|
Per the FBI website: Good afternoon Chairman Johnson, Ranking Member Carper, and members of the committee. Thank you for the opportunity to appear before you today to discuss the current threats to the homeland and our efforts to address new challenges, including terrorists’ use of technology to communicate—both to inspire and recruit. The widespread use of technology propagates the persistent terrorist message to attack U.S. interests whether in the homeland or abroad. As the threat to harm Western interests evolves, we must adapt and confront the challenges, relying heavily on the strength of our federal, state, local, and international partnerships. Our successes depend on interagency cooperation. We work closely with our partners within the Department of Homeland Security and the National Counterterrorism Center to address current and emerging threats. Counterterrorism Counterterrorism remains the FBI’s top priority, however, the threat has changed in two significant ways. First, the core al Qaeda tumor has been reduced, but the cancer has metastasized. The progeny of al Qaeda—including AQAP, al Qaeda in the Islamic Maghreb, and the Islamic State of Iraq and the Levant (ISIL)—have become our focus. Secondly, we are confronting the explosion of terrorist propaganda and training on the Internet. It is no longer necessary to get a terrorist operative into the United States to recruit. Terrorists, in ungoverned spaces, disseminate poisonous propaganda and training materials to attract troubled souls around the world to their cause. They encourage these individuals to travel, but if they can’t travel, they motivate them to act at home. This is a significant change from a decade ago. We continue to identify individuals who seek to join the ranks of foreign fighters traveling in support of ISIL, and also homegrown violent extremists who may aspire to attack the United States from within. These threats remain among the highest priorities for the FBI and the Intelligence Community as a whole. Conflicts in Syria and Iraq continue to serve as the most attractive overseas theaters for Western-based extremists who want to engage in violence. We estimate approximately 250 Americans have traveled or attempted to travel to Syria to participate in the conflict. While this number is lower in comparison to many of our international partners, we closely analyze and assess the influence groups like ISIL have on individuals located in the United States who are inspired to commit acts of violence. Whether or not the individuals are affiliated with a foreign terrorist organization and are willing to travel abroad to fight or are inspired by the call to arms to act in their communities, they potentially pose a significant threat to the safety of the United States and U.S. persons. ISIL has proven relentless in its violent campaign to rule and has aggressively promoted its hateful message, attracting like-minded extremists to include Westerners. To an even greater degree than al Qaeda or other foreign terrorist organizations, ISIL has persistently used the Internet to communicate. From a homeland perspective, it is ISIL’s widespread reach through the Internet and social media which is most concerning as ISIL has aggressively employed this technology for its nefarious strategy. ISIL blends traditional media platforms, glossy photos, in-depth articles, and social media campaigns that can go viral in a matter of seconds. No matter the format, the message of radicalization spreads faster than we imagined just a few years ago. Unlike other groups, ISIL has constructed a narrative that touches on all facets of life—from career opportunities to family life to a sense of community. The message isn’t tailored solely to those who are overtly expressing symptoms of radicalization. It is seen by many who click through the Internet every day, receive social media push notifications, and participate in social networks. Ultimately, many of these individuals are seeking a sense of belonging. As a communication medium, social media is a critical tool for terror groups to exploit. One recent example occurred when an individual was arrested for providing material support to ISIL by facilitating an associate’s travel to Syria to join ISIL. The arrested individual had multiple connections, via a social media networking site, with other like-minded individuals. There is no set profile for the susceptible consumer of this propaganda. However, one trend continues to rise—the inspired youth. We’ve seen certain children and young adults drawing deeper into the ISIL narrative. These individuals are often comfortable with virtual communication platforms, specifically social media networks. ISIL continues to disseminate their terrorist message to all social media users—regardless of age. Following other groups, ISIL has advocated for lone offender attacks. In recent months ISIL released a video, via social media, reiterating the group’s encouragement of lone offender attacks in Western countries, specifically advocating for attacks against soldiers and law enforcement, intelligence community members, and government personnel. Several incidents have occurred in the United States and Europe over the last few months that indicate this “call to arms” has resonated among ISIL supporters and sympathizers. In