*****
Working document:
To: Interested parties
RE: DNC Structure
STRUCTURE
I would suggest you consider two staffing structures for the DNC:
- CEO onlyIf this is the chosen structure, I would recommend finding a new CEO.
- Under this scenario, the CEO would be accountable for all functions of the DNC—money, general election, and party/convention affairs. She or he would need to hire a General Election Director to help with general election planning and programs, but would remain ultimately accountable to the Chair for everything in the building.
- CEO and General Election DirectorI would then suggest hiring a General Election Director, who would report directly to the Chair on all general election matters (a job scope is attached), including all budgeting, spending, and cash flow for the joint fundraising committee with the campaign. This would be “your person” at the DNC and she or he would work directly with your campaign manager on organizing a general election strategy and getting battleground state parties and the DNC up to snuff. This person would be the final decision maker at the DNC on how the joint committee money is spent and would do so in coordination with your campaign.
- In this scenario, I would suggest keeping Amy Dacey as CEO and make her responsible for all party affairs and meetings, the convention, and basic DNC operations (compliance, the building, etc). I suggest keeping Amy because she is already familiar with the rhythm and functions of the DNC, such as the Rules and Bylaws process, the quarterly party meetings, and the convention. These functions are important to the DNC as an institution, especially to the DNC members, but they aren’t particularly important to you if you decide to run. Keeping Amy at the DNC would also allow White House to have someone in the building to look after their needs, such as polling.
Recommendation: I would recommend the second option, since party affairs and the convention are incredibly time consuming and would probably distract from general election planning (i.e. you don’t want the person in charge of figuring out how to win Florida and Ohio taking a week to look at convention sites). You also don’t want the politics of the DNC itself to disrupt or derail your general election effort.
STAFFING OPTIONS
Options for Chair
- Stephanie Shriock, President of EMILY’s List
- Jennifer Granholm, former Governor of Michigan
- Ted Strickland, former Governor of Ohio
- NEED OTHER OPTIONS
CEO or General Election Director
- Kelly Ward, current Executive Director of DCCC
- Mitch Stewart, 270 Strategies, former Battleground States Director for OFA 12
- Jeremy Bird, 270 Strategies, former Field Director for OFA 12
- Marlon Marshall, former Dep. Field Director for OFA 2012
- Buffy Wicks, current ED of Priorities, USA
Other key staff:
- Finance Director: recommend keeping Jordan Kaplan
- Data and Technology Director: recommend keeping Andrew Brown
- Communications and Research: recommend assessment; potentially bring in some enhanced research capacity
- Voter protection director: recommend a new Voter Protection Director
- Political Director: recommend a new Political Director
TIMING
I would suggest aiming to have a General Election Director in place by the beginning of December, so he or she can attend immediately to some urgent voter protection and research matters. The role could be announced at the December Executive Committee meeting.
A new Chair is slightly less urgent in my opinion. I would certainly make the change by the February DNC meeting, but would probably defer to the White House on what timing they prefer.
- Executive Committee December 5-6, Hollywood, FL
- Full Meeting Week of Feb 18 (tent), Washington, DC
General Election Director
Job Scope
- General election analytics and planning
- Analytics and polling in each battleground state to identify the actual battleground map
- Identify off year-work (probably voter registration) that should be done to support the 2016 strategy
- Start creating turnout and support models for the general election
- General election data hygiene and systems
- Analytics capability for matched data (user capacity, candidate confidentiality)
- VAN/NGP technical updates
- Update key tools: make a plan, commit to vote, voter registration, polling place look up, etc.
- Coordination with campaigns on who is completing what engineering projects; ensuring that all systems will be compatible in the general election
- Opposition research
- Identify next steps on opposition research
- Ensure all collection and record request work has been completed
- Setting up a permanent tracking structure (whether that involves purchasing tracking or doing it in house)
- Technology and digital
- Update key online GOTV tools
- Ensure updates to the voter file are completed on time
- Ensure all DNC data systems can synch perfectly with the campaign
- Complete all necessary updates to internal database tools like voter protection incident tracking
-
-
- Coordination with allies
- Coordination on state ballot referenda
- Aligning around general election goals/plan/targeting/best practices
- Ensuring data systems will be compatible, where possible
- Identifying staff for general election field and state organizations
-
- Ironing out state party operational issues
- Helping
- Transfer down MOUs for battleground states completed in the off year
- Indemnification
- Approval of direct mail
- Administrative overhead
- Using SPP for accountability re: the items above?
