Primer:
The United States Computer Emergency Readiness Team (US-CERT) issued a technical alert about the activity of the North Korea’s ‘Hidden Cobra’ APT group.
The joint Technical Alert (TA) report is the result of the efforts between of the Department of Homeland Security (DHS) and the Federal Bureau of Investigation (FBI).
The US Government has tracked the hacker group as Hidden Cobra, but the APT is most popular as the Lazarus APT Group.
The activity of the Lazarus Group surged in 2014 and 2015, its members used mostly custom-tailored malware in their attacks and experts that investigated on the crew consider it highly sophisticated.
This threat actor has been active since at least 2009, possibly as early as 2007, and it was involved in both cyber espionage campaigns and sabotage activities aimed to destroy data and disrupt systems. Security researchers discovered that North Korean Lazarus APT group was behind recent attacks on banks, including the Bangladesh cyber heist.
According to security experts, the group was behind, other large-scale cyber espionage campaigns against targets worldwide, including the Troy Operation, the DarkSeoul Operation, and the Sony Picture hack.
The joint alert from the FBI and the DHS further details on the group, including indicators of compromise (IoC) for its DeltaCharlie botnet involved in the “Operation Blockbuster” to power DDoS attacks. More here.
*** Most of North Korea’s cyber operations are located in China hosted on Chinese communications internet/communications platforms. It is espionage of an epic standard. But let us go deeper.
Related reading: The North Korea-Cuba Connection including arms sales
Related reading: DPRK-Cuba relations showcase mutual support and solidarity
(Remember, Obama removed Cuba in 2015 from the terror list as a means to establish the process to normalize relations)
*** 
Few think of North Korea as being a prosperous nation. But it is rich in one regard: mineral resources.
Currently North Korea is alarming neighbors with its frequent missile tests, and the US with its attempts to field long-range nuclear missiles that can hit American cities. A sixth nuclear test could be imminent. An attack on the US or its allies would be suicidal, so Pyongyang probably aims to extract “aid” from the international community in exchange for dismantling some of its weaponry—rewind about 10 years to see the last time it pulled off the old “nuclear blackmail” trick.
AP
But however much North Korea could extract from other nations that way, the result would pale in comparison to the value of its largely untapped underground resources.
Below the nation’s mostly mountainous surface are vast mineral reserves, including iron, gold, magnesite, zinc, copper, limestone, molybdenum, graphite, and more—all told about 200 kinds of minerals. Also present are large amounts of rare earth metals, which factories in nearby countries need to make smartphones and other high-tech products.
NKNews
Estimates as to the value of the nation’s mineral resources have varied greatly over the years, made difficult by secrecy and lack of access. North Korea itself has made what are likely exaggerated claims about them. According to one estimate from a South Korean state-owned mining company, they’re worth over $6 trillion. Another from a South Korean research institute puts the amount closer to $10 trillion.
State of neglect
North Korea has prioritized its mining sector since the 1970s (pdf, p. 31). But while mining production increased until about 1990—iron ore production peaked in 1985—after that it started to decline. A count in 2012 put the number of mines in the country at about 700 (pdf, p. 2). Many, though, have been poorly run and are in a state of neglect. The nation lacks the equipment, expertise, and even basic infrastructure to properly tap into the jackpot that waits in the ground.
In April, Lloyd R. Vasey, a senior adviser at the Center for Strategic and International Studies, noted that:
North Korean mining production has decreased significantly since the early 1990s. It is likely that the average operational rate of existing mine facilities is below 30 per cent of capacity. There is a shortage of mining equipment and North Korea is unable to purchase new equipment due to its dire economic situation, the energy shortage and the age and generally poor condition of the power grid.
It doesn’t help that private mining is illegal in communist North Korea, as are private enterprises in general (at least technically). Or that the ruling regime, now led by third-generation dictator Kim Jong-un, has been known to, seemingly on a whim, kick out foreign mining companies it’s allowed in, or suddenly change the terms of agreements.
Despite all this, the nation is so blessed with underground resources that mining makes up roughly 14% of the economy.
