The Iranian people have been protesting against the regime for quite some time and in some cases it has turned deadly, where military forces are firing on the protestors. What are the protests about? Their economy. Remember when the Obama White House gave Iran billions that apparently we owed from back debts and the regime was to use the money to infuse growth in the economy? Yeah, not so much. In fact the starving and unemployed citizens of Iran are demanding the regime get out of Syria and pay attention at home.
Related reading: Iran Calls for Calm After Water Protests, Clashes
Yet, water availability in Iran has been at a crisis point for a few years and getting worse.
Dozens of riot police on motorcycles faced off against farmers in the same town, Varzaneh, another video showed. Smoke swirled around the protesters and the person filming said tear gas was being fired. A second person reported clashes. Police in the city of Isfahan were not immediately available to comment.
“What’s called drought is more often the mismanagement of water,” said a journalist in Varzaneh, who asked not to be identified because of the sensitivity of the subject.
“And this lack of water has disrupted people’s income.”
Farmers accuse local politicians of allowing water to be diverted from their areas in return for bribes.
While the nationwide protests in December and January stemmed from anger over high prices and alleged corruption, in rural areas, lack of access to water was also a major cause, analysts say.
At least 25 people were killed and, according to one parliamentarian, up to 3,700 people were arrested, the biggest challenge yet for the government of president Hassan Rouhani, who was reelected last year. More here from Reuters.
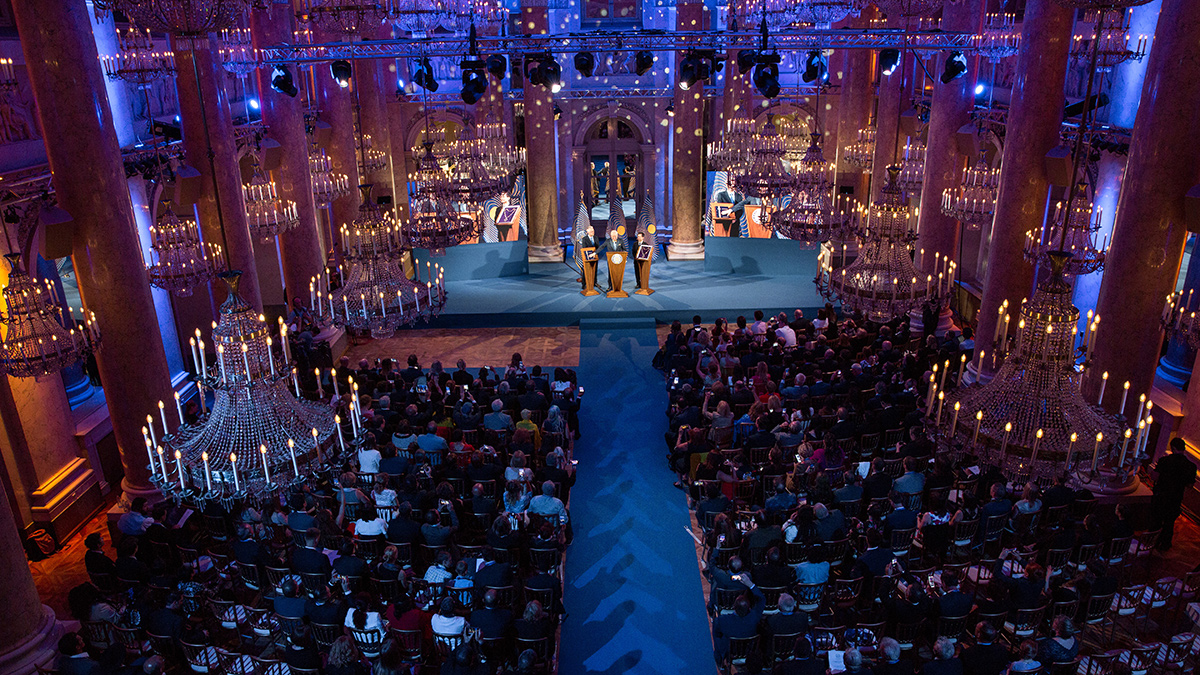
Meanwhile, in Paris there are several Americans attending the annual National Council of Resistance of Iran (NCRI) – an umbrella bloc of opposition groups in exile that seek an end to Shi’ite Muslim clerical rule in Iran. There apparently was a bomb plot on Monday that was foiled, where an Iranian diplomat was arrested along with several others.
Since President Trump formally exited the JCPOA, the nuclear deal, Iran has some nefarious activities again in play and that includes hacking beyond punishing the Iranian citizens and bomb plots.
Since the 2009 Green Revolution in Iran, the Iranian Revolutionary Guard Corps has taken to hacking including by proxy.
The emergence of the Iranian Cyber Army (ICA) as an extension of the IRGC was an initial attempt by the Islamic Republic at conducting internationally focused operations. These operations were a departure from Gerdab’s focus on maintaining domestic moral values and defending government rhetoric. In 2011, the IRGC’s ICA formed the foundation of the Khaybar Center for Information Technology. According to a former IRGC cyber commander, the Khaybar Center was established in 2011 and has been linked to a number of attacks against the United States, Saudi Arabia, and Turkey.
Even today, the balance between ideology and cyber skills remains problematic. One example of the conflict between ideology and skill was Mohammad Hussein Tajik, a former cyber commander within the IRGC. According to Insikt Group’s source, Tajik’s father maintained a strong religious background and was a veteran of Iran’s ministry of intelligence. Yet Tajik was arrested and killed because the Iranian government feared that Tajik was not ideologically aligned and posed a betrayal and flight risk.
Today, based on ongoing contact between Insikt Group’s source and Iranian hackers, it is estimated that there are over 50 organizations vying for government-sponsored offensive cyber projects. Only the best teams succeed, are paid, and remain in business. The government does its best to compartmentalize — one job might be creating a remote code exploit (RCE) for a popular software application, while another job might be using the RCE and establishing persistent unauthorized access. Two different contractors (or more) are typically required to complete the government-defined objective.
Public knowledge has also established that Iranian academic institutions play a contractor-like role. Specific examples include Shahid Beheshti University (SBU) and the Imam Hossein University (IHU), which have comprehensive science and technology departments attracting some of the best academic talent in Iran. In fact, the SBU has a specific cyberspace research institute dedicated to such matters, and the IHU was founded by the IRGC.
For a full read on the report due to an interview with a previous Iranian hacker and significant research on state sponsored campaigns, go here.
Cyber security professionals in the United States have detected Iranian hackers breaking into defense contractors, aviation systems, energy companies, telecom operations and other tech companies in the United States. Iran is listed at APT 33, Advanced Persistent Threat and Saudi Arabia is just as vulnerable as the United States. In 2016, the Department of Justice indicted 7 Iranians on cyber attacks on dozens of U.S. banks, attempting to shut down the Bowman Avenue dam operation in New York and to disrupt other critical U.S. infrastructure sites. 45 major financial institutions were targeted including JP Morgan, Well Fargo and American Express. Read more detail here.






 Connect with Forward – Thinking People
Connect with Forward – Thinking People Protect Our Planet and Future Generations
Protect Our Planet and Future Generations
