Hillary Clinton is no novice to security measures when it comes to global adversarial incursions. Her team of political operatives are not neophytes either.
By virtue of Hillary’s emails, inspector general’s reports and non-approved (unknown servers) and violations of data protection, Hillary’s team are guilty of malfeasance of duty and management. For proof, read the FBI search warrant of the Abedin/Weiner computers and hard-drive.
Have you considered why certain buildings in government have harden structures including sound proof windows, SCIFs, entry and exit procedures, security clearances and action protocol when transmitting information in hardcopy and electronically? This is due to thousands of foreign tasking of espionage of history that include Russia, China and North Korea to mention a few. Not all hacking is equal, there are viruses, malware, electronic theft and propaganda.
A distinction should also be made between hacking and SIGINT, signals intelligence. SIGINT is the interception of data used by foreign powers which can and does include scooping and snooping. There are electronic signals, radars and weapons systems that are all part of the target base applied by foreign adversaries and allies. No part of the United States government or civilian enterprise is exempt or omitted by outside powers including outright spying and theft of industrial espionage, patent information and intelligence.
Beyond this, there is the whole model of propaganda, real and fake news. Under Barack Obama, the United States has been in a reactionary mode rather than installing and actively pursuing defensive and countermeasures when it comes to biased, misleading, filtered or altered influence causing ill legitimate attitudes, movements, synthesis and policy decisions. The master of this game is Russia.
The U.S. government spent more than a decade preparing responses to malicious hacking by a foreign power but had no clear strategy when Russia launched a disinformation campaign over the internet during the U.S. election campaign, current and former White House cyber security advisers said.
Far more effort has gone into plotting offensive hacking and preparing defenses against the less probable but more dramatic damage from electronic assaults on the power grid, financial system or direct manipulation of voting machines.
Over the last several years, U.S. intelligence agencies tracked Russia’s use of coordinated hacking and disinformation in Ukraine and elsewhere, the advisers and intelligence experts said, but there was little sustained, high-level government conversation about the risk of the propaganda coming to the United States.
A former White House official cautioned that any U.S. government attempt to counter the flow of foreign state-backed disinformation through deterrence would face major political, legal and moral obstacles.
“You would have to have massive surveillance and curtailed freedom and that is a cost we have not been willing to accept,” said the former official, who spoke on condition of anonymity. “They (Russia) can control distribution of information in ways we don’t.”
Clinton Watts, a security consultant, former FBI agent and a fellow at the nonprofit Foreign Policy Research Institute, said the U.S. government no longer has an organization, such as the U.S. Information Agency, that provided counter-narratives during the Cold War.
He said that most major Russian disinformation campaigns in the United States and Europe have started at Russian-government funded media outlets, such as RT television or Sputnik News, before being amplified on Twitter by others.
A defense spending pill passed this month calls for the State Department to establish a “Global Engagement Center” to take on some of that work, but similar efforts to counter less sophisticated Islamic State narratives have fallen short.
The U.S. government formally accused Russia of a campaign of cyber attacks against U.S. political organizations in October, a month before the Nov. 8 election.
U.S. ‘STUCK’
James Lewis, a cyber security expert at the Center for Strategic & International Studies who has worked for the departments of State and Commerce and the U.S. military, said Washington needed to move beyond antiquated notions of projecting influence if it hoped to catch up with Russia.
