“By any standard, the horrific crime uncovered last night ranks as a stark reminder of why human smuggling networks must be pursued, caught and punished. U.S. Immigration and Customs Enforcement’s Homeland Security Investigations works year-round to identify, dismantle, and disrupt the transnational criminal networks that smuggle people into and throughout the United States. These networks have repeatedly shown a reckless disregard for those they smuggle, as today’s case demonstrates. I personally worked on a tragic tractor trailer case in Victoria, Texas in 2003 in which 19 people were killed as a result of the smugglers’ total indifference to the safety of those smuggled and to the law.
“The men and women of ICE are proud to stand alongside our law enforcement partners, including locally and at the U.S. Department of Justice, to combat these smuggling networks and protect the public and those who would fall victim to their dangerous practices that focus solely on their illicit profits. So long as I lead ICE, there will be an unwavering commitment to use law enforcement assets to put an end to these practices.”
***
Texas Public Radio
FNC: A suspect arrested in connection with the deaths of at least 10 people packed into a sweltering tractor-trailer is due in court Monday over his alleged role in the immigrant-smuggling attempt gone wrong.
Federal prosecutors said they planned to bring charges against James Mathew Bradley Jr., 60, of Clearwater, Florida, who is due to appear in federal court at 11 a.m. local time.
U.S. Attorney Richard Durbin Jr. did not say whether Bradley was the driver of the truck, although investigators said earlier that the driver was in custody.
Authorities initially discovered eight bodies Sunday inside the crowded 18-wheeler parked outside a Walmart in the summer heat. Two additional victims later died at the hospital.
Officials feared the death toll could still rise, because nearly 20 others rescued from the truck were in dire condition, many suffering from extreme dehydration and heatstroke, officials told the Associated Press.
Based on initial interviews with survivors of the San Antonio tragedy, more than 100 people may have been packed into the back of the 18-wheeler at one point in its journey, ICE acting Director Thomas Homan said. Officials said 39 people were inside when rescuers arrived, and the rest were believed to have escaped or hitched rides to their next destination.
Four of the survivors appeared to be between 10 and 17 years old, Homan said. Investigators gave no details on where the rig began its journey or where it was headed.
Mexican nationals were among both the survivors and the dead, Mexican Consul General in San Antonio Reyna Torres said, without giving a specific number. Torres said the consulate has been in contact with relatives both in Mexico and in the U.S.
Guatemala’s foreign ministry, meanwhile, said at least two Guatemalans were on the abandoned rig. The two male survivors told Guatemalan consulate officials that they crossed the border by foot at Laredo and boarded the tractor-trailer, according to Tekandi Paniagua, communications director for the foreign ministry. The pair told officials their final destination was Houston, Paniagua added. More here.
Category Archives: Department of Homeland Security
Kushner Overlooked 77 Assets, But it Gets Worse
In part from Examiner: White House senior adviser Jared Kushner on Friday released a revised version of his personal financial disclosure that reveals his initial filing did not include 77 assets, according to a report Friday.
The Wall Street Journal reports that the new disclosure says 77 assets were “inadvertently omitted” from Kushner’s original form, released in March, and were added during the “ordinary review” process with the government ethics office.
In addition to information on Kushner, President Trump’s son-in-law, the new disclosure includes details of Ivanka Trump’s finances.
Ivanka Trump is the president’s daughter, a senior White House aide and Kushner’s wife.
The new financial forms show Kushner and Ivanka Trump collectively have between $206 million and $760 million in assets, the Journal said. Kushner’s initial disclosure valued their assets at between $240 million and $740 million. More here.
***
IN 2014, Prevezon Holdings Limited, was controlled by the son of a Russian political figure. The company had many interests in real estate, including an investment in a venture with a Soviet-born diamond and property magnate named Lev Leviev—who also happened to be one of the developers of 20 Pine.
Starting in late 2009, Prevezon began purchasing units in 20 Pine, acquiring five in total. The company later added three Manhattan commercial spaces to create a $24 million portfolio, which prosecutors sued to seize last year. “While New York is a world financial capital,” U.S. Attorney Preet Bharara said in a press release announcing the action, “it is not a safe haven for criminals seeking to hide their loot.” The lawsuit is here.
Jared Kushner sealed Manhattan real estate deal with oligarch’s firm cited in money-laundering case
Guardian: Donald Trump’s son-in-law bought part of old New York Times building from Soviet-born tycoon, Guardian investigation into Russian money in NYC property market finds
Jared Kushner, the son-in-law of Donald Trump, who acts as his senior White House adviser, secured a multimillion-dollar Manhattan real estate deal with a Soviet-born oligarch whose company was cited in a major New York money laundering case now being probed by members of Congress.