- Aligning state party staff with critical projects (voter protection, registration, etc)
- Joint fundraising account money management and supervision
- Voter registration projects in battleground states (where needed)
- Directly oversee development of any state strategy
- Hire project leader
- Oversee progress to goals
- Oversee budget for the program
-
-
- Coordination with Voting Rights Trust on litigation
- Florida
- North Carolina
- Wisconsin
- Ohio
- Nevada (Reid coordination)
- Michigan?
-
-
- Coordination with voter protection ballot referenda program
- Ohio (State Director and team)
- Florida (State Director and team)
- Michigan?
- Colorado?
- Missouri?
- Arizona?
- Political and research work for voter protection
- State FOIA project
- Plaintiff recruitment
- Earned media and political advocacy management (esp. Florida)
- Coordinating with Perkins Coie staff on state legislative threat monitoring
- Voting law changes
- Electoral vote allocations (esp PA and WI)
*****
To: Interested parties
Re: Threat assessment
PRIMARY ELECTION
- Message
- Higher concerns
- Authenticity
- Emily’s List: “Panelists have about whether HRC is personally trustworthy: tells the truth, levels with people, is sincere in her motivations”.
- “Relatability”
- Emily’s List: “When voters think about HRC’s positives, they do not instinctively think about what she cares about…when pressed panelists say they do not necessarily think of HRC as “relatable” and tend to describe her personally as more ‘cold’ than ‘warm’”. But respondents are quick to say they do not have a feel HRC as a person. They are intrigued by details like ‘she shops at Target’”.
- Emily’s List: “The focus groups make clear, however, that winning the voters’ trust on the economy is not only a matter of having a plan. A successful candidate must also show that s/he personally understands the struggles and concerns voters experience in today’s economy and that s/he is on their side”
- Not a clear/credible vision, including clarity on Obama
- Emily’s List: “It will be essential for her to articulate a more specific economic agenda that translates these normative values and broad policy directions into a credible plan of action.
- Wall Street/elitism
- Policy and rhetoric on Wall Street (Emily’s List: 22% “Hillary Clinton won’t stand up to the big banks”)
- Personal income and finances
- Foundation fundraising and business connections
- Campaign finance; superpac affiliation
- How to respond to superpac attacks
- Do you need to respond?
- How do you respond when there is no opponent?
- Role of outside groups vs. campaign
- Lower concerns
- Benghazi (only because of upcoming hearings)
- Emily’s List: “Benhgazi raises questions about HRC that relate more to lingering questions about her candor than about the event itself. Voters do not know the details of the incident (other than the fatal outcome) and are not especially eager to learn all the complicated facts…Benghazi can serve as a proxy character issue”.
- Immigration
- Need to be firm and unequivocal
- Will there be a compromise that is unpopular with Hispanics?
- Use of military force: remains very unpopular with Democrats
- Need Simas numbers
- Grand bargain: what if Obama cuts a budget deal that’s unpopular with Democrats?
- Timing
- Oxygen for competitors
- Waiting too long gives competitors time to get the media spotlight and build credibility
- Risk of a reactionary launch
- Lack of infrastructure to manage GOP attacks in Q1 and Q2
- Losing talent to other campaigns/jobs
- People will start to accept other jobs after Thanksgiving
- New DCCC and DSCC leadership and senior staffs; many attractive Senate and House races
- Losing time on technology
- Long term projects like mobile canvassing tools, volunteer engagement ap, etc.
- Fundraising opportunity cost: losing time in Q2
- Geography
- Iowa
- Starting out on the right foot will be key to ice out the competition. This could be challenging if opponents get in early and pick up any steam.
- Potential for caucus goes to want to “make it a race” if there’s a perception that the campaign is not fully invested. Primary opponents will always be more accessible and exciting to the left no matter what.
