Have you read the newly released book titled ‘Bully of Asia’ by Steven W. Mosher? China is the single largest threat to global stability and Russia and Iran in second and third place.
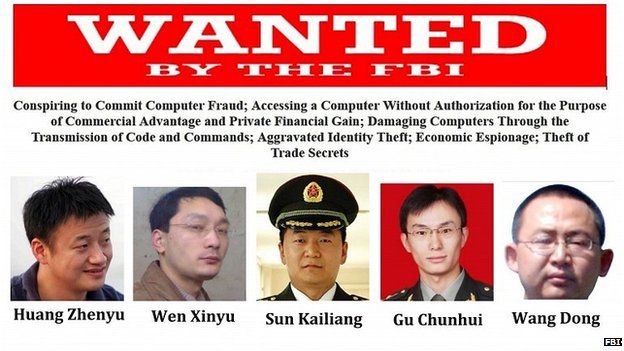
China is a thief. China has dispatched operatives throughout the West under the guise of cultural exchanges, students, temporary workers and journalists. It is all about espionage and cyberwar.
Hey State Department and DHS, get these operatives outta here. By the way, are there any sanctions on China with regard to PLA Unit 61398?
FP: The Johns Hopkins University’s School of Advanced International Studies (SAIS), located just a short walk from Dupont Circle in Washington, D.C., is one of the top international relations schools in the United States. Its graduates feed into a variety of government agencies, from the State Department to the CIA, and the military. Its China studies program is especially well known; many graduates come away with expert knowledge of the language, culture, and politics of the United States’ most important strategic competitor.
In August, SAIS announced a new endowed professorship in the China Studies department as well as a new research project called the Pacific Community Initiative, which aims to examine “what China’s broader role in Asia and the world means for its neighbors and partners.”
What the SAIS press release did not say is that the money for the new initiatives came in part from the China-United States Exchange Foundation (CUSEF), a Hong Kong-based nonprofit. CUSEF is a registered foreign agent bankrolled by a high-ranking Chinese government official with close ties to a sprawling Chinese Communist Party apparatus that handles influence operations abroad, known as the “united front.”
The China-U.S. Exchange Foundation’s partnership with a premier U.S. academic institution comes amid a Chinese Communist Party push to strengthen its influence over policy debate around the globe. The Chinese government has sought to repress ideas it doesn’t like and to amplify those it does, and its efforts have met with growing success.
Even as Washington is embroiled in a debate over Russian influence in U.S. elections, it’s China that has proved adept at inserting itself in American politics.
“The Chinese approach to influence operation is a bit different than the Russian one,” said Peter Mattis, a fellow at the Jamestown Foundation. “The Russian one is much more about an operational objective and they work backward from that objective, saying, ‘How do we achieve that?’” But on the Chinese side, Mattis said, “they focus on relationships — and not on the relationships having specific takeaway value, but that someday, some way, those relationships might become valuable.”
The Chinese seek a kind of “ecological change,” he explained. “If they cultivate enough people in the right places, they start to change the debate without having to directly inject their own voice.”
The China-U.S. Exchange Foundation was founded in 2008 by Tung Chee-hwa, a Hong Kong shipping magnate who later served as the chief executive of the former British colony, where he championed the benefits of close ties to Beijing. Tung’s Hong Kong-based nonprofit conducts academic and professional exchanges, bringing U.S. journalists, scholars, and political and military leaders to mainland China. It also has funded research projects at numerous U.S. institutions, including the Brookings Institution, the Center for Strategic and International Studies, the Atlantic Council, the Center for American Progress, the East-West Institute, the Carter Center, and the Carnegie Endowment for Peace.
Tung’s foundation’s ties to the united front are indirect, but important. Tung currently serves as the vice chairman of one of the united front’s most important entities — the so-called Chinese People’s Political Consultative Conference, which is one of China’s two rubber-stamp assemblies.
The body is one of Beijing’s most crucial tentacles for extending influence.
In its newest project with SAIS, the foundation describes the Pacific Community Initiative as a “joint research project.” David Lampton, director of the university’s China Studies Program, said in an August press release that the new professor “will also be responsible for running our Pacific Community Initiative and work closely with the China-U.S. Exchange Foundation in Hong Kong.”
Lampton also confirmed that CUSEF funded the new programs. “Both the Initiative and the Professorship were made possible through the support of the China-U.S. Exchange Foundation,” he said in an emailed statement to Foreign Policy.
But he denied that CUSEF had attached any intellectual strings to its funding.
“There are absolutely no conditions or limitations imposed upon the Pacific Community Initiative or our faculty members by reason of a gift or otherwise,” Lampton told FP. “We have full confidence in the academic integrity and independence of these endeavors.”
CUSEF denies it acts as a vehicle for Beijing’s ideological agenda or has “any connections” to the united front. “We do not aim to promote or support the policies of any one government,” wrote a spokesperson for the foundation in an email.
This isn’t the first time SAIS and the foundation have worked together; they co-sponsored a conference on China’s economy in Hong Kong in March 2016, according to the school’s website. But a professorship and a major research project offer an opportunity for broader reach — the kind of global influence that Chinese President Xi Jinping has made a centerpiece of his policies. In October, at the meeting of the Communist Party that sets the national agenda for the next five years, Xi called for an expansion of the party’s overseas influence work, referring to the united front as a “magic weapon” of party power.
That quest to shape the global view of China isn’t the same thing as soft power, said James Leibold, a professor at La Trobe University in Melbourne who researches Chinese influence in Australia, where Beijing’s recent influence operations have sparked a national controversy.
China is an authoritarian state where the Communist Party rules with an iron fist, Leibold said — and that is what Beijing is trying to export.
