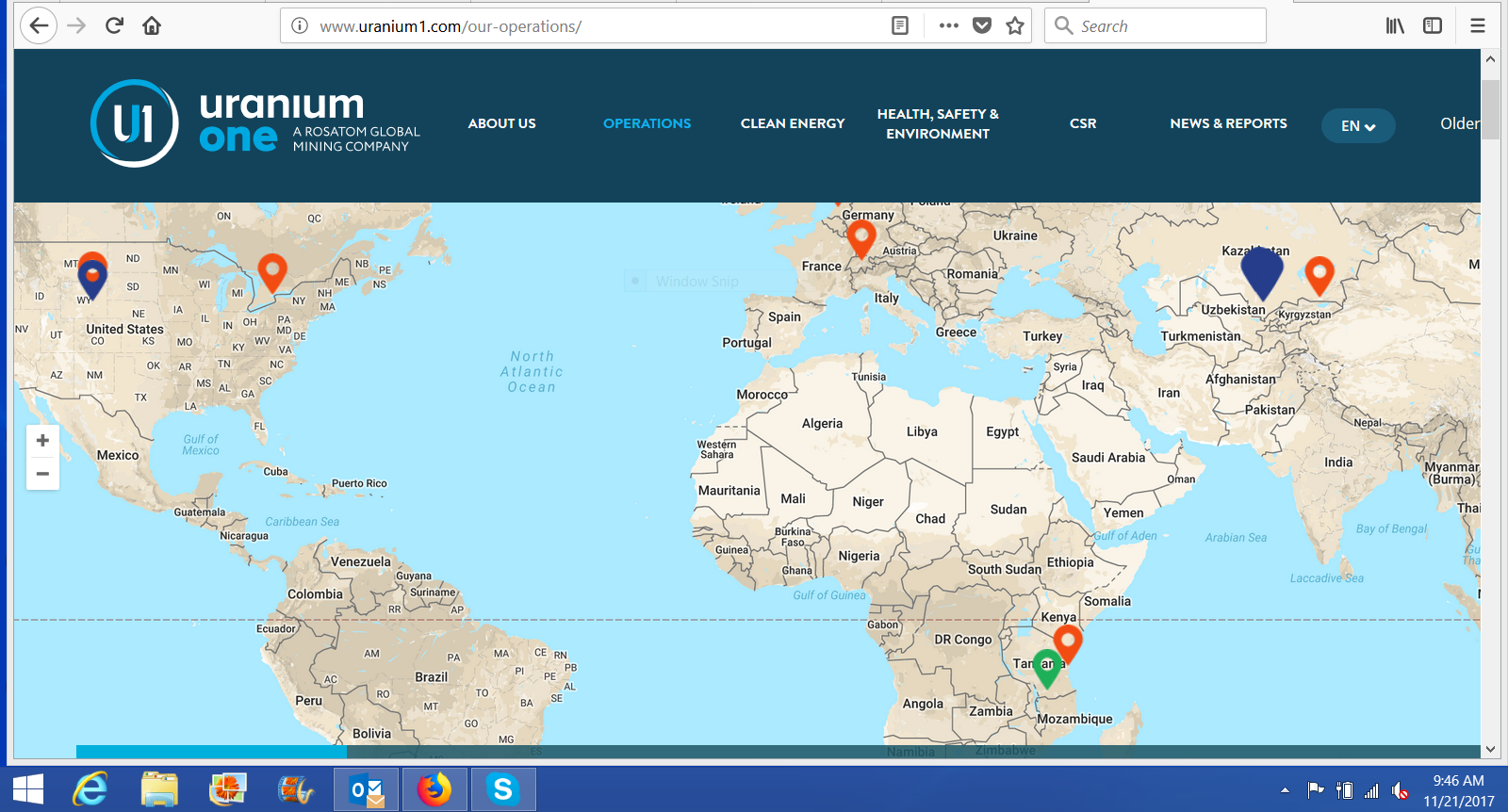
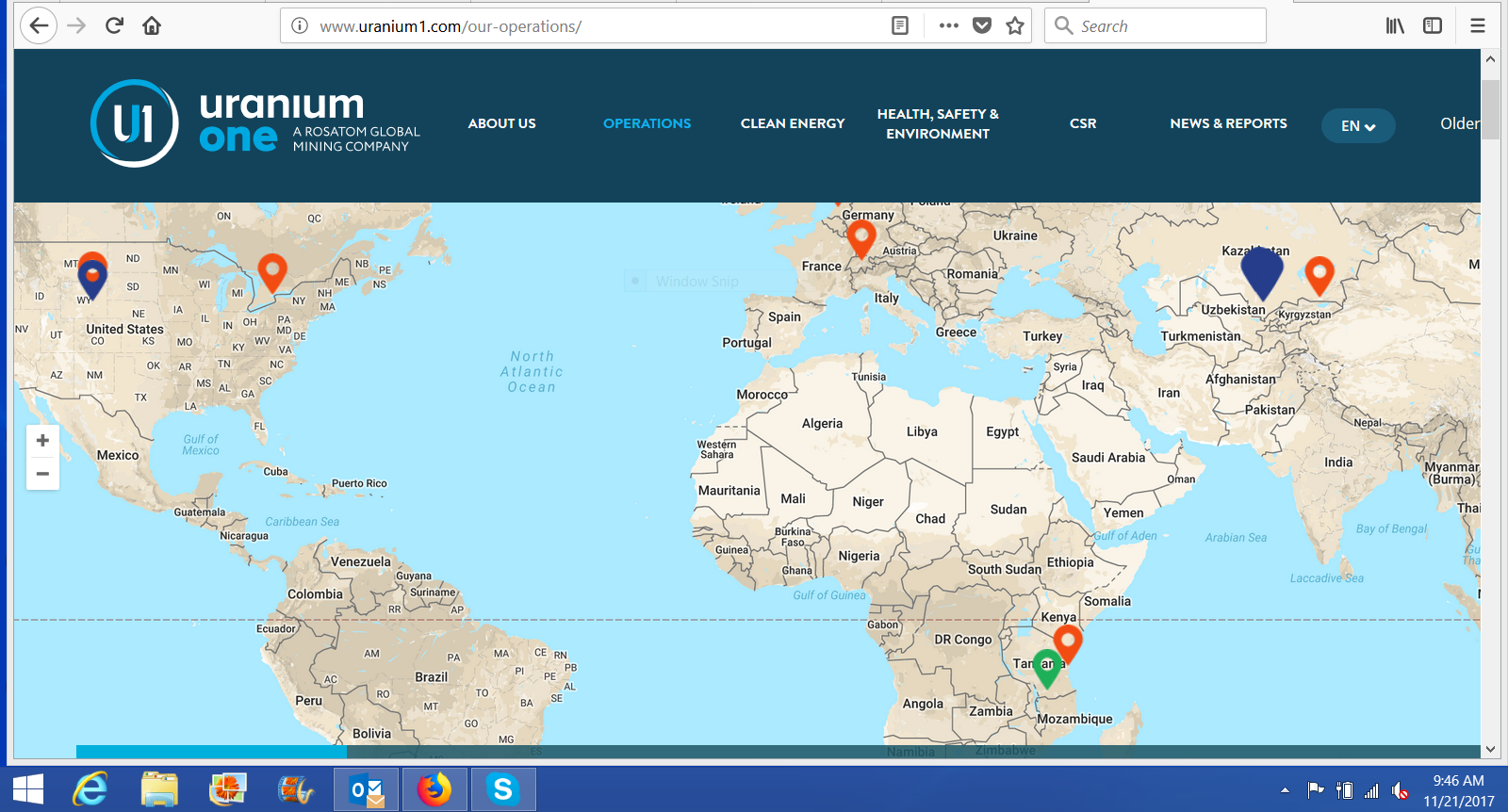
Our Operations
Uranium One is engaged through its subsidiaries and joint ventures in uranium production, and in the exploration and development of uranium properties, in Kazakhstan, the United States, Tanzania and elsewhere. Uranium One is focused on low cost and low technical risk operations, with existing, near and medium-term production visibility in some of the world’s largest uranium resource jurisdictions.
Uranium One is a joint venture partner with JSC NAC Kazatomprom, the Kazakhstan state-owned atomic energy company, in six major producing uranium mines in Kazakhstan – Akdala, South Inkai, Karatau, Akbastau, Zarechnoye and Kharasan. The company also operates the Willow Creek uranium mine in Wyoming, and is the operator of, and owns a 13.9 percent interest in, the Mkuju River uranium development project in Tanzania.
Uranium One’s revenues are largely derived from the sale of uranium concentrates. The company sells its uranium to major nuclear utilities in Russia, Europe, North America, South America, Middle East and Asia.
***
This was an internal coup advanced by the Obama administration. What is worse, where are those Hillary, State Department of CFIUS or White House related emails?
***
William Campbell, the FBI informant, documented for his FBI handlers the first illegal activity by Russians nuclear industry officials in fall 2009, nearly a entire year before the Russian state-owned Rosatom nuclear firm won Obama administration approval for the Uranium One deal, the memos show.
Evidence gathered by an FBI undercover informant conflicts with several media reports as well as statements by Justice officials concerning the connections between a Russian nuclear bribery case and the Obama administration’s approval of the sale of uranium One to Russia’s state-owned Rosatom nuclear company. More here.