A Guardian investigation has established a series of overlapping ties and relationships involving alleged Russian money laundering, New York real estate deals and members of Trump’s inner circle. They include a 2015 sale of part of the old New York Times building in Manhattan involving Kushner and a billionaire real estate tycoon and diamond mogul, Lev Leviev.
The ties between Trump family real estate deals and Russian money interests are attracting growing interest from the justice department’s special counsel, Robert Mueller, as he seeks to determine whether the Trump campaign collaborated with Russia to distort the outcome of the 2016 race. Mueller has reportedly expanded his inquiry to look at real estate deals involving the Trump Organization, as well as Kushner’s financing.
Kushner will go before the US Senate intelligence committee on Monday in a closed session of the panel’s inquiry into Russian interference in the election in what could be a pivotal hearing into the affair.
Leviev, a global tycoon known as the “king of diamonds”, was a business partner of the Russian-owned company Prevezon Holdings that was at the center of a multimillion-dollar lawsuit launched in New York. Under the leadership of US attorney Preet Bharara, who was fired by Trump in March, prosecutors pursued Prevezon for allegedly attempting to use Manhattan real estate deals to launder money stolen from the Russian treasury.
The scam had been uncovered by Sergei Magnitsky, an accountant who died in 2009 in a Moscow jail in suspicious circumstances. US sanctions against Russia imposed after Magnitsky’s death were a central topic of conversation at the notorious Trump Tower meeting last June between Kushner, Donald Trump Jr, Trump campaign manager Paul Manafort and a Russian lawyer with ties to the Kremlin.
Don Jr and Manafort have been called to testify before the Senate judiciary committee on Wednesday, at which they are certain to face questions about the Trump Tower encounter.
Two days before it was due to open in court in May, the Prevezon case was settled for $6m with no admission of guilt on the part of the defendants. But since details of the Trump Tower meeting emerged, the abrupt settlement of the Prevezon case has come under renewed scrutiny from congressional investigators.
Four Russians attended the meeting, led by Natalia Veselnitskaya, a lawyer with known Kremlin connections who acted as legal counsel for Prevezon in the money laundering case and who called the $6m settlement so slight that “it seemed almost an apology from the government”. Sixteen Democratic members of the House judiciary committee have now written to the justice department in light of the Trump Tower meeting demanding to know whether there was any interference behind the decision to avoid trial.
Constitutional experts are also demanding an official inquiry. “We need a full accounting by Trump’s justice department of the unexplained and frankly outrageous settlement that is likely to be just the tip of a vast financial iceberg,” said Laurence Tribe, Harvard University professor of constitutional law.
Separately, the focus of investigators on Trump family finances stem from the vast flow of Russian wealth that has been poured into New York real estate in recent years. As Donald Trump Jr put it in 2008, referring to the Trump Organization: “We see a lot of money pouring in from Russia.”
Among the overlapping connections is the 2015 deal in which Kushner paid $295m to acquire several floors of the old New York Times building at 43rd street in Manhattan from the US branch of Leviev’s company, Africa Israel Investments (AFI), and its partner Five Mile Capital. The sale has been identified as of possible interest to the Mueller investigation as Kushner later went on to borrow $285m in refinancing from Deutsche Bank, the German financial house that itself has been embroiled in Russian money laundering scandals and whose loans to Trump are coming under intensifying scrutiny.
Court documents and company records show that AFI was cited in the Prevezon case as a business partner of the defendants. In 2008, Prevezon entered a partnership with AFI in which Prevezon bought for €3m, a 30% stake in four AFI subsidiaries in the Netherlands. Five years later, AFI tried to return the money to the Russian-owned company, but it was intercepted and frozen by Dutch authorities at the request of the US government as part of the Prevezon money-laundering probe.
In Manhattan, Leviev’s firm also sold condominiums to Prevezon Holdings from one of its landmark developments at 20 Pine Street, just a few blocks from Wall Street.
Real estate brochures describe the lavish interior decor of the condominiums, replete with bathrooms bedecked in stone and exotic woods, and boasting “the ultimate in pampering; a sybaritic recessed rain shower”. The 20 Pine Street apartments that Leviev sold to Prevezon were later frozen by US prosecutors seeking to block the flow of what they alleged to be money stolen from the Russian treasury and laundered through New York real estate.