“What we’re talking about here is not Chinese influence per se, but the influence of the Chinese Communist Party.”
In a joint project like the one at SAIS, that influence can be subtle rather than being heavy-handed, said Jamestown’s Mattis. “It’s the ability to privilege certain views over others, to create a platform for someone to speak,” he said. “When you have a role in selecting the platform and generating what I presume they hope are some of the bigger reports on U.S.-China relations in the next few years, that’s important.”
One goal of the joint research project is, in fact, to “yield a white paper to be submitted for endorsement by both the U.S. and Chinese governments,” a CUSEF spokesperson wrote in an emailed statement to FP.
While CUSEF representatives stress that it is not an agent of the Chinese Communist Party, the foundation has cooperated on projects with the the People’s Liberation Army and uses the same Washington public relations firm that the Chinese Embassy does.
One of those PLA projects is the Sanya Initiative, an exchange program that brings together U.S. and Chinese former high-ranking military leaders. On the Chinese side, the Sanya Initiative is led by a bureau of the PLA that engages in political warfare and influence operations, according to Mark Stokes, executive director of the Project 2049 Institute.
Sometimes the results of such high-level exchanges aren’t subtle. In February 2008, PLA participants in the Sanya Initiative asked their U.S. counterparts to persuade the Pentagon to delay publishing a forthcoming report about China’s military buildup, according to a segment excised from the 2011 annual report of the congressional U.S.-China Economic and Security Review Commission.
The U.S. members complied, though their request was not successful.
Exchanges and partnerships are not CUSEF’s only initiatives. As a registered foreign agent, in 2016 it spent just under $668,000 on lobbying, hiring the Podesta Group and other firms to lobby Congress on the topic of “China-U.S. relations.” The foundation has spent $510,000 on lobbying to date in 2017.
CUSEF also keeps on retainer the consulting and public relations firm BLJ Worldwide LTD, the same firm the Chinese Embassy in the United States uses. According to FARA filings, CUSEF currently pays the firm $29,700 a month to promote the foundation’s work and run a pro-Beijing website called China US Focus.
Whether through websites, partnerships, or endowments, China has learned to wrap its message in a palatable wrapper of U.S. academics and intellectuals, according to Mattis.
“Who better to influence Americans than other Americans?” he said.


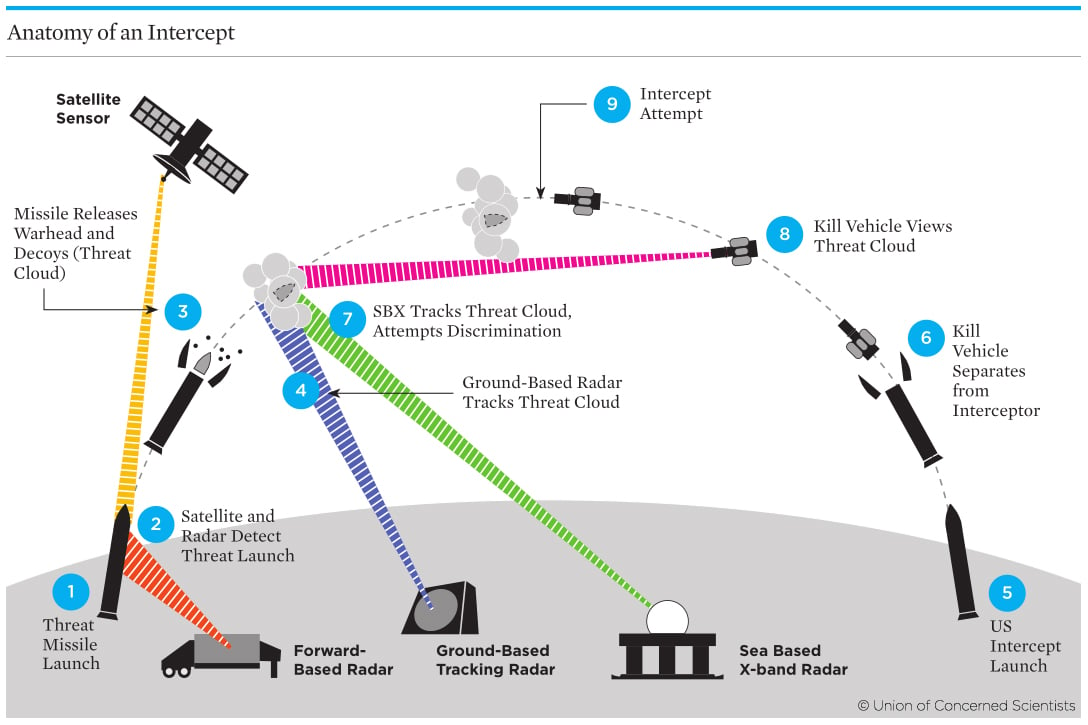 ICBM launches have three distinct phases of flight. During the boost phase, a rocket launches the warhead at high speeds above the atmosphere, where it continues in free-fall through the vacuum of space. The midcourse phase begins with the rocket separating from the warhead, which continues unguided and unpowered, hundreds of miles above the Earth. The reentry, or terminal, phase sees the warhead descend at high speeds back through the Earth’s atmosphere toward the ground.
ICBM launches have three distinct phases of flight. During the boost phase, a rocket launches the warhead at high speeds above the atmosphere, where it continues in free-fall through the vacuum of space. The midcourse phase begins with the rocket separating from the warhead, which continues unguided and unpowered, hundreds of miles above the Earth. The reentry, or terminal, phase sees the warhead descend at high speeds back through the Earth’s atmosphere toward the ground.