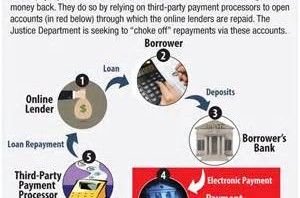
Announced and launched in 2014, the White House in collusion with the Department of Justice created an edict in the national banking system that is allegedly to protect consumers, from what exactly is still to be determined, but Operation Choke Point leads to the assassination of private business and then it is an attack on customers. There are some bankers that are happy to comply, yet others not so much.
In a recent weekly address in Spanish, White House Director of the Domestic Policy Council Cecilia Muñoz weaved the President’s budget proposal into a fictitious narrative aimed to assure the Hispanic community that the administration’s policies will contribute to provide opportunity, economic growth, and prosperity, promising “it will grow the middle class.”
But as has all-too-often been the case during the last few years, the administration’s rhetoric concerning economic opportunity flies in the face of heavy-handed political maneuvers that destroy chances for upward mobility.
For example, the Obama administration has been employing clandestine policies to cut off easy access to cash by systematically eliminating alternative lending options. In August 2013, the Wall Street Journal reported that the Justice Department was “targeting banks that service a broad range of what it considers questionable financial ventures, including online payday lenders.” Additionally, banks like Capital One have already closed the accounts of check-cashing companies. By going after these companies, hardworking Hispanics without a bank account may not have a place to cash their paychecks.
This affects anyone who finds themselves strapped for cash, including self-employed and blue-collar workers. The administration’s regulatory assault is not an assault on the short-term lending industry, but rather on any consumer who relies on having access to cash in cash flow emergencies, especially in underserved communities. For example, two-thirds of all Hispanics work in the service industry, and they will feel the brunt of these policies more than others. In addition, alternative lenders can cater to newer immigrants without substantial credit histories — a demographic that banks fail to serve.
Contrary to the administration’s claim that these targeted financial businesses have a “disparate impact” on minorities, the truth is that these heavy-handed regulations will have a disparate impact on the country’s minorities, many of which live in communities with limited access to traditional banks. And the answer is not capping rates or creating artificial “waiting periods” as the controversial Consumer Financial Protection Bureau has considered. Those remedies will ultimately ensure that the companies will stop providing these services since they are no longer profitable.
In addition to restricting financial options for blue-collar workers, lending regulation will also hurt small-business owners and entrepreneurs, an area where Hispanics have contributed greatly to the American economy. Hispanic entrepreneurs fortified the U.S. economy by an estimated $468 billion last year. This has been pivotal for the nation’s economy, especially in the face of the economic recession.
For frame of reference, from 2010 to 2012, the total number of American entrepreneurs declined by 250,000. Yet in the same period, there were 160,000 new Hispanic entrepreneurs in the U.S.
From 1990 to 2012, entrepreneurship among Hispanics multiplied nearly 10 times that of the general population. Many of them utilized these alternative loan products for quick access to capital, capital that is harder than ever to receive from traditional banks due to the passage of the Dodd-Frank Act.
Targeting payday lenders is only the tip of the iceberg of the administration’s broader initiative, which they tellingly named Operation Choke Point, a maneuver designed to literally choke private businesses at their financial wellsprings by intimidating banks and lending institutions into compliancy. These purely political maneuvers hold no promise for actual economic recovery.
In addition to targeting short-term lenders, another goal of the Obama Administration’s Operation Choke Point is to obstruct multi-level marketing companies, where new entrepreneurs often get their start.
Take Herbalife, a company where Hispanics make up 60 percent of direct sellers. The administration opts to gut profitable companies, condemning sales practices that they judge to be inferior while at the same time initiating no real recovery measures. These policies hurt minorities, who disproportionately make up the lower echelon of workers that are forced to seek irregular forms of employment.
Government agencies and the folks who seek to empower them with more control over the lives of ordinary people are quick to claim “disparate impact” as a justification for their regulatory excesses. But in order to understand the full story, policymakers should look at the impact those very same regulations have on the economy at large, all the people whose jobs and livelihoods are tied to the impacted industries, and the disparate impact the destruction of those industries will have on underserved communities all across the country.
Without a sane analysis, efforts like Operation Choke Point can really only be interpreted as political operatives prioritizing an ideological crusade over an interest in actual economic recovery.
Now for the Choke Tube component, it is the gun dealers and the parts dealers……the backdoor method to infringe again on the 2nd Amendment.
