Seems there is some talking point being launched that whatever Russia did do with regard to hacking the Democrats…watch out because the actual text could be altered and false…seems Politico is carrying the water for that talking point as well.
Admittedly, Russia does publish false propaganda for sure and the use of Russia Today (RT) and Sputnik News are the go to methods…but in this case….does Russia need to do this? Okay, read on as the Democrats are in fear and setting the table to promote an early new warning.
Democrats’ new warning: Leaks could include Russian lies
The move could help inoculate Hillary Clinton against an October cyber surprise.
Politico: Democratic leaders are putting out a warning that could help inoculate Hillary Clinton against an October cyber surprise: Any future mass leaks of embarrassing party emails might contain fake information inserted by Russian hackers.
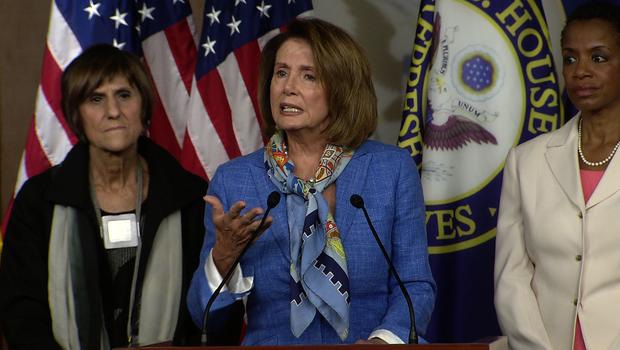
House Minority Leader Nancy Pelosi is among those sounding that alarm, echoing security experts who say Russian security services have been known to doctor documents and images or bury fictitious, damaging details amid genuine information. For hackers to resort to such tactics would be highly unusual, but security specialists say it’s a realistic extension of Moscow’s robust information warfare efforts.
Pelosi aired her concerns during a Saturday night conference call with Democratic lawmakers and aides who had been stung by a dump of their emails and phone numbers, according to a source on the call.
Democratic strategists say the party would be wise to trumpet warnings about faked leaks as it braces for the possibility of hackers releasing damaging information about Clinton or other candidates close to Election Day. Preemptively casting doubt on the leaks may be easier now than trying to mount a full response days before voters go to the polls.
“It is certainly a valid issue to raise, because clearly the people who are doing these attacks have a political agenda that’s against the Democratic Party,” said Anita Dunn, who was White House communications director in the early part of President Barack Obama’s first term.
If Russia is indeed attempting to destabilize Clinton’s candidacy through the widespread digital assault on Democratic institutions — as many researchers believe, and Democrats are alleging, but Moscow strongly denies — “why wouldn’t you want to raise the potential [for tampering]?” asked Dunn, now a partner at communications firm SKDKnickerbocker. “I think it’s only prudent for people to raise that possibility.”
Republicans say Democrats are just trying to distract the public from the most important issue: the content of the leaks. They say the Democrats already tried to do that with the first batch of 20,000 Democratic National Committee emails that leaked in July, which forced the resignation of Chairwoman Debbie Wasserman Schultz after showing that some DNC staffers had favored Clinton over primary rival Sen. Bernie Sanders.
“First, they made it all about Russia instead of the substance of what was actually in the emails,” said Matt Mackowiak, a veteran Republican strategist. Now, he added, “If there is a massive trove of emails or documents relating to the Clinton campaign or the Clinton Foundation … they may just say, ‘Look, the authenticity of the emails hasn’t been confirmed.’”
Intelligence officials — including NSA Director Adm. Michael Rogers and Director of National Intelligence James Clapper — have long argued that data manipulation more broadly is a disturbing possibility, and potentially the next front in both cybercrime and the budding digital warfare between countries.
