The excuses both sides explain scheduling conflicts. C’mon, lil Kim is not exactly that busy to take a meeting with America, right? As North and South Korea have begin to dismantle 20 guard posts along the DMZ. South Korea has 60 such positions while North Korea has an estimated 160. Allegedly, all firearms have been already removed from the guard posts. Personnel is still there but it is said they are unarmed.
Back to that cancelled meeting….
 A satellite image of a secret North Korean ballistic missile base. The North has offered to dismantle a different major missile launching site while continuing to make improvements at more than a dozen others.CreditCreditCSIS/Beyond Parallel, via DigitalGlobe 2018
A satellite image of a secret North Korean ballistic missile base. The North has offered to dismantle a different major missile launching site while continuing to make improvements at more than a dozen others.CreditCreditCSIS/Beyond Parallel, via DigitalGlobe 2018
More detail is explained here.
What is the reason then? Missile sites….hummm
North Korea are still operating undeclared missile bases and even improving some of their missile sites instead of shutting them down.
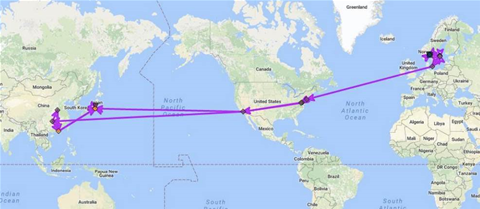
The latest report from the Center for Strategic and International Studies in Washington said it had identified 13 of an estimated 20 secret missile operating bases inside North Korea.
They could be used to house ballistic missiles of various ranges, with the largest believed to be capable of striking anywhere in the United States.
The report, written by researcher Joseph Bermudez, said maintenance and minor infrastructure improvements have been observed at some of the sites.
The sites identified in the report are scattered in remote, mountainous areas across North Korea.
It even identified improvements being made to its Sakkanmol site, close to the border with South Korea.
President Trump is still hoping to persuade Pyongyang to give up its nuclear weapons and long-range missiles.
The North Korean leader Kim Jong Un and U.S. President Donald Trump pledged to work towards ‘denuclearization’ at their landmark June summit in Singapore.
Shortly after the summit, Trump tweeted that there was no longer a nuclear threat from North Korea.
North Korea declared its nuclear force ‘complete’ and halted missile and nuclear bomb testing earlier this year.
North Korea has said it has closed its Punggye-ri nuclear testing site and the Sohae missile engine test facility.
It also raised the possibility of shuttering more sites and allowing international inspections if Washington took ‘corresponding measures’.
Last week, North Korea called off a meeting with U.S. Secretary of State Mike Pompeo in New York.
The country’s state media said on Monday the resumption of some small-scale military drills by South Korea and the United States violated a recent agreement aimed at lowering tensions on the Korean peninsula.
‘Missile operating bases are not launch facilities,’ Bermudez wrote.
‘While missiles could be launched from within them in an emergency, Korean People’s Army (KPA) operational procedures call for missile launchers to disperse from the bases to pre-surveyed or semi-prepared launch sites for operations.’
None of the missile bases have been acknowledged by North Korea, and analysts say an accurate disclosure of nuclear weapons and missile capabilities would be an important part of any denuclearization deal.



 In part from
In part from