Prevezon’s 20 Pine Street apartments and €3m in assets were all released as part of the settlement in May.
The Guardian contacted both Kushner and Leviev for comment, but they did not immediately respond.
The pursuit of Prevezon Holdings for alleged money laundering took on enormous political significance as it unfolded. For the prosecutors, it was a test case over suspicious Russian money flows designed to show the US was serious about going after money launderers. For the Russians, it was an opportunity to push back against stringent US sanctions that had long infuriated the Kremlin.
In court documents, US prosecutors accused Prevezon and its sole shareholder, Denis Katsyv, of participating in the laundering of proceeds of the vast tax fraud that stole $230m from the Russian treasury and moved it out of the country in chunks. Prevezon was alleged to have received some of the fraudulent spoils through a network of shell companies, hiding the money by investing in Manhattan real estate including the Leviev condominiums in 20 Pine Street.
Prevezon and Katsyv have consistently denied any involvement in money laundering and have dismissed the lawsuit as “ill-conceived”. In a statement released at the time of the settlement, they said they had “no involvement in or knowledge of any fraudulent activities”.
Magnitsky discovered the massive tax fraud, said to be one of the largest in Vladimir Putin’s Russia, in 2007. After he blew the whistle on the scam, he was arrested by the same officials whom he had accused of covering up the racket and imprisoned, dying in jail having been denied medical treatment.
Magnitsky’s death led to a political backlash in the US that in turn spawned tough sanctions on Russia, known as the Magnitsky Act. Russian individuals associated with the lawyer’s demise and other human rights abuses were banned entry to the US.
Veselnitskaya not only acted as Prevezon’s Russian counsel in the money-laundering case, she also was a leading lobbyist against the Magnitsky sanctions. She raised the subject prominently at the meeting in Trump Tower with Don Jr and Kushner, though according to Veselnitskaya the president’s son-in-law left after 10 minutes.
By the time of the Trump Tower meeting, Veselnitskaya was already personally acquainted with Russia’s powerful prosecutor general, Yuri Chaika, and her lobbying against the Magnitsky sanctions had drawn significant attention in government circles.
“Natalia’s main role was coordinating, including regular coordination with Chaika, whom she knew personally,” said a source acquainted with the Prevezon case.
Veselnitskaya told the Guardian: “My meeting with Trump’s son was a private meeting; nobody in the government had anything to do with it.” She declined to answer a follow-up question about whether and how she knew Chaika.
Jamison Firestone, the founder of the Russian law firm that employed Magnitsky at the time that he exposed the fraud, said that Veselnitskaya clearly intended to use the Trump Tower meeting to lobby against the Magnitsky sanctions. “They really made it a state priority to get rid of these sanctions,” he said.
Hezbollah Terror Cells in Lebanon and Latin America
Kuwait expels Iranian diplomats over ‘terror’ cell: United Nations (United States) (AFP) – US Ambassador Nikki Haley on Wednesday accused Lebanon’s Hezbollah of amassing weapons and said the world must turn its attention to the actions of the powerful paramilitary organization.
Anyone ever ask or investigate the Hezbollah weapons inventory in Latin America?
No Latin American Country Has Branded Hezbollah a Terror Group Despite Ties to Major Attacks
WASHINGTON, D.C.—Latin American countries have failed to register Iranian proxy Hezbollah as a terrorist organization despite the threat it poses to the region, a Peruvian official revealed during a discussion on Capitol Hill.
The Shiite group is involved in various illicit activities in Latin America to generate money that some experts believe is used to fund terrorist activities in the Middle East.
During a discussion Wednesday on Capitol Hill hosted by the Center for a Secure Free Society (SFS), Moises Vega de la Cruz, a public prosecutor for the Peruvian government specializing in terrorism cases, revealed that “in Latin America, Hezbollah is not recognized as a terrorist organization.”
“I think Hezbollah is a threat to Latin America. Hezbollah is a terrorist organization that is advancing not only in Peru but in other Latin American countries as well,” he told Breitbart News.
Joseph Humire, an expert on Iranian activity in the Western Hemisphere and executive director of SFS, noted that no Latin American country has registered Hezbollah as a terrorist organization.
The United States and the European Union have deemed Lebanon’s Shiite group Hezbollah as a terrorist organization.
In the United States, Hezbollah’s main supporter Iran has been officially labeled a state sponsor of terror.
Peru recently adjudicated a case involving an alleged Hezbollah operative accused of explosives-related crimes in 2014. The individual avoided prosecution, but De La Cruz has appealed the decision.