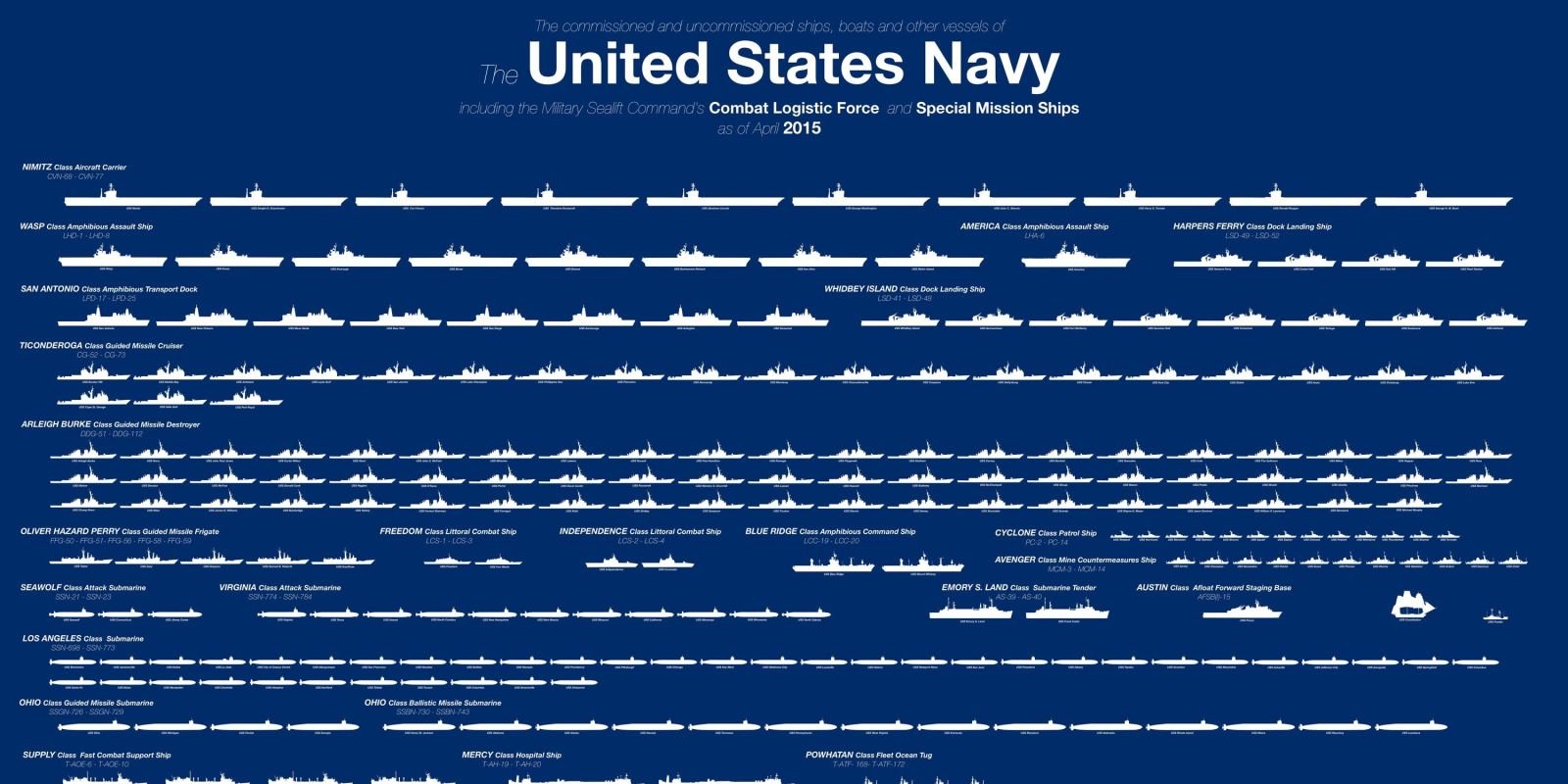
“They have RT and all we know how to do is send a carrier battle group,” Lewis said. “We’re going to be stuck until we find a way deal with that.” More here including Alex Jones from Reuters.
Then there is Iran who has and continues to use propaganda to build internal reputation and power, the same as Putin of Russia himself.
When Iran detained our Navy personnel, consider the traction that was gained both positive and negative.
NR: The sight of members of the American military, disarmed and under Iranian control, is of enormous propaganda value in Iran’s ongoing war against the United States. To its allies in the Middle East, the photo demonstrates Iran’s strength – how many jihadist countries have had this many American servicemembers under their power? – and it demonstrates American weakness. Then there’s this: “This time, the Americans were cooperative in proving their innocence, and they quickly accepted their faults without resistance,” the analyst, Hamidreza Taraghi, said in a phone interview. “The Marines apologized for having strayed into Iranian waters.” Never fear, John Kerry made friends with the Iranians, and that made all the difference: Also playing a role was the strong relationship that has developed between Mr. Kerry and the Iranian foreign minister, Mohammad Javad Zarif, during negotiations on the nuclear deal, Mr. Taraghi said. “John Kerry and Zarif were on the phone during the past hours, and this helped the problem to be resolved quickly due to their direct contact,” he said. Nations that take illegal propaganda photos, crow about their seizure of American boats, confiscate part of their equipment, and then point to our allegedly admitted faults aren’t “easing tensions,” they’re flexing their muscles. I’m glad our sailors and boats are back in American hands — minus, apparently, their GPS equipment — but once again Iran has thumbed its nose at the U.S., demonstrating that it does what it wants — whether it’s testing missiles, launching rockets near U.S. warships, or taking, questioning, and photographing American sailors who (allegedly) stray into Iranian waters.