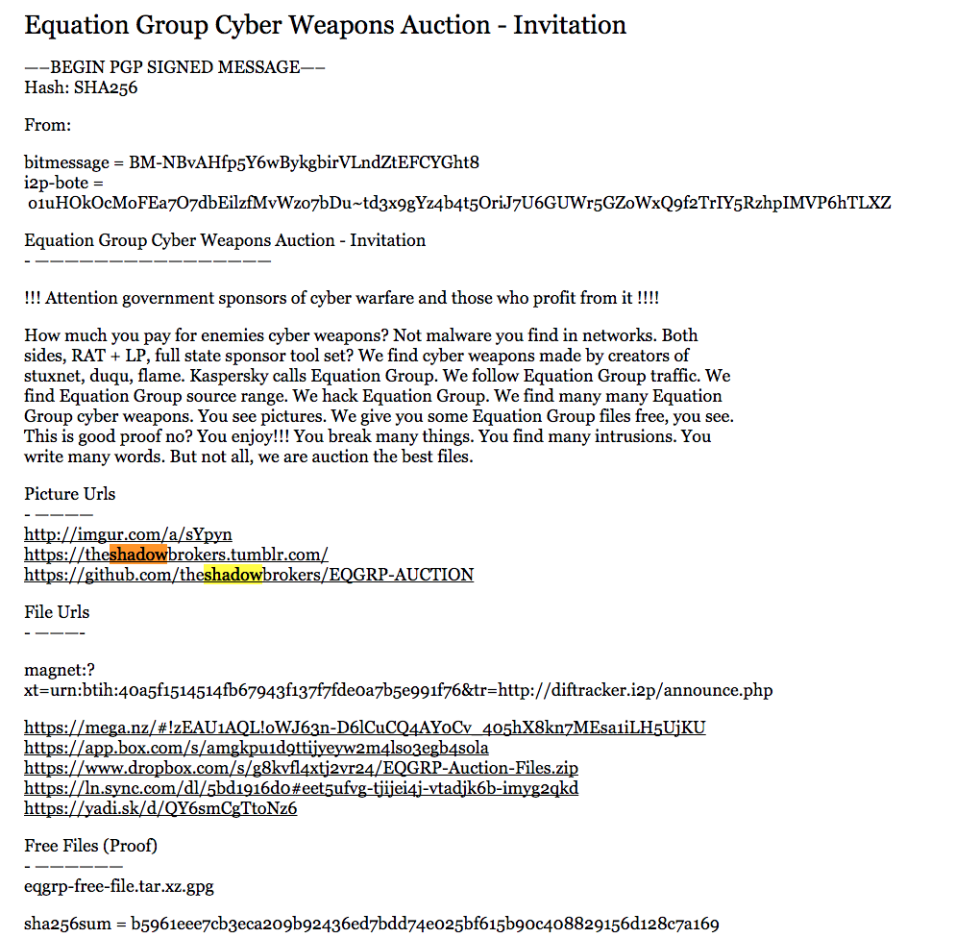
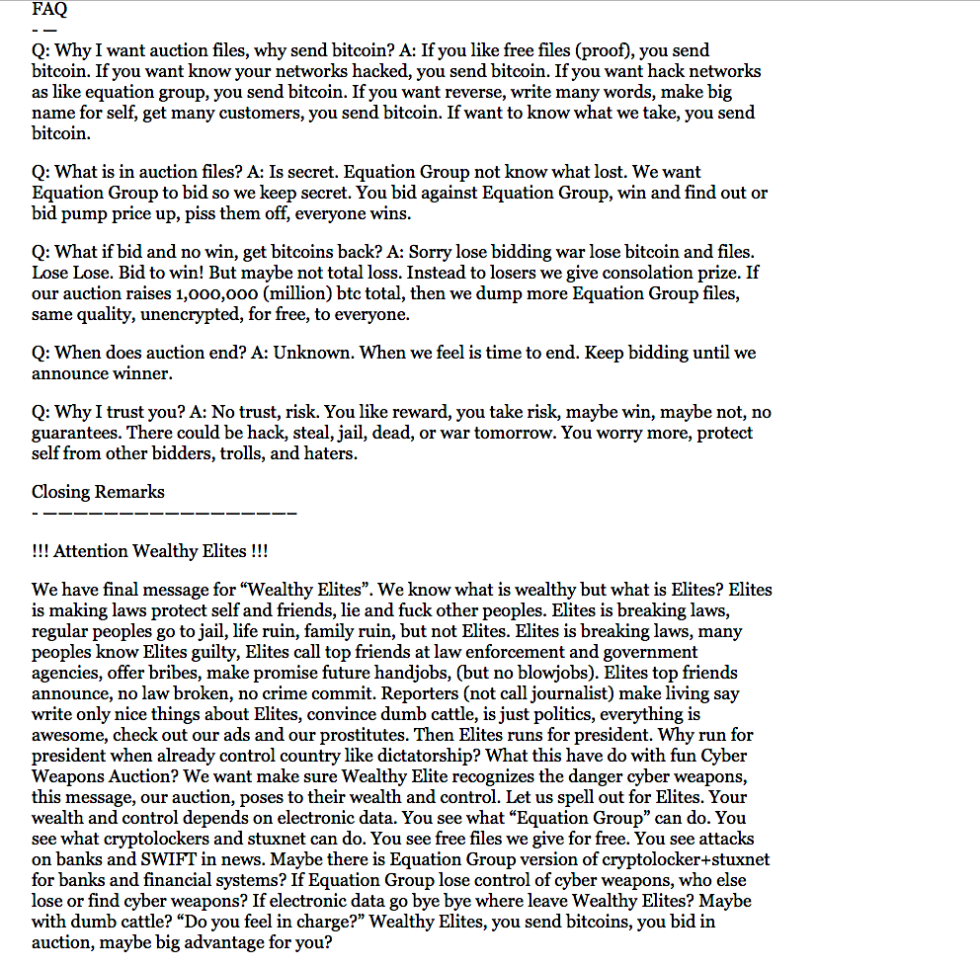
Last month, a bipartisan group of 32 national security experts at the Aspen Institute Homeland Security Group warned of a specific type of fakery following the DNC hack, arguing that the suspected Russian hackers who struck the DNC and the Democratic Congressional Campaign Committee could “salt the files they release with plausible forgeries.”
