In part from Wired: Hackers who stole sensitive customer information from the cheating site AshleyMadison.com appear to have made good on their threat to post the data online.
A data dump, 9.7 gigabytes in size, was posted on Tuesday to the dark web using an Onion address accessible only through the Tor browser. The files appear to include account details and log-ins for some 32 million users of the social networking site, touted as the premier site for married individuals seeking partners for affairs. Seven years worth of credit card and other payment transaction details are also part of the dump, going back to 2007. The data, which amounts to millions of payment transactions, includes names, street address, email address and amount paid, but not credit card numbers; instead it includes four digits for each transaction that may be the last four digits of the credit card or simply a transaction ID unique to each charge. AshleyMadison.com claimed to have nearly 40 million users at the time of the breach about a month ago, all apparently in the market for clandestine hookups.
“Ashley Madison is the most famous name in infidelity and married dating,” the site asserts on its homepage. “Have an Affair today on Ashley Madison. Thousands of cheating wives and cheating husbands signup everyday looking for an affair…. With Our affair guarantee package we guarantee you will find the perfect affair partner.”
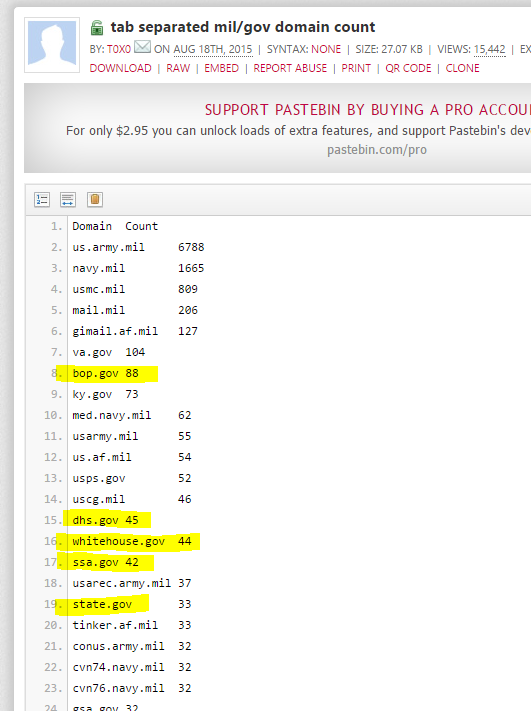
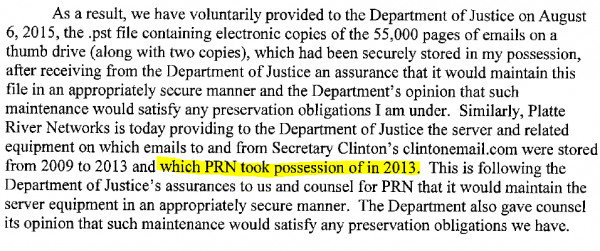
The data released by the hackers includes names, addresses and phone numbers submitted by users of the site, though it’s unclear if members provided legitimate details. A sampling of the data indicates that users likely provided random numbers and addresses, but files containing credit card transactions will yield real names and addresses, unless members of the site used anonymous pre-paid cards. One analysis of email addresses found in the data dump also shows that some 15,000 are .mil. or .gov addresses. Read more here.
Between being unable to respond to terror attacks (Benghazi) and being unable to kill terrorists massing on the Iraq border (ISIS) to being dumb enough to register for an infidelity hook-up site with their White House email accounts.
From Twitter: I’ve come to the conclusion that the Obama administration IS the JV team they warned us to look out for.