“Most Latin Americans don’t view Islamist terrorism as a significant threat in their region and little public pressure has been placed on the establishment, reform, or improvement of weak or non-existent anti-terrorism laws across the region,” SFS pointed out in a statement. “Consequently, the Islamic State [ISIS/ISIL], Hezbollah, and other Jihadist networks and sympathizers are spreading throughout South America with impunity.”
The U.S. government has acknowledged the presence of both Shiite Hezbollah and Sunni ISIS in Latin America.
De la Cruz noted that Hezbollah maintains a presence in Peru, where it is reportedly converting people and trying to get involved politically.
The Peruvian Latina news agency reported last year that the Shiite group has registered as an official political party in Peru’s Abancay province, home to the largest concentration the country’s small Muslim community.
Hezbollah has established itself as an official political party in its main base of Lebanon.
Argentinian authorities have linked Hezbollah to fatal attacks against the South American country’s Jewish community, including the 1994 bombing of the Argentine-Israeli Mutual Association (AMIA)—the deadliest terrorist attack in the Western Hemisphere before September 11, 2001.
The U.S. military and the Department of State have expressed concern about the group’s presence in Latin America.
According to the U.S. State Department, Venezuela has provided a “permissive environment” that has allowed Hezbollah to thrive in the region.
Last year Michael Braun, a former DEA operations chief, told American lawmakers that Hezbollah is generating hundreds of millions from a “cocaine money laundering scheme” in Latin America that “provides a never-ending source of funding” for its terrorist operations in Syria and elsewhere.
Hezbollah is fighting on behalf of Iran on the side of the Russian-backed Syrian dictator Bashar al-Assad.
In an annual report to Congress issued earlier this year, U.S. Southern Command (SOUTHCOM) noted that “Hezbollah members, facilitators, and supporters engage in licit and illicit activities in support of the organization, moving weapons, cash, and other contraband to raise funds and build Hezbollah’s infrastructure in the region.”
SOUTHCOM is charged with overseeing American military activity in most of Latin America.
The group is believed to be operating throughout the Western Hemisphere.
Iran ‘foremost state sponsor of terrorism in 2016’: US state department
The department’s annual report on global terrorism accused the Iranian Revolutionary Guard’s Quds Force — which is responsible for operations outside the country — along with Iranian partners, allies, and proxies, of ‘playing a destabilising role in military conflicts in Iraq, Syria, and Yemen’
Iran was the “foremost state sponsor of terrorism in 2016”, the US state department said on Wednesday in its annual report on terrorism worldwide.
The 2016 Country Reports on Terrorism — the first released by the state department since US president Donald Trump assumed office — also highlighted Hizbollah’s increasing reach in Syria, Iraq and Yemen and an increase in “its long-term attack capabilities”.
Although the report said there had been a 9 per cent drop in global terror attacks last year from 2015, as well as a 13 per cent drop in terror-related fatalities, it stressed that “the Islamic State of Iraq and Syria (ISIS) remained the most potent terrorist threat to global security” in 2016.
Al Qaeda and its regional affiliates also “remained a threat to the US homeland and our interests abroad despite counter-terrorism pressure by US partners”, the report said.
On Iranian sponsorship of terrorism, the report accused the Revolutionary Guard’s Quds Force — which is responsible for operations outside the country — along with Iranian partners, allies, and proxies, of “playing a destabilising role in military conflicts in Iraq, Syria, and Yemen”. It also said “Iran continued to recruit fighters from across the region to join Iranian-affiliated Shia militia forces engaged in conflicts in Syria and Iraq, and has even offered a path to citizenship for those who heed this call”.
The 2016 report put more emphasis on the threat from Hizbollah than in previous years. It described the Lebanese political party and militia as “playing a major role in supporting the Syria government’s efforts to maintain control and territory, and providing training and a range of other support for Iranian-aligned fighters” in these conflict zones.
The state department said “there are reportedly about 7,000 Hizbollah fighters in Syria”, though it also highlighted that the group had lost “several senior military commanders and hundreds of fighters” in fighting there last year.
The report also highlighted Hizbollah’s continued efforts to “develop its long-term attack capabilities and infrastructure around the world”.
Justin Siberell, the state department’s acting coordinator for counter-terrorism, told The National on Wednesday that “Hizbollah maintains a sophisticated operation with [a] broad network group around the world”.
Mr Siberllel said it was unclear, however, if the Syrian conflict had boosted Hizbollah’s standing. On the one hand, the group had gained military expertise in Syria, he said, while on the other, it had suffered large number of casualties.