BankUnited N.A., which dropped Top Gun Firearms Training & Supply in Miami from its customer list, declined to comment.
In a statement to The Washington Times, Bank of America said: “We would not deny banking services to an organization solely on the basis of its industry.”
The banking giant blamed a misunderstanding with the Arizona gun manufacturers McMillan Group International and American Spirit Arms.
However, the American Banking Association, the industry’s advocacy group in Washington, said businesses deemed “risky” will be frozen out of the financial system if the Justice Department continues Operation Choke Point because the regulatory burden and risk of investigation will be too great for less-specialized banks to bear.
“We’re being threatened with a regulatory regime that attempts to foist on us the obligation to monitor all types of transactions,” Richard Riese, a senior vice president at the American Bankers Association, said in the April 28 issue of American Banker. “All of this is predicated on a notion that the banks are a choke point for all businesses.”
In an interview with The Times, Mr. Riese said the cost of doing business with gun retailers outweighs the benefits for some banks, given that regulators deem the industry as “risky,” state laws vary on the sale of guns and ammunition, and the Justice Department’s enforcement.
The Independent Community Bankers of America, an association for small banks, said enforcement actions from the Justice Department are too broad and overly aggressive.
“While preventing fraud is a top concern for community banks, it needs to be balanced with ensuring that businesses and consumers that operate in accordance with applicable laws can still access payment systems,” bankers association President Camden Fine told the Justice Department in an April 7 letter. “ICBA requests that the DOJ suspend Operation Choke Point immediately and focus its resources directly on businesses that may be violating the law, rather than targeting banks providing payment services.”
Justice’s operation threatens to “close access to the financial system to law-abiding businesses, because the mere prospect of an enforcement action is sufficient to cause financial institutions to restrict access to their payment systems to only established companies that present low risks,” the organization said.
‘No statutory authority’
Regulations on the financial industry have increased over the past few years, said Thomas P. Vartanian, chairman of Dechert LLP, a global law firm specializing in regulatory and financial matters.
He noted the chilling effect of overregulation by the Financial Fraud Enforcement Task Force, an interagency behemoth that includes the departments of Commerce, Justice, Labor, Education, Homeland Security and Justice along with the Internal Revenue Service, the Securities and Exchange Commission, the Secret Service, the FBI, the Social Security Administration and the Federal Trade Commission.
“The key to effective regulation is the balancing between too little and too much regulation,” Mr. Vartanian said. “The problem here is that there are now so many regulators, including the Department of Justice, with their fingers on the scales on that balancing act.”
Congressional Republicans say the Obama administration is using its regulatory powers to shutter industries it doesn’t like. Last year, 31 Republicans accused the Justice Department and the Federal Deposit Insurance Corp. of intimidating banks and payment processors to “terminate business relationships with lawful lenders.”
In a March hearing before the Senate Banking, Housing and Urban Affairs subcommittee on consumer protection, Sen. David Vitter, Louisiana Republican, complained that several payday lenders — another industry labeled “risky” by the administration — were being dropped by their banks in his home state.
“There is a determined effort from [the Justice Department] to the regulators to cut off credit and use other tactics to force [payday lenders] out of business,” Mr. Vitter said. “I find that deeply troubling because it has no statutory basis, no statutory authority.”
In a House hearing in April, FDIC acting General Counsel Richard Osterman defended his agency’s definition of what constitutes a “risky” business — subject to money laundering or other criminal behavior — but made it clear that no bank is outright prohibited from serving any such companies.
“We have actually put out a policy statement on this issue to make it very clear from the very top that as long as financial institutions are properly managing their relationships and the risks, they’re neither prohibited nor discouraged from providing these services,” Mr. Osterman said.
“Basically, what we’re saying is, these types of programs can be, can involve high-risk activities that could create litigation risk and reputation risk for financial institutions,” he said. “So, they need to do due diligence to ensure that the folks who they’re banking are acting in a safe and sound manner.”
But the cost of that due diligence, coupled with the threat of a lawsuit for doing business with a customer in an industry the government has defined as risky, is having a chilling effect on legitimate companies such as gun dealers, said Mr. Weinstock, the Hunton & Williams lawyer.
“We are one of the most heavily regulated industries in America,” said Mr. Sirochman of American Spirit Arms. “We have to ship our guns to another federal licensed dealers for pickup. The people that are picking up the rifles have to go through a background check to make sure they don’t have any felonies. You can’t own a gun or pass the background check if you do.
“All this is, is an assault on our Second Amendment rights.”