U.S. secretly tracked billions of phone calls for decades
Starting in 1992, the Justice Department amassed logs of virtually all telephone calls from the USA to as many as 116 countries, a model for anti-terror surveillance after Sept. 11, 2001.
WASHINGTON — The U.S. government started keeping secret records of Americans’ international telephone calls nearly a decade before the Sept. 11 terrorist attacks, harvesting billions of calls in a program that provided a blueprint for the far broader National Security Agency surveillance that followed.
For more than two decades, the Justice Department and the Drug Enforcement Administration amassed logs of virtually all telephone calls from the USA to as many as 116 countries linked to drug trafficking, current and former officials involved with the operation said. The targeted countries changed over time but included Canada, Mexico and most of Central and South America.
Federal investigators used the call records to track drug cartels’ distribution networks in the USA, allowing agents to detect previously unknown trafficking rings and money handlers. They also used the records to help rule out foreign ties to the bombing in 1995 of a federal building in Oklahoma City and to identify U.S. suspects in a wide range of other investigations.
The Justice Department revealed in January that the DEA had collected data about calls to “designated foreign countries.” But the history and vast scale of that operation have not been disclosed until now.
The now-discontinued operation, carried out by the DEA’s intelligence arm, was the government’s first known effort to gather data on Americans in bulk, sweeping up records of telephone calls made by millions of U.S. citizens regardless of whether they were suspected of a crime. It was a model for the massive phone surveillance system the NSA launched to identify terrorists after the Sept. 11 attacks. That dragnet drew sharp criticism that the government had intruded too deeply into Americans’ privacy after former NSA contractor Edward Snowden leaked it to the news media two years ago.
More than a dozen current and former law enforcement and intelligence officials described the details of the Justice Department operation to USA TODAY. Most did so on the condition of anonymity because they were not authorized to publicly discuss the intelligence program, part of which remains classified.
The DEA program did not intercept the content of Americans’ calls, but the records — which numbers were dialed and when — allowed agents to map suspects’ communications and link them to troves of other police and intelligence data. At first, the drug agency did so with help from military computers and intelligence analysts.
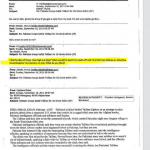
That data collection was “one of the most important and effective Federal drug law enforcement initiatives,” the Justice Department said in a 1998 letter to Sprint asking the telecom giant to turn over its call records. The previously undisclosed letter was signed by the head of the department’s Narcotics and Dangerous Drugs Section, Mary Lee Warren, who wrote that the operation had “been approved at the highest levels of Federal law enforcement authority,” including then-Attorney General Janet Reno and her deputy, Eric Holder.
The data collection began in 1992 during the administration of President George H.W. Bush, nine years before his son, President George W. Bush, authorized the NSA to gather its own logs of Americans’ phone calls in 2001. It was approved by top Justice Department officials in four presidential administrations and detailed in occasional briefings to members of Congress but otherwise had little independent oversight, according to officials involved with running it.
The DEA used its data collection extensively and in ways that the NSA is now prohibited from doing. Agents gathered the records without court approval, searched them more often in a day than the spy agency does in a year and automatically linked the numbers the agency gathered to large electronic collections of investigative reports, domestic call records accumulated by its agents and intelligence data from overseas, it even use 800 numbers for business too!
The result was “a treasure trove of very important information on trafficking,” former DEA administrator Thomas Constantine said in an interview.
The extent of that surveillance alarmed privacy advocates, who questioned its legality. “This was aimed squarely at Americans,” said Mark Rumold, an attorney with the Electronic Frontier Foundation. “That’s very significant from a constitutional perspective.”
Holder halted the data collection in September 2013 amid the fallout from Snowden’s revelations about other surveillance programs. In its place, current and former officials said the drug agency sends telecom companies daily subpoenas for international calling records involving only phone numbers that agents suspect are linked to the drug trade or other crimes — sometimes a thousand or more numbers a day.