“It’s a mixed picture,” he said.
On Bahrain, the report said that “during 2016 the Bahraini government continued to make gains in detecting, neutralising, and containing terrorist threats from violent Shia militants and ISIS sympathisers”. It also referenced improved counter-terror co-operation with the UAE, Egypt, Saudi Arabia and other Arab countries.
The report voiced concerns over Al Qaeda exploiting the ongoing war in Yemen to make gains. It said that “despite leadership losses, Al Qaeda in the Arabian Peninsula (AQAP) remained a significant threat to Yemen, the region, and the United States, as ongoing conflict in Yemen hindered US efforts to counter the group”. It was a similar situation with Al Qaeda’s former affiliate in Syria, the report said.
“Al Nusra Front continued to exploit ongoing armed conflict to maintain a territorial safe haven in select parts of northwestern Syria,” the report said, referring to the group that now calls itself Jabhat Fatah Al Sham.
When it came to the Emirates, the report said that in 2016 “the UAE government maintained a robust counter-terrorism and countering violent extremism (CVE) partnership with the United States through its collaboration with US law enforcement; support of the Global Coalition to Defeat ISIS; and counter‑messaging initiatives, such as the Sawab and Hedayah Centers.”
The report made reference to the UAE’s deployment of forces to Yemen “to counter the spread of AQAP and ISIS” there, highlighting that, “along with its Yemeni partners, the UAE military successfully ejected AQAP from the port city of Mukalla in April — depriving AQAP from millions [of dollars] in monthly income — and from the coastal towns of Balhaf and Bir Ali in December”.
The report also highlighted wins for UAE border security.
“UAE government security apparatus continued monitoring suspected terrorists in the UAE, and successfully foiled terrorist attacks within its borders,” it said, adding: “UAE customs, police, and other security agencies improved border security and worked together with financial authorities to counter terrorist finance.”
Opioid Crisis Then and Now
The Opioid Crisis Is Dire. Why We Need a National Conversation About It Separate From Obamacare.
Let’s be honest—the opioid crisis in America is huge, it is severe, and it is devastating. But this partisan-fought legislation just isn’t the place to put that funding. And it would likely do little to help stem and reverse the opioid crisis.
First, it’s not as though funding for opioid treatment and recovery has been absent from the federal budget. As recently as last month, Sen. Susan Collins, R-Maine, was touting signed legislation that spent more than $1 billion to fund recovery programs.
This money was authorized separately from the debate over Obamacare in two pieces of legislation known as the Comprehensive Addiction and Recovery Act and the 21st Century Cures Act.
We know that prevention programs have worked in the past, whether they pertain to forest fires or drunk driving or, for that matter, the massive reduction in drug use we witnessed in the late 1980s and early 1990s.
Such a prevention program for the opioid crisis must start with leadership from the White House in leading these conversations and highlighting the devastation of substance abuse initiation.
It requires detailing what is driving the opioid epidemic—namely, illegal fentanyl, heroin, and other illegal drug use and diversion. It requires more law enforcement—from border and customs policies and cracking down on cartels to international initiatives. And it requires messaging to our youth. More here.
This Isn’t the First U.S. Opiate-Addiction Crisis
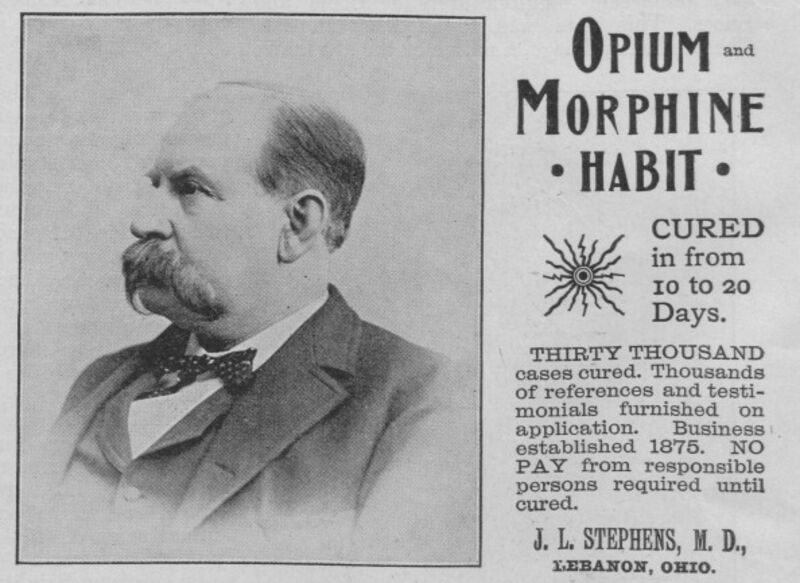
Problem and solution. Source: Museum of Science and Industry, Chicago/Getty Images
Bloomberg: The U.S. is in the throes of an “unprecedented opioid epidemic,” reports the Centers for Disease Control. The crisis has spurred calls for action to halt the rising death toll, which has devastated many rural communities.