- South Carolina and early southern primary states: if there’s an African American primary opponent
- Demography
- African Americas (if there’s an African American primary opponent)
- The 2008 Obama primary coalition: younger, better educated, less partisan primary, male voters are less supportive, but still very winnable
| Source:
Emily’s List Dec 2013 |
Support HRC Regardless |
Consider others, but prefer HRC |
Consider HRC, but prefer others |
Likely to support others |
|
|
|
|
|
| Men |
29% |
39% |
15% |
6% |
| Women |
40% |
46% |
6% |
5% |
|
|
|
|
|
| 18-34 |
23% |
45% |
19% |
5% |
| 35-49 |
37% |
45% |
11% |
3% |
| 50-64 |
36% |
44% |
6% |
7% |
| 65+ |
43% |
39% |
6% |
5% |
|
|
|
|
|
| Whites |
33% |
46% |
9% |
5% |
| AA |
42% |
41% |
10% |
3% |
| Hisp |
40% |
36% |
10% |
6% |
|
|
|
|
|
| Strong D |
42% |
43% |
8% |
3% |
| Weaker D |
22% |
42% |
14% |
9% |
- Political
- Potential opponents: Biden, Warren, Patrick, O’Malley, Sanders
- Clumsy launch politics
- Messy labor endorsement process
- Operational
- Clear leadership and decision making; clarity on who speaks for the campaign
- Unhelpful chatter and leaks
GENERAL ELECTION
- Message
- Same issues as the primary, as well as…
- A better GOP candidate than Romney (better profile, more credibly moderate)
- Risk of losing more downscale whites in places like PA and OH
- National environment (largely not controllable)
- President Obama’s approval rating/direction of the country
- Perceived success/failure of foreign policy at the time
- DemographySince we don’t have a lot of polling, it’s most helpful to look at the breakdown of Obama’s vote and figure out how to offset likely changes. Big picture, we have to assume slightly lower performance and turnout among the key “Obama coalition” groups (young people and minorities), which will need to be made up with stronger performance among whites.
- Obama won by driving up turnout and support among key minority groups and getting enough whites to break 50%. Your math to 50% could look similar, but one potential “threat” is that you match Obama’s performance with white voters but don’t achieve his level of turnout or support with other groups.
- White voters: Obama was the first president to win the presidency with less than 40% of the white vote (39%). This was possible because whites are shrinking as a proportion of the electorate, but also because he organized very strong African American turnout and boosted traditionally high levels of support even higher. These proportions with African Americans will likely dip for you, meaning that you will need over 40% of the white vote nationally.
- The GOP candidate will also be a key factor in this equation: Romeny’s profile as a defender of Wall Street and outsourcer helped to suppress support among downscale whites in Pennsylvania, for example. His positions on abortion helped to move persuadable white women to Obama. All these variables will need to be accounted for in determining the win number in each state.
- African Americans: African American performance is a key factor in states like Ohio and Florida , where Obama pushed turnout disproportionately high. We have to anticipate 89% African American support, whereas Obama was in the mid 90s. We also have to anticipate a drop in African American turnout. Romney would have won Ohio, for example, if African American turnout had been at “normal” levels.
- Hispanics: Hispanics are equally key in some states for determining the win number. They performed at or above 70% for Obama nationally. We have to anticipate closer to 65%, although the rhetoric and immigration stance of the GOP candidate will be a major factor. Correctly predicting Hispanic turnout in Colorado, for example, will determine how much we need to worry about a potential rightward swing in the Denver suburbs.
- Young people: level of support and turnout are both major unknowns and need to be examined early. Your level of support is softest with young people, but that could just be because they know the least about you. Extreme GOP views on gay marriage, global warming, and/or birth control could swing and motivate young voters.
- That said, we have to assume a drop in performance and turnout among young voters. The Emily’s List general election poll from last year predicts that you can get 50% or more of voters 65 and older, while Obama only got 44%, which could make up the difference.
- Asians: exit polls showed that Asians performed 70/30 for Obama, but this could move closer to 60% next year since their level of support for Democrats appears to have dipped in 2014. This needs to be researched further.
- Geography
- Lean Democratic states to watch
- Wisconsin: was harder for Obama in 2012 due to Paul Ryan, but Walker’s performance was higher than expected last week. This requires further research.
- Pennsylvania: probably stable, but should be monitored, since downscale whites could sour even more depending on the national mood.
- Battlegrounds to watch
- Colorado: Denver suburbs troubling, GOP carried Jefferson Co. this year.
- Virginia: African American turnout appeared to be disproportionately high last week, but Warner still performed poorly in suburban counties like Loudon, Prince William, Chesterfield.
- Iowa: rural and white, could get worse depending on performance with whites overall and national mood.
- Ohio: Obama won with black turnout in 2012; need to identify a path to winning more whites.
- The 2016 electorate will look completely different than 2014, which was even lower than 2010. That’s why states like Nevada, where Democrats were beaten badly this year, remain favorable for 2016. The breakdown of the battleground has been covered in other documents, but I’ve noted a few states below that could become harder next year based on what we saw in last week’s election returns.