In Saturday’s call, Pelosi was underlining a point made by cyber experts at CrowdStrike, the firm the party has hired to investigate the breaches at the DNC and the DCCC. The conference call was prompted by the late Friday release of DCCC spreadsheets containing nearly all House Democrats’ and staffers’ personal emails and phone numbers, which led to a flood of harassing emails and phone calls over the weekend.
In total, the hackers have reportedly infiltrated more than 100 party officials and groups, leaving progressives fearful that the entire Democratic Party apparatus is potentially compromised. During Saturday’s call, House members in competitive races voiced concerns about what damning information might be out there.
But hacking specialists say the most harmful information might not even be genuine.
“You may have material that’s 95 percent authentic, but 5 percent is modified, and you’ll never actually be able to prove a negative, that you never wrote what’s in that material,” CrowdStrike co-founder Dmitri Alperovitch told POLITICO. “Even if you released the original email, how will you prove that it’s not doctored? It’s sort of damned if you do, damned if you don’t.”
Several Democratic operatives said they even expect fake information, though mixed with enough truth to cause damage.
“The most powerful lie contains truth,” said Craig Varoga, a D.C.-based Democratic strategist. “Whether it’s the devil or it’s Russian intelligence services, they traffic in things that are true in order to put across a greater lie.”
Historically, it’s not unprecedented for intelligence agencies — including those in the U.S. — to release fake reports for propaganda purposes. The FBI’s COINTELPRO program infamously used forged documents and false news reports to discredit or harass dissenters during the 1950s and 1960s, including civil rights leaders, anti-war protesters and alleged communist organizations.
Hackers have adopted similar strategies.
In 2013, Syrian hackers backing embattled President Bashar Assad hijacked The Associated Press’ Twitter account, tweeting out falsified reports of two explosions at the White House that had injured Obama. The Dow plummeted in minutes, wiping out $136 billion in market value, according to Bloomberg. It stabilized shortly thereafter, once the report was revealed to be a hoax.
Russia has long been known for engaging in such propaganda warfare, going back to the days of the Soviet Union, when the KGB spread conspiracy theories about the FBI and CIA’s involvement in President John F. Kennedy’s assassination. In the 1980s, the KGB planted newspaper articles alleging that the U.S. had invented HIV during a biological weapons research project.
The security agency also secretly helped an East German journalist write a book, “Who’s Who in the CIA,” that accurately outed numerous undercover CIA agents but also intentionally included a raft of people who were simply American officials stationed overseas, according to a former top Soviet security official.
In the weeks since the DNC email leaks, cyber specialists on Twitter have been circulating a passage from the memoirs of a former East German spymaster who wrote about the “creative” use of forgeries in conjunction with genuine leaks.
“Embarrassed by the publication of genuine but suppressed information, the targets were badly placed to defend themselves against the other, more damaging accusations that had been invented,” wrote Markus Wolf, who had headed East Germany’s foreign intelligence division for more than three decades. (On the other hand, he added that, “my principle was to stick as close to the truth as possible, especially when there was so much of it that could easily further the department’s aims.”)
In recent years, the Kremlin has adapted these tactics for a digital age.
The Kremlin was caught in 2014 manipulating satellite images to produce “proof” that Ukraine had shot down the Malaysia Airlines flight that was downed over Ukraine, killing 298 passengers. Last year, a Russian lawmaker’s staffer was exposed filming a fake war report, pretending to be near the front line in eastern Ukraine, where Moscow has seized territory.