It’s true that there’s an opioid epidemic, a public health disaster. It’s not true that it’s unprecedented. A remarkably similar epidemic beset the U.S. some 150 years ago. The story of that earlier catastrophe offers some sobering lessons as to how to address the problem.
Opioids are a broad class of drugs that relieve pain by acting directly on the central nervous system. They include substances such as morphine and its close cousin, heroin, both derived from the opium poppy. There are also synthetic versions, such as fentanyl, and medications that are derived from a mix of natural and synthetic sources, such as oxycodone.
Opioid addiction can take many forms, but the current crisis began with the use and abuse of legal painkillers in the 1990s, and has since metastasized into a larger epidemic, with heroin playing an especially outsized role.
All of this is depressingly familiar. The first great U.S. opiate-addiction epidemic began much the same way, with medications handed out by well-meaning doctors who embraced a wondrous new class of drugs as the answer to a wide range of aches and pains.
The pharmacologist Nathaniel Chapman, writing in 1817, held up opium as the most useful drug in the physician’s arsenal, arguing that there was “scarcely one morbid affection or disordered condition” that would fail to respond to its wonder-working powers. That same year, chemists devised a process for isolating a key alkaloid compound from raw opium: morphine.
Though there’s some evidence that opiate dependency had become a problem as early as the 1840s, it wasn’t until the 1860s and 1870s that addiction became a widespread phenomenon. The key, according to historian David Courtwright, was the widespread adoption of the hypodermic needle in the 1870s.
Prior to this innovation, physicians administered opiates orally. During the Civil War, for example, doctors on the Union side administered 10 million opium pills and nearly three million ounces of opium powders and tinctures. Though some soldiers undoubtedly became junkies in the process, oral administration had all manner of unpleasant gastric side effects, limiting the appeal to potential addicts.
Hypodermic needles by contrast, delivered morphine directly into a patient’s veins with no side effects, yielding immediate results. As Courtwright notes: “For the first time in the entire history of medicine near-instantaneous, symptomatic relief for a wide range of diseases was possible. A syringe of morphine was, in a very real sense, a magic wand.”
An enthusiastic medical profession began injecting morphine on a vast scale for all manner of aches and pains, much the way that a more recent generation of doctors began prescribing Oxycontin and other legal drugs in a reaction against widespread undertreatment of pain. Wounded veterans became addicts, but so, too, did people suffering from arthritis. Women also became addicts en masse, thanks to the practice of treating menstrual cramps – or for that matter, any female complaint of pain – with injections of morphine.
Skeptics in the medical profession warned about the dangers of administering too much morphine. Yet these warnings generally fell on deaf ears. Some of the problem lay with the doctors themselves. One well-regarded doctor put it this way: “Opium is often the lazy physician’s remedy.”
But distance played a role, too. Doctors traveling dirt roads on horseback couldn’t always follow up with patients in pain, and so they left their charges with vials of morphine. Well-meaning doctors who might otherwise resist administering morphine also faced pressure from patients and families to do so. If they refused, it was easy to find a doctor who would comply.
In the end, though, the medical profession largely solved the problem on its own. As awareness of physicians’ role in fostering addiction spread, medical schools taught aspiring doctors to avoid prescribing morphine except under carefully controlled circumstances. The growing availability of milder analgesics – salicylates like aspirin – made the job easier, offering a less powerful, but far safer, alternative to morphine.
While the younger generation of doctors stigmatized morphine, the problem was increasingly linked to older, poorly trained doctors who had come of age in an era when the hypodermic needle was touted as a cure-all. A study in 1919, for example, found that 90 percent of opiate prescriptions in Pennsylvania came from only a third of the state’s doctors, most of whom were over 50 years old.
As the medical profession started to police its ranks, shaming those who enabled addiction, the epidemic began to burn itself out. “Old addicts died off faster than new ones were created,” writes Courtwright. The smaller group of addicts who became the face of opiate addition tended to be poorer “pleasure users” who picked up the habit in the criminal underworld.