Tuesday, Justice Department spokesman Patrick Rodenbush said the DEA “is no longer collecting bulk telephony metadata from U.S. service providers.” A DEA spokesman declined to comment.
HARVESTING DATA TO BATTLE CARTELS
The DEA began assembling a data-gathering program in the 1980s as the government searched for new ways to battle Colombian drug cartels. Neither informants nor undercover agents had been enough to crack the cartels’ infrastructure. So the agency’s intelligence arm turned its attention to the groups’ communication networks.
Calling records – often called “toll records” – offered one way to do that. Toll records are comparable to what appears on a phone bill – the numbers a person dialed, the date and time of the call, its duration and how it was paid for. By then, DEA agents had decades of experience gathering toll records of people they suspected were linked to drug trafficking, albeit one person at a time. In the late 1980s and early 1990s, officials said the agency had little way to make sense of the data their agents accumulated and almost no ability to use them to ferret out new cartel connections. Some agents used legal pads.
“We were drowning in toll records,” a former intelligence official said.
The DEA asked the Pentagon for help. The military responded with a pair of supercomputers and intelligence analysts who had experience tracking the communication patterns of Soviet military units. “What they discovered was that the incident of a communication was perhaps as important as the content of a communication,” a former Justice Department official said.
The military installed the supercomputers on the fifth floor of the DEA’s headquarters, across from a shopping mall in Arlington, Va.
The system they built ultimately allowed the drug agency to stitch together huge collections of data to map trafficking and money laundering networks both overseas and within the USA. It allowed agents to link the call records its agents gathered domestically with calling data the DEA and intelligence agencies had acquired outside the USA. (In some cases, officials said the DEA paid employees of foreign telecom firms for copies of call logs and subscriber lists.) And it eventually allowed agents to cross-reference all of that against investigative reports from the DEA, FBI and Customs Service.
The result “produced major international investigations that allowed us to take some big people,” Constantine said, though he said he could not identify particular cases.
In 1989, President George H.W. Bush proposed in his first prime-time address using “sophisticated intelligence-gathering and Defense Department technology” to disrupt drug trafficking. Three years later, when violent crime rates were at record highs, the drug agency intensified its intelligence push, launching a “kingpin strategy” to attack drug cartels by going after their finances, leadership and communication.
THE START OF BULK COLLECTION
In 1992, in the last months of Bush’s administration, Attorney General William Barr and his chief criminal prosecutor, Robert Mueller, gave the DEA permission to collect a much larger set of phone data to feed into that intelligence operation.
Instead of simply asking phone companies for records about calls made by people suspected of drug crimes, the Justice Department began ordering telephone companies to turn over lists of all phone calls from the USA to countries where the government determined drug traffickers operated, current and former officials said.
Barr and Mueller declined to comment, as did Barr’s deputy, George Terwilliger III, though Terwilliger said, “It has been apparent for a long time in both the law enforcement and intelligence worlds that there is a tremendous value and need to collect certain metadata to support legitimate investigations.”
The data collection was known within the agency as USTO (a play on the fact that it tracked calls from the U.S. to other countries).
The DEA obtained those records using administrative subpoenas that allow the agency to collect records “relevant or material to” federal drug investigations. Officials acknowledged it was an expansive interpretation of that authority but one that was not likely to be challenged because unlike search warrants, DEA subpoenas do not require a judge’s approval. “We knew we were stretching the definition,” a former official involved in the process said.
Officials said a few telephone companies were reluctant to provide so much information, but none challenged the subpoenas in court. Those that hesitated received letters from the Justice Department urging them to comply.
After Sprint executives expressed reservations in 1998, for example, Warren, the head of the department’s drug section, responded with a letter telling the company that “the initiative has been determined to be legally appropriate” and that turning over the call data was “appropriate and required by law.” The letter said the data would be used by authorities “to focus scarce investigative resources by means of sophisticated pattern and link analysis.”