A “cash cow”
China is the sector’s main customer. Last September, South Korea’s state-run Korea Development Institute said that the mineral trade between North Korea and China remains a “cash cow” for Pyongyang despite UN sanctions, and that it accounted for 54% (paywall) of the North’s total trade volume to China in the first half of 2016. In 2015 China imported $73 million in iron ore from North Korea, and $680,000 worth of zincin the first quarter of this year.
North Korea has been particularly active in coal mining in recent years. In 2015 China imported about $1 billion worth of coal from North Korea. Coal is especially appealing because it can be mined with relatively simple equipment. Large deposits of the stuff are located near major ports and the border with China, making the nation’s bad transportation infrastructure less of an issue.
For years Chinese buyers have purchased coal from North Korea at far below the market rate. As of last summer, coal shipments to China accounted for about 40% (paywall) of all North Korean exports. But global demand for coal is declining as alternatives like natural gas and renewables gain momentum, and earlier this year Beijing, in line with UN sanctions, began restricting coal imports from its neighbor.
The sanctions game
After North Korea conducted its first nuclear test in 2006, the UN began imposing ever stronger sanctions against it. Last year the nation’s underground resources became a focus. In November 2016, the UN passed a resolution capping North Korea’s coal exports and banning shipments of nickel, copper, zinc, and silver. That followed a resolution in March 2016 banning the export (pdf) of gold, vanadium, titanium, and rare earth metals.
The resolutions targeting the mining sector could hurt the Kim regime. Before they were issued, a 2014 report on the country’s mining sector by the United States Geological Survey noted that (pdf, p. 3), “The mining sector in North Korea is not directly subject to international economic sanctions and is, therefore, the only legal, lucrative source of investment trade available to the country.”
That is no longer the case.
Of course, Pyongyang has grown adept at evading such sanctions, especially through shipping. Glimpses of its covert activities come from occasional interceptions of vessels. Last August Egyptian authorities boarded a ship laden with 2,300 tons (2,087 metric tons) of iron ore heading from North Korea to the Suez Canal (they also found 30,000 rocket-propelled grenades below the ore).
Earlier this year a group of UN experts concluded that North Korea, despite sanctions, continues to export banned minerals. They determined, as well, that North Korea uses another mineral—gold—along with cash to “entirely circumvent the formal financial sector.”
Interested neighbors
Meanwhile China’s overall trade with North Korea actually increased 37.4% (paywall) in the first quarter compared to the same period last year. Its imports of iron ore from North Korea shot up 270% in January and February from a year ago. Coal dropped 51.6%.
North Korea’s neighbors have long had their eyes on its bonanza of mineral wealth. About five years ago China spent some $10 billion on an infrastructure project near the border with North Korea, primarily to give it easier access to the mineral resources. Conveniently North Korea’s largest iron ore deposits, in Musan County, are right by the border. An analysis of satellite images published last October by 38 North, a website affiliated with Johns Hopkins University, showed mining activity was alive and well in the area.
China particularly covets North Korea’s rare earth minerals. Pyongyang knows this. It punished Beijing in March by suspending exports of the metals to China in retaliation for the coal trade restrictions.
Meanwhile Russia, which also shares a (smaller) border with North Korea, in 2014 developed plans to overhaul North Korea’s rail network in exchange for access to the country’s mineral resources. That particular plan lost steam (pdf, p. 8), but the general sentiment is still alive.
But South Korea has its own plans for the mineral resources. It sees them as a way to help pay for reunification (should it finally come to pass), which is expected to take decades and cost hundreds of billions or even trillions of dollars. (Germany knows a few things about that.) Overhauling the North’s decrepit infrastructure, including the aging railway line, will be part of the enormous bill.
In May, South Korea’s Ministry of Land, Infrastructure and Transport invited companies to submit bids on possible infrastructure projects in North Korea, especially ones regarding the mining sector. It argued that (paywall) the underground resources could “cover the expense of repairing the North’s poor infrastructure.”
It was, of course, jumping the gun a bit. For now South Korea—and the world—is stuck with a bully in the mineral-blessed North.
***
China is undergoing a major military build up around the world and has even included collaboration with Pakistan.