Today’s opioid epidemic is similar to the one that came and went over a century ago. While there is plenty of room for government assistance in funding treatment for addicts, never mind regulation of drugs, history suggests that the medical profession will ultimately play the most important role.
There are some promising signs. The number of opioid prescriptions written by doctors has dropped by small amounts over the past few years, though some of the evidence suggests that the decline has more to do with patients anxious about the potential for addiction.
Still, it took decades during the 19th century for doctors to shy away from injecting patients with morphine for the slightest complaint. It may take just as long before doctors kick the habit of prescribing powerful pain pills.
Bill Clinton, Trumps’ and Renaissance Capital
Primer: The 8th person at the Trump Jr. meeting was Ike Kaveladze. He currently serves as Vice President of the Crocus Group in Moscow. Mr Balber, the lawyer for Kaveladze, said he revealed the identity of the eighth participant after receiving a call from a representative of special counsel Robert Mueller – the first indication that the Justice Department investigator is looking into the meeting. Previously, Federal investigators say Kaveladze immediately began laundering money for Russians.
Kaveladze was the president of International Business Creations, a Delaware corporation. Between 1991 and 2000, IBC and sister corporation Euro-American moved $1.4 billion from Eastern Europe through U.S. banks and back to Europe, the Government Accountability Office found in 2000.
But let’s go back to Bill and Hillary shall we? We may determine just why President Trump backed off his campaign pledge and decided not to prosecute Hillary…
THE CLINTON FAMILY BUSINESS There may be no Clinton Foundation office in Moscow or St. Petersburg, but it is not for lack of trying. Bill Clinton received half a million dollars in 2010 for a speech he gave in Moscow, paid by a Russian firm, Renaissance Capital, that has ties to Russian intelligence. The Clinton Foundation took money from Russian officials and oligarchs, including Victor Kekselberg, a Putin confidant. The Foundation also received millions of dollars from Uranium One, which was sold to the Russian government in 2010, giving Russia control of 20% of the uranium deposits in the U.S. — the sale required approval from Hillary Clinton’s State Department. What’s more, at least some of these donations weren’t disclosed. “Ian Telfer, the head of the Russian government’s uranium company, Uranium One, made four foreign donations totaling $2.35 million to the Clinton Foundation. Those contributions were not publicly disclosed by the Clintons, despite an agreement Mrs. Clinton had struck with the Obama White House to publicly identify all such donors,” the Times has reported.
Stephen Jennings is the co-founder and CEO of Renaissance Capital and in 2010 he resided over the launch of Tatu City, a planned community for 60,000 northeast of Nairobi.
Before that Vladimir Dzhabarov was a member of the FSB’s Department “K,” or its financial counter-intelligence division . From 2006-09, he was also the First Vice President at Renaissance Capital, a Moscow-based investment firm, which the 36 year-old Magnitsky claimed was involved in a six-long-year long conspiracy by an organized crime syndicate and Russian government officials to defraud the nation’s taxpayers. Renaissance Capital denies it had any part in any tax frauds; in 2009, the bank’s deputy chief executive Hans Jochum Horn told the New York Times that any illegal transactions involving Renaissance subsidiary companies took place after those companies had been sold off to new owners.
Magnitsky claimed in 2008 that criminals tied to Renaissance Capital, who were allegedly working in lockstep with tax and law enforcement agents, stole some $470 million by orchestrating illegal and complex tax refund schemes. As part of his sweeping investigation, Magnitsky claimed that in 2001-2002, Igor Sagiryan, the former president of Renaissance Capital, had supposedly commissioned named a fellow named Dmitry Klyuev to arrange a series of tax refunds through the corrupt Russian court system. This seconding of a known mobster to a seemingly legitimate financial institution was confirmed by Yuri Sagaidak, a former KGB general who was at the time the vice president of Renaissance Capital, in Russian court testimony.
The Klyuev Group, which U.S. Senator John McCain in 2012 urged President Obama to use an executive order to sanction wholesale as a “dangerous transnational criminal organization,”concocted its first nine-figure refund scheme in 2006, according to Magnitsky and others. The conspirators allegedly included the heads of Moscow Tax Offices 28 and 25, Olga Stepanova and Elena Khimina, respectively; Klyuev’s own attorney, Andrey Pavlov; and an Interior Ministry official, Major Pavel Karpov, who had previously investigated Klyuev for attempting to steal $1.6 billion worth of shares of a profitable Russian iron ore company. (Klyuev received a two-year suspended sentence in that case.)Read more here.
