Drug cartels heavily rely on GPS devices to track shipments, feds say
The GPS has increasingly become a drug dealer’s new partner in crime.
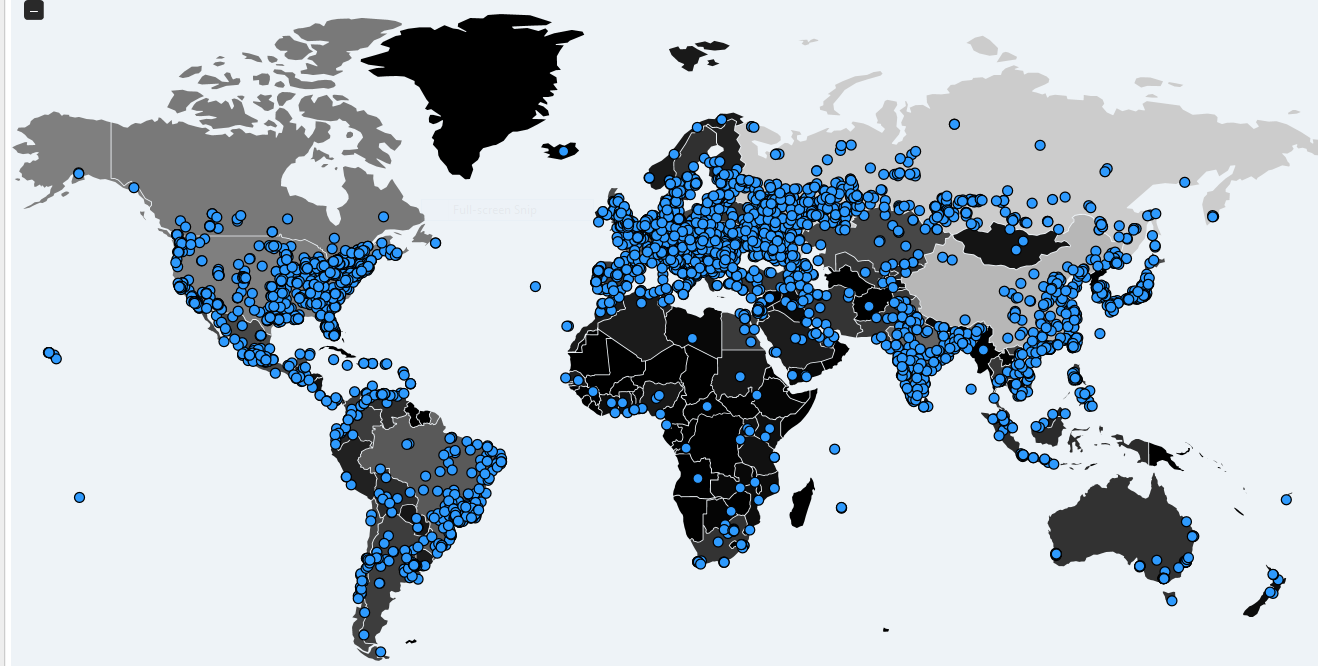
Drug-smuggling groups are relying on the device to keep tabs on drug packages as they wind their way through Central America to the United States, according to published reports.
The criminals attach the drug shipments to buoys, send them off in the Pacific Ocean, and use signals they give off to track a package’s location by using special codes, InSight Crimes reports.
The GPS gives dealers the advantage of having drug shipments picked up by others monitoring their movements without being detected by authorities.
GPS devices are also allowing drug cartels to keep track of lower-level smugglers to ensure they are doing what they were told, say U.S. officials.
Barbara L. Carreno, public affairs officer for the U.S. Drug Enforcement Administration, said drug dealers have been using the tracking device for years. But recently, as the once bulky devices have become smaller and cheaper, their use has increased, she said.
“Traffickers need to know that their mules are doing what they are supposed to do and delivering their very valuable shipments where they are supposed to go,” Carreno said. “We often find GPS devices in shipments we seize.”
Traffickers won’t use a computerized system that would lead law enforcement back to them or create records that would implicate them.
The GPS is simple enough, the DEA says, that it actually eludes more sophisticated tools used for drug interdictions by government agencies of various countries.
“Traffickers wouldn’t use a computerized system that would lead law enforcement back to them or create records that would implicate them,” Carreno said. “They want something cheap, unsophisticated and untraceable.”
Salvadoran officials say that Ecuadorean boatmen have become a core part of the criminal activity. They move the shipments to places off coasts of El Salvador, Guatemala and Costa Rica.
Once the shipments are left at certain locations in the Pacific, traffickers use the GPS to alert those waiting for them by sending information to mobile telephones and computers, the website said, citing the Salvadoran national police’s anti-narcotics division.
One of the most notorious drug kingpins, Ecuador’s Washington Prado Alava, was said by Colombian authorities to have run a highly sophisticated trafficking operation. But his operation, which moved 250 metric tons of cocaine to the United States over a four-year span, was dependent on GPS locators, Insight Crime reported. More here from FNC.
***
Anti-drug forces from several European and American countries intercepted a total of eight tons of cocaine in a double bust that is being dubbed as one of the largest in history.
In the larger one, Spanish authorities cooperated with Ecuadorean police to intercept a ship off that Latin American country bringing more than 5.5 metric tons of cocaine to Spain.
The ship was loaded with Colombian cocaine in the Pacific and planned to travel through the Panama Canal and across the Atlantic to Europe, officials said in a statement.
Una operación de la
@policia junto a la de Ecuador ha permitido interceptar un buque con 5.529 kilos de cocaína y detener a 24 personas.pic.twitter.com/5W5UFrSX9K
In a separate drug seizure, Spanish police stopped a Venezuela-flagged fishing vessel carrying 2.5 metric tons of cocaine near Martinica.
The ship was intercepted on May 4 and was towed to Las Palmas in Spain’s Canary Islands.
The U.S. Drug Enforcement Agency and Britain’s National Crime Agency also took part in the joint operation.
The cargo seized off the coast of Ecuador has an estimated value of $250 million. Ecuadorean agents boarded it when it was almost three nautical miles off Santa Elena province.
Spain’s Interior Minister Juan Ignocio Zoido said to El Pais that the first operation resulted in the capture of 24 suspected drug traffickers.
“It is one of the largest cocaine seizures in history and it takes apart a large drug-trafficking organization between South America and Spain,” he said.
The massive operation began after Spain found out in January that a South American ring with links in Spain was organizing a large shipment.
That information was corroborated by intelligence also gathered by the U.S., Britain and Portugal, the statement said.
Since the beginning of 2017, Ecuador has confiscated about 30 tons of cocaine.
Large seizures of cocaine and cannabis aren’t uncommon in the Iberian Peninsula, which is seen as a drug gateway to Europe.
Spanish police captured almost eight metric tons of cocaine from four vessels in 2015 and 2016 and arrested 80 people, the police statement said.




 Courtesy:
Courtesy: 


