still investigating him as the suspect.
Until now it’s been unclear how the FBI became suspicious of Schulte in the first place. In a statement to The Washington Post, which broke the story of the arrest, Schulte said the bureau went after him because he’d reported managerial incompetence to the CIA’s inspector general and then left the agency in 2016. “Due to these unfortunate coincidences, the FBI ultimately made the snap judgment that I was guilty of the leaks and targeted me.”
Prosecutor Matthew Larouch said at a January court appearance that “the government immediately had enough evidence to establish that [Schulte] was a target of that investigation,” but didn’t elaborate on the evidence.
Schulte has hosted 11 of his own coding projects on GitHub over the years. In the fall of 2013, he uploaded a robust software development tool he’d developed called OSB Project Wizard, described this way: “Create all types of projects following OSB build guidelines.” The OSB abbreviation went unexplained.


 In 2016, Women Vote raised almost $38 million and spent just over that. In 2018, they are in the
In 2016, Women Vote raised almost $38 million and spent just over that. In 2018, they are in the