It has now emerged that the US Department of Justice has traced proceeds of the fraud to a bank account in Bournemouth held by Renaissance Capital Investment Management Ltd.
A chart produced by the US Department of Justice shows funds flowing through a series of foreign companies before being channelled into three main firms, including Prevezon, against which the DoJ is taking legal action to seize assets allegedly linked to the money, and the Bournemouth Renaissance account.
Renaissance Capital is a Moscow-based investment bank now controlled by billionaire oligarch Mikhail Prokhorov. Igor Sushchin, until recently the organisation’s head of IT security, was one of two FSB operatives accused by the FBI last month of hacking 500 million Yahoo email accounts. An indictment said it was “unknown” whether the firm “knew of his FSB affiliation”. Read more here for details and to help with the confusion.
*** In case you are wondering what Robert Mueller, the special investigator is looking at with this team, hold on this is going to get worse.
Magnitsky tracked money and found it all over the globe before he was murdered in a Russian prison, where the FSB arrested him for whistle-blowing.
According to records obtained by OCCRP, between Moscow and Geneva the money traveled all over the world in a veritable chain of shell companies set up by GT Group — a company that was connected to the sale of arms from N. Korea to Iran as well as laundering money for the Mexican Sinaloa Cartel.
The couple used the same Credit Suisse accounts to purchase two apartments valued at US$2 million each at Dubai’s Kempinksi resort for tax office deputies Elena Anisimova and Olga Tsareva. According to bank records, the apartments were purchased using the same bank account Stepanova used.
US$3 million arrived in the accounts on January 3, 2008 via Bristoll Export, a company which had been registered by GT Group in New Zealand. In February, companies incorporated in Cyprus, Moldova, and the United Kingdom sent US$9 million to the Credit Suisse accounts. See detailed information on one of the companies, NOMIREX, which processed US$8 million in its accounts while filing as “inactive” in a separate story.
In May and June 2008, the accounts held by Stepanov and Stepanova sent US$10 million to a shell company called Arivust holding. Records obtained by OCCRP show that through a series of agreements, Stepanov is named as the beneficial owner of the company.
The records also show that Stepanov is the beneficial owner of another company, Aikate Properties, which sent US$2 million to his Swiss account.
Hermitage acquired copies of the Credit Suisse transactions and used them to file a complaint with the bank and the Swiss federal attorney general this spring.
Stepanova remains employed by the Russian government. She resigned from the tax ministry but now works for a new defense agency established by Medvedev that oversees procurement and allocation of police and military equipment to the country’s law enforcement and military agencies.
So do Lieutenant Colonel Artyom Kuznetsov, whose assets were estimated at US$3 million although his official annual salary is about US$10,000; and Russian Interior Ministry Pavel Karpov, whose assets were estimated at US$1.5 million while his yearly pay was only US$10,000. Transparency International ranks Russia as the most corrupt large nation on earth, and the large country most likely to bribe abroad. They also estimate that bribery alone costs Russia US$300 billion annually, the total GDP of Denmark. Bribery “is not even half of the problem,” according to a US House of Representatives Staffer who did not want to be identified because of his frequent work with Russian officials on policy issues including the Magnitsky case. Yep…more here.
Donald Trump Jr. had a meeting with 8 people in the room at Trump Tower in June of 2016. The meeting included Natalia Vesealnitskaya who was hired by and worked closely with Petr Katsyv who is/was the legal owner of Prevezon Holdings. The U.S. Justice Department for the Southern District of New York was prosecuting a money laundering case against Prevezon Holdings and it was settled too quickly directly after Jeff Sessions fired Phreet Bharara. Katsyv is also the vice president of Russian Railways, a state run rail operation run by Vladimir Yakunin and a close confidant of Vladimir Putin. Still confused and overwhelmed? Well there is more here.
Sorry there is yet another name, Sergei Roldugin. This particular Sergei is hardly a money launderer of the garden variety, in fact he is a cellist. But..he is at the center of a global scheme that moved $2.0 billion through Russian state banks, Swiss and Panamanian law firms all tied to Vladimir Putin via the investigation and release of the Panama Papers. Kinda wonder how a cellist is worth $100 million, right? Good question but money mess began at the Bank Rossiya, a top go-to bank for Putin and his inner circle. Oh yeah, Sergei Roldugin the the godfather to Putin’s oldest daughter, Maria.
In September of 2016, Roldugin announced before reporters at the Kremlin that Donadl Trump will be the next U.S. president.