- Changing rules
- Harsher voting restrictions in GOP controlled battleground states
- Florida (Gov has announced a bill already), Ohio, Wisconsin, Nevada, Michigan
- Changes in electoral vote allocations (there are only rumors now)
- Ohio, Michigan, Florida
- Financial
- Full concentration of GOP resources from Day One
- GOP general election spending begins earlier than
****
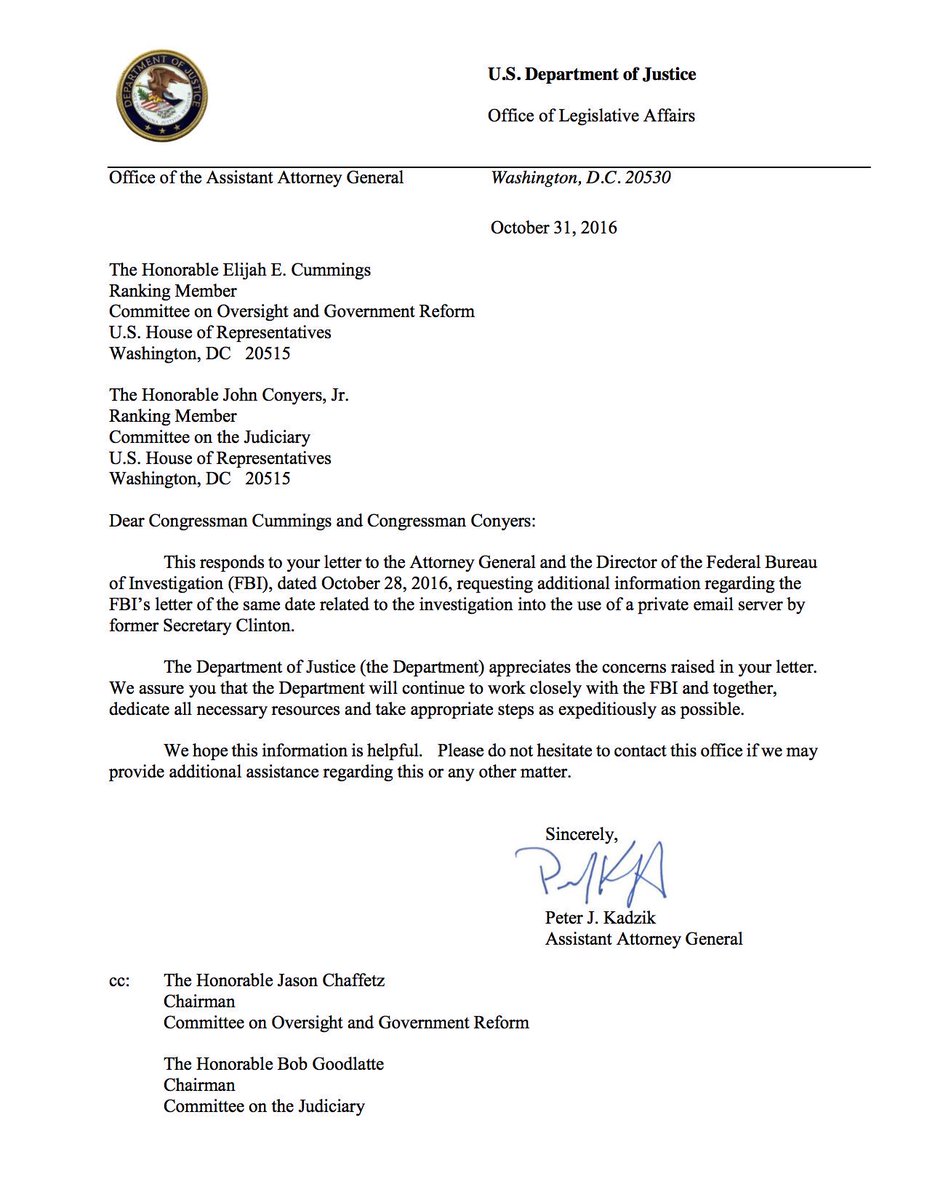
To: Cheryl Mills
Re: Legal Options for launching a potential campaign
SUMMARY
If you decide to run, a number of core functions need to be in place for a successful campaign launch, which have been outlined in previous materials. Ideally, every aspect of the campaign will ramp up as quickly as possible, but three tasks will take a particularly long time and will drive the overall timeline:
- Researching and testing your message
- Developing a brand and logo
- Designing and testing your website and mobile ap
All three tasks are highly intertwined and contain a series of constituent steps, which should be carefully sequenced. As demonstrated by the attached timeline, they will collectively take approximately 19 weeks to complete. The first five weeks can take place do not require any funding or structure, but the last 14 will require some sort of funding mechanism. I would recommend that a CTO, Digital Director, and Media Director are hired within the first four weeks to help shepherd the process.