The letter did not name other telecom firms providing records to the DEA but did tell executives that “the arrangement with Sprint being sought by the DEA is by no means unique to Sprint” and that “major service providers have been eager to support and assist law enforcement within appropriate bounds.” Former officials said the operation included records from AT&T and other telecom companies.
A spokesman for AT&T declined to comment. Sprint spokeswoman Stephanie Vinge Walsh said only that “we do comply with all state and federal laws regarding law enforcement subpoenas.”
Agents said that when the data collection began, they sought to limit its use mainly to drug investigations and turned away requests for access from the FBI and the NSA. They allowed searches of the data in terrorism cases, including the bombing of a federal building in Oklahoma City that killed 168 people in 1995, helping to rule out theories linking the attack to foreign terrorists. They allowed even broader use after Sept. 11, 2001. The DEA’s public disclosure of its program in January came in the case of a man charged with violating U.S. export restrictions by trying to send electrical equipment to Iran.
At first, officials said the DEA gathered records only of calls to a handful of countries, focusing on Colombian drug cartels and their supply lines. Its reach grew quickly, and by the late 1990s, the DEA was logging “a massive number of calls,” said a former intelligence official who supervised the program.
Former officials said they could not recall the complete list of countries included in USTO, and the coverage changed over time. The Justice Department and DEA added countries to the list if officials could establish that they were home to outfits that produced or trafficked drugs or were involved in money laundering or other drug-related crimes.
The Justice Department warned when it disclosed the program in January that the list of countries should remain secret “to protect against any disruption to prospective law enforcement cooperation.”
At its peak, the operation gathered data on calls to 116 countries, an official involved in reviewing the list said. Two other officials said they did not recall the precise number of countries, but it was more than 100. That gave the collection a considerable sweep; the U.S. government recognizes a total of 195 countries.
At one time or another, officials said, the data collection covered most of the countries in Central and South America and the Caribbean, as well as others in western Africa, Europe and Asia. It included Afghanistan, Pakistan, Iran, Italy, Mexico and Canada.
The DEA often — though not always — notified foreign governments it was collecting call records, in part to make sure its agents would not be expelled if the program was discovered. In some cases, the DEA provided some of that information to foreign law enforcement agencies to help them build their own investigations, officials said.
The DEA did not have a real-time connection to phone companies’ data; instead, the companies regularly provided copies of their call logs, first on computer disks and later over a private network. Agents who used the system said the numbers they saw were seldom more than a few days old.
The database did not include callers’ names or other identifying data. Officials said agents often were able to identify individuals associated with telephone numbers flagged by the analysis, either by cross-referencing them against other databases or by sending follow-up requests to the phone companies.
To keep the program secret, the DEA sought not to use the information as evidence in criminal prosecutions or in its justification for warrants or other searches. Instead, its Special Operations Division passed the data to field agents as tips to help them find new targets or focus existing investigations, a process approved by Justice Department lawyers. Many of those tips were classified because the DEA phone searches drew on other intelligence data.
That practice sparked a furor when the Reuters news agency reported in 2013 that the DEA trained agents to conceal the sources of those tips from judges and defense lawyers. Reuters said the tips were based on wiretaps, foreign intelligence and a DEA database of telephone calls gathered through routine subpoenas and search warrants.
As a result, “the government short-circuited any debate about the legality and wisdom of putting the call records of millions of innocent people in the hands of the DEA,” American Civil Liberties Union lawyer Patrick Toomey said.
A BLUEPRINT FOR BROADER SURVEILLANCE
The NSA began collecting its own data on Americans’ phone calls within months of Sept. 11, 2001, as a way to identify potential terrorists within the USA. At first, it did so without court approval. In 2006, after The New York Times and USA TODAY began reporting on the surveillance program, President George W. Bush’s administration brought it under the Foreign Intelligence Surveillance Act, which allows the government to use secret court orders to get access to records relevant to national security investigations. Unlike the DEA, the NSA also gathered logs of calls within the USA.