***  photo
photo
During Campbell’s time working as a confidential informant, he was required by the Russians to launder large sums of money to financial institutions in Cyprus, Latvia and Seychelles. With Campbell’s help the FBI uncovered an extensive money Russian nuclear money laundering apparatus and Campbell was working solo. He was required to launder money, from his own salary, on particular days and times when Russian money handlers would be working at the banks. If he missed a scheduled pay time for any reason his Russian counterparts would threaten him, he told his attorney. He was also required on many occasions to deliver cash directly to those who were being paid off, most of which he recorded on hidden cameras for the FBI.
It didn’t end there. In order to keep his cover he spent many nights with his Russian counterparts drinking, collecting information and more importantly gaining their trust. He was in his early 60s and his once unblemished driving record ended with a DUI in 2008 and two other reckless driving charges in 2010 and 2012, said Toensing, who noted they were all misdemeanors.
THE PLAYERS
The cast of characters deep within the Russian nuclear agency also included another American businessman named Rod Fisk, whose company Transportation Logistics International, also known as TLI, was the primary transport company for Russian enriched uranium sold to the United States.
Fisk passed away in 2011, and his Vice President Daren Condrey replaced him. In 2015, Daren Condrey, of Maryland, pleaded guilty to conspiring to violate the Foreign Corrupt Practices Act (FCPA) and conspiring to commit wire fraud, according to the DOJ.
Adding to the colorful array of Russian criminals the FBI was watching, was a Russian national named Vadim Mikerin. He was then a top official of the Russian nuclear arms subsidiary Tenex. Mikerin, who had close ties to elite members of the Kremlin, and who bragged in emails and documents about his families connections to current Russian President Vladimir Putin, would later become president of Tenam, the American subsidiary that began operations in 2010, according to the contract. Boris Rubizhevsky, another Russian national from New Jersey, who was president of the security firm NEXGEN Security, also pleaded guilty in 2015, to conspiracy to commit money laundering. He served as a consultant to TENAM and to Mikerin. He was sentenced to prison last week along with three years of supervised release and a $26,500 fine, according to a recent Reuters report.
Mikerin was eventually arrested for a racketeering scheme that dated back to 2004, and included fraud, extortion and money laundering. But he only plead guilty to money-laundering. He was sentenced to 48 months in prison in December 2015. More here.
 Vadim Mikerin (image from flickr.com by Tenam USA) / Flickr
Vadim Mikerin (image from flickr.com by Tenam USA) / Flickr
Here are five revelations from those documents reviewed by The Hill:
Russia saw its purchase of Uranium One as part of a strategy to dominate global uranium markets, including making the United States more dependent on Moscow’s nuclear fuel.
Documents the informant gave the FBI clearly show that the purchase of Uranium One was seen by Russia and its American consultants as one tool in a strategy to “control” the uranium market worldwide. In the United States, that strategy focused on securing billions of new uranium contracts to create a new reliance on Russian nuclear fuel just as the Cold War-era Megatons to Megawatts program was ending.
Uranium One did export some of its U.S. uranium ore.
News organizations, including The Washington Post, continue to report none of Uranium One’s product left the U.S. after Russia took control. In fact, the Nuclear Regulatory Commission (NRC) approved an export license for a third party trucking firm to export Uranium One ore to Canada for enrichment, and that some of that uranium ended up in Europe, NRC memos show. Uranium One itself admits that as much as 25 percent of the uranium it exported to Canada ended up with European or Asian clients through what is know in the industry as “book transfers.”
The FBI informant Douglas Campbell does have information to share with Congress about Rosatom’s Uranium One purchase.
Justice officials have suggested in recent stories that Campbell has little on Uranium One because his work forced on nuclear bribery involving a different Rosatom subsidiary. While it’s true Campbell’s undercover work focused on criminality inside the Rosatom subsidiary Tenex, he did gather extensive documents about Rosatom’s efforts to win approval to buy Uranium One.
The FBI did have evidence that Rosatom officials were engaged in criminality well before the Obama administration approved Rosatom’s purchase of Uranium One.
Evidence that a foreign company is involved in criminality can disqualify it from Committee on Foreign Investment in the United States (CFIUS) approval to buy a sensitive U.S. asset. And Campbell helped the FBI recorded the first criminal activity by Rosatom officials inside its Tenex arm in November 2009, nearly an entire year before CFIUS approved Rosatom’s purchase of Uranium One.
Justice officials trusted the informant Campbell enough to keep him working undercover for six years and to pay him more than $51,000 once the convictions were secured.
A check obtained by The Hill shows the FBI paid Campbell an informant fee of more than $51,000 in January 2016, shortly after the last convictions in the Russian nuclear bribery case were made.