The new assessment focuses instead on the buildup on Spratly Islands, noting that previous year the Mischief, Subi and Fiery Cross Reefs, three of the largest outposts, saw the construction of 24 administration buildings, barracks, fixed weapons positions, communication facilities and fighter-sized hangars by China, each of them with runways 8,800 feet long.
While the report notes that China has not undertaken any new land reclamation projects on disputed features in the South China Sea during 2016, it did accuse China of further militarizing the contested Spratly Islands via the construction of 24 hangars capable of housing fighter aircraft, fixed weapons positions, barracks and communication facilities.
Beijing has opposed the deployment of a U.S. missile shield in South Korea to defend against attacks from North Korea, in part because it says it could be used to counter China’s capabilities.
Meanwhile Pakistan itself has not made any comments about this statement.
Published Tuesday, the Pentagon report estimated that China spent US$180 billion previous year on its military – the world’s largest – a figure well over the country’s official US$140 billion defence budget.
The report made “irresponsible remarks on China’s national defense development and reasonable actions in defending our territorial sovereignty and security interests in disregard of the facts“, foreign ministry spokeswoman Hua Chunying told reporters yesterday.
“China likely will seek to establish additional military bases in countries with which it has longstanding, friendly relationships“, the report predicts.
China has cited anti-piracy patrolling as one of the reasons for developing what it calls a naval logistics center in Djibouti.
“China’s expanding global economic interests are increasing demands for the [Chinese Navy] to operate in more distant maritime environments to protect Chinese citizens, investments, and critical sea lines of communication”, the report reads.
The defence ministry in a statement refuted the U.S. assessment, saying “China is not doing any military expansion and does not seek a sphere of influence”. Pakistan has also emerged as the biggest market for Chinese arms exports, a focus area in Beijing’s expansion plans, the report titled “Military and Security Developments Involving the People’s Republic of China 2017″, said. He harshly criticized China’s construction in the South China Sea and became the first member of President Donald Trump’s cabinet to lay out a comprehensive strategy on Asia. That region accounted for almost half of China’s over $20 billion in arms exports from 2011 to 2015.
Countries including Pakistan and Afghanistan welcome it as a path out of poverty. “To support this modernisation, China uses a variety of methods to acquire foreign military and dual-use technologies, including cyber theft, targeted foreign direct investment and exploitation of the access of private Chinese nationals to such technologies”, the report said.
Regarding the Senkaku Islands, a group of East China Sea islets controlled by Japan but claimed by the mainland and Taiwan, the Pentagon said that previous year Beijing continued to use law-enforcement ships and aircraft to “patrol” near the islands in an attempt to undermine Japan’s administration of them.
China has also always been a strong military, economic, and diplomatic supporter of Pakistan and is considered Islamabad’s largest trade and defense partner.

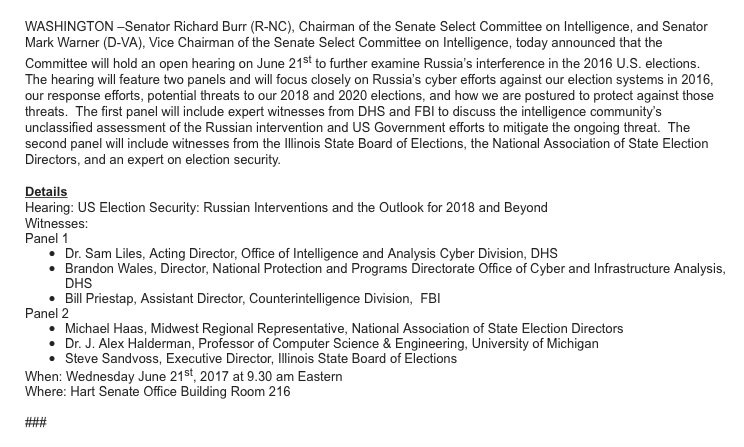 At least there is a hearing to begin the discussion to harden the software systems related to election processes from further intrusions as 2018 and 2020 approaches.
At least there is a hearing to begin the discussion to harden the software systems related to election processes from further intrusions as 2018 and 2020 approaches.
.jpg)
 FoxLatino
FoxLatino