The launch will require a full leadership team, as well as staff in the early 4 primary states and support staff at headquarters. The attached timeline has them starting a month before the launch and I suggest a formal exploratory be set up a month out to pay for them (and the equipment and overhead that will come with them!).
WHAT NEEDS TO BE ACCOMPLISHED
Message
As we have discussed before, a campaign is fundamentally an organization built to do one thing—communicate a message. The proposed message development process is a series of focus groups, polls, and web tests to develop a narrative, messages, responses to attacks, and even a tagline for the campaign. This process will allow you to hear directly from voters about their mood and what they want from a president. It will also allow you to explore how you can articulate your vision and policy proposals. Lastly, it will help us to put together a path to victory in the primary and general, including key target groups.
Branding and Logo
Based on how you decide to present your candidacy based on the research process, we will engage design firms to develop a logo and branding scheme for all campaign materials that reflect the kind of candidate you are and the audiences we are trying to reach. The brand will dictate what colors, fonts, and moods should be used to design the site and mobile ap.
Website and Mobile Ap Design
Four separate firms will each create three designs for your site using the branding and logo concepts. We will choose one design (or an amalgamation of many) and go through a cycle of edits and feedback to get it exactly right. We will probably want to do some sort of photo shoot and record a video for the site as well.
WHEN TO START
Attached are three alternative timelines. The first begins in December, the second in January and the third in February. All three have the same 19-week timeline and sequence.
I would suggest establishing a date you want to launch and then work back from there. For example, if you want to launch your campaign at the beginning of the second quarter, you should start the ramp up process in December.
Keep in mind that this process will take over four months, which is a long time to keep potential opponents iced out. For example, the winter DNC meeting (which will take place in mid February) traditionally includes a beauty pageant for declared or prospective candidates. You will undoubtedly be asked to speak and we have to assume for planning purposes that Sanders and/or O’Malley will be declared and actively running by that time. Once a launch date is set, it will be worth thinking of what can be done from a communications standpoint to keep the opposition frozen out, even if you won’t declare for a few months.
BUDGET AND SPENDING
As described above, candidate-specific design work will begin in the fifth week of the ramp up process, at which point you will need either personal resources, or an exploratory committee to fund work.
If personal funds are used, spending can be limited to polling, focus groups, web tests, design firms, and some modest staff overhead. The budget below is approximately $1.3 million, but I would assume this will cost $2-3 million due to unforeseen expenses.
Polling and Focus Groups: $800,000
Logo and branding $100,000
Digital design: $200,000
Staff Overhead $200,000
Even if personal funds are used, there will inevitably need to be an exploratory period of about a month for the sole purpose of hiring staff and getting them ready to execute the launch plan. On the day you declare your candidacy, the campaign will need a fully functioning finance, communications, political, and operations/compliance staff. There should also be skeletal staff in the four early states. Overhead for the last month will likely be $3-4 million.
****
More here including the timeline.
Another item to destroy the GOP and includes SEIU operatives:
From:jlrhalpin@gmail.com To: john.podesta@gmail.com, Amy.Dacey@seiu.org, cvarney@hhlaw.com, tmatzzie@gmail.com, anna.burger@seiu.org, mpbonner@bonnergrp.com more tjdaly@bonnergrp.com, mberkowitz@bonnergrp.com, eagle@bonnergrp.com Date: 2007-12-03 19:20 Subject: Revised PowerPoint
Here is a revised PowerPoint based on my discussion with Christine. The script is okay as is but will need to reviewed again if there is any plan to go into more depth on differences between the (c)(4)s and what they will be doing. Please use this version for any additonal changes or updates. Main differences to keep in mind for the presentation or other changes: – The Fund for America has been removed from the corner of all of the slides. – The connections between the Fund for America, the messaging, and the mobilization is not explicit in the org chart (dotted lines removed). – “Building a Permanent Progressive Majority” starts and ends the presenation. – References are all tied to “progressive” voters, issues or targeted states. Thanks, Christine, for your help. Take care – John
The Associated Press
 Just the Facts
Just the Facts



 JOEL SAGET/AFP/Getty
JOEL SAGET/AFP/Getty