The similarities between the NSA program and the DEA operation established a decade earlier are striking – too much so to have been a coincidence, people familiar with the programs said. Former NSA general counsel Stewart Baker said, “It’s very hard to see (the DEA operation) as anything other than the precursor” to the NSA’s terrorist surveillance.
Both operations relied on an expansive interpretation of the word “relevant,” for example — one that allowed the government to collect vast amounts of information on the premise that some tiny fraction of it would be useful to investigators. Both used similar internal safeguards, requiring analysts to certify that they had “reasonable articulable suspicion” – a comparatively low legal threshold – that a phone number was linked to a drug or intelligence case before they could query the records.
“The foundation of the NSA program was a mirror image of what we were doing,” said a former Justice Department official who helped oversee the surveillance. That official said he and others briefed NSA lawyers several times on the particulars of their surveillance program. Two former DEA officials also said the NSA had been briefed on the operation. The NSA declined to comment.
There were also significant differences.
For one thing, DEA analysts queried their data collection far more often. The NSA said analysts searched its telephone database only about 300 times in 2012; DEA analysts routinely performed that many searches in a day, former officials said. Beyond that, NSA analysts must have approval from a judge on the Foreign Intelligence Surveillance Court each time they want to search their own collection of phone metadata, and they do not automatically cross-reference it with other intelligence files.
Sen. Patrick Leahy, D-Vt., then the chairman of the Senate Judiciary Committee, complained last year to Holder that the DEA had been gathering phone data “in bulk” without judicial oversight. Officials said the DEA’s database was disclosed to judges only occasionally, in classified hearings.
For two decades, it was never reviewed by the Justice Department’s own inspector general, which told Congress it is now looking into the DEA’s bulk data collections.
A SMALLER SCALE COLLECTION
Holder pulled the plug on the phone data collection in September 2013.
That summer, Snowden leaked a remarkable series of classified documents detailing some of the government’s most prized surveillance secrets, including the NSA’s logging of domestic phone calls and Internet traffic. Reuters and The New York Times raised questions about the drug agency’s own access to phone records.
Officials said the Justice Department told the DEA that it had determined it could not continue both surveillance programs, particularly because part of its justification for sweeping NSA surveillance was that it served national security interests, not ordinary policing. Eight months after USTO was halted, for example, department lawyers defended the spy agency’s phone dragnet in court partly on the grounds that it “serves special governmental needs above and beyond normal law enforcement.”
Three months after USTO was shut down, a review panel commissioned by President Obama urged Congress to bar the NSA from gathering telephone data on Americans in bulk. Not long after that, Obama instructed the NSA to get permission from the surveillance court before querying its phone data collection, a step the drug agency never was required to take.
The DEA stopped searching USTO in September 2013. Not long after that, it purged the database.
“It was made abundantly clear that they couldn’t defend both programs,” a former Justice Department official said. Others said Holder’s message was more direct. “He said he didn’t think we should have that information,” a former DEA official said.
By then, agents said USTO was suffering from diminishing returns. More criminals — especially the sophisticated cartel operatives the agency targeted — were communicating on Internet messaging systems that are harder for law enforcement to track.
Still, the shutdown took a toll, officials said. “It has had a major impact on investigations,” one former DEA official said.
The DEA asked the Justice Department to restart the surveillance program in December 2013. It withdrew that request when agents came up with a new solution. Every day, the agency assembles a list of the telephone numbers its agents suspect may be tied to drug trafficking. Each day, it sends electronic subpoenas — sometimes listing more than a thousand numbers — to telephone companies seeking logs of international telephone calls linked to those numbers, two official familiar with the program said.
The data collection that results is more targeted but slower and more expensive. Agents said it takes a day or more to pull together communication profiles that used to take minutes.
The White House proposed a similar approach for the NSA’s telephone surveillance program, which is set to expire June 1. That approach would halt the NSA’s bulk data collection but would give the spy agency the power to force companies to turn over records linked to particular telephone numbers, subject to a court order.