“Standard Russian modus operandi,” said James Lewis, an international cyber policy expert at the Center for Strategic and International Studies, via email. “They’ve done it before in the Baltics and other parts of Europe: Leak a lot of real data and slip in some fakes (or more often, things that have been subtly modified rather than a complete fake).”
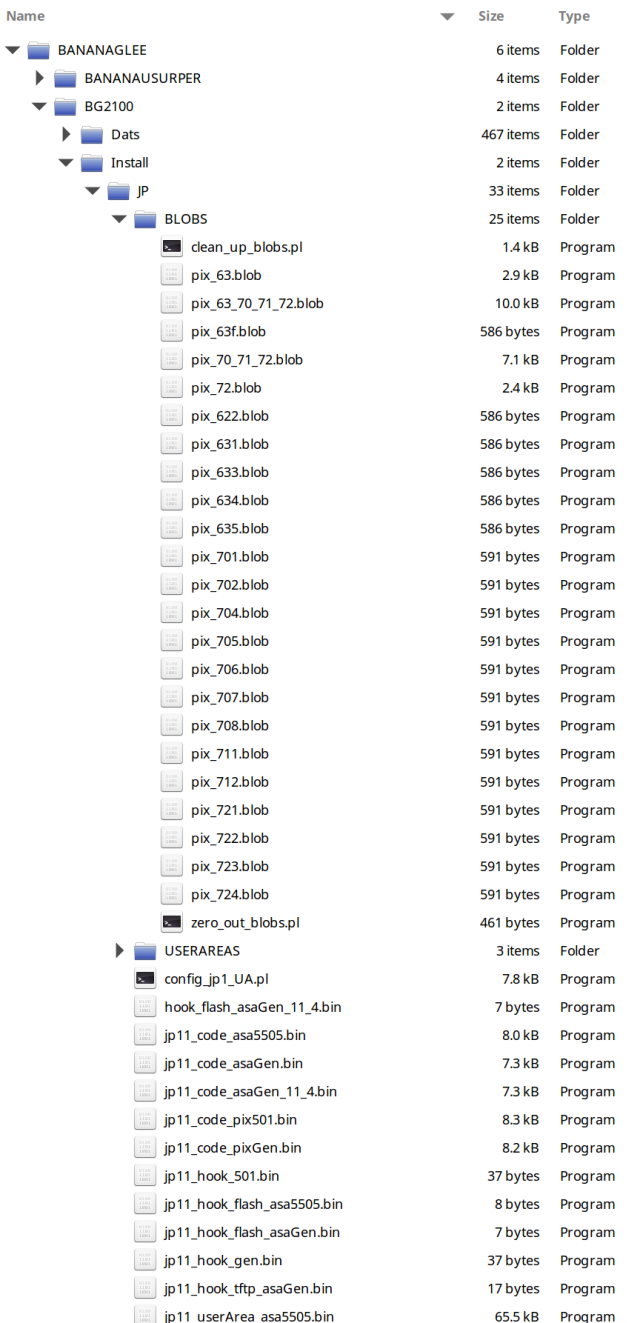
Digital forensics experts even noted that the metadata on some of the early documents leaked from the DNC — which included opposition research files — had been altered, although it didn’t appear that any content was compromised. But the discovery showed how easy such an edit would be.
“They have information warfare as a core tenet of what they do form a geopolitical perspective,” said Steve Ward, director of communications for digital security firm FireEye, which tracks many Russian hacking groups. “It’s really in their wheelhouse.”
But Ward and other digital security experts acknowledge that the exact scenario Pelosi was discussing would be novel, and that so far, hackers have had little incentive to manipulate leaked data. As anonymous digital actors, hackers already have the deck stacked against them when trying to expose information.
“You’ve got to suspend disbelief and trust the bad guys when you’re looking at this stuff,” Ward said. If they make just one discredited leak, hackers are “effectively losing the value of the operation by creating distrust with the data,” he added.
This leads many cyber experts to suspect that any release of faked emails, if it comes at all, would probably not come until days before the Nov. 8 election. At that point, the Democrats wouldn’t have time to definitively prove a forgery.
So it makes sense, strategists said, for Democrats to put the concept in the public’s mind now.
“What Pelosi is doing is making the response now,” said Brad Bannon, a longtime Democratic consultant. “Democrats do have their antenna up over this thing. They are anticipating.”
Eric Geller, Martin Matishak and Heather Caygle contributed to this report.