one case, a New York-based male was arrested in September after he systematically attempted to travel to the Middle East to join ISIL. The individual, who was inspired by ISIL propaganda, expressed his support for ISIL online and took steps to carry out acts encouraged in the ISIL call to arms. The targeting of U.S. military personnel is also evident with the release of names of individuals serving in the U.S. military by ISIL supporters. The names continue to be posted to the Internet and quickly spread through social media, depicting ISIL’s capability to produce viral messaging. Threats to U.S. military and coalition forces continue today. Social media has allowed groups, such as ISIL, to use the Internet to spot and assess potential recruits. With the widespread horizontal distribution of social media, terrorists can identify vulnerable individuals of all ages in the United States—spot, assess, recruit, and radicalize—either to travel or to conduct a homeland attack. The foreign terrorist now has direct access into the United States like never before. In other examples of arrests, a group of individuals was contacted by a known ISIL supporter who had already successfully traveled to Syria and encouraged them to do the same. Some of these conversations occur in publicly accessed social networking sites, but others take place via private messaging platforms. As a result, it is imperative the FBI and all law enforcement organizations understand the latest communication tools and are positioned to identify and prevent terror attacks in the homeland. We live in a technologically driven society and just as private industry has adapted to modern forms of communication so too have terrorists. Unfortunately, changing forms of Internet communication and the use of encryption are posing real challenges to the FBI’s ability to fulfill its public safety and national security missions. This real and growing gap, to which the FBI refers as “Going Dark,” is an area of continuing focus for the FBI; we believe it must be addressed given the resulting risks are grave both in both traditional criminal matters as well as in national security matters. The United States government is actively engaged with private companies to ensure they understand the public safety and national security risks that result from malicious actors’ use of their encrypted products and services. However, the administration is not seeking legislation at this time. The FBI is utilizing all lawful investigative techniques and methods to combat the threat these individuals may pose to the United States. In conjunction with our domestic and foreign partners, we are rigorously collecting and analyzing intelligence information as it pertains to the ongoing threat posed by foreign terrorist organizations and homegrown violent extremists. We continue to encourage robust information sharing; in partnership with our many federal, state, and local agencies assigned to Joint Terrorism Task Forces around the country, we remain vigilant to ensure the safety of the American public. Be assured, the FBI continues to pursue increased efficiencies and information sharing processes as well as pursue technological and other methods to help stay ahead of threats to the homeland. Intelligence Integrating intelligence and operations is part of the broader intelligence transformation the FBI has undertaken in the last decade. We are making progress, but have more work to do. We have taken two steps to improve this integration. First, we have established an Intelligence Branch within the FBI headed by an executive assistant director (EAD). The EAD looks across the entire enterprise and drives integration. Second, we now have special agents and new intelligence analysts at the FBI Academy engaged in practical training exercises and taking core courses together. As a result, they are better prepared to work well together in the field. Our goal every day is to get better at using, collecting and sharing intelligence to better understand and defeat our adversaries. The FBI cannot be content to just work what is directly in front of us. We must also be able to understand the threats we face at home and abroad and how those threats may be connected. Towards that end, intelligence is gathered, consistent with our authorities, to help us understand and prioritize identified threats and to determine where there are gaps in what we know about these threats. We then seek to fill those gaps and learn as much as we can about the threats we are addressing and others on the threat landscape. We do this for national security and criminal threats, on both a national and local field office level. We then compare the national and local perspectives to organize threats into priority for each of the FBI’s 56 field offices. By categorizing threats in this way, we strive to place the greatest focus on the gravest threats we face. This gives us a better assessment of what the dangers are, what’s being done about them, and where we should prioritize our resources. Cyber An element of virtually every national security threat and crime problem the FBI faces is cyber-based or facilitated. We face sophisticated cyber threats from state-sponsored hackers, hackers for hire, organized cyber syndicates, and terrorists. On a daily basis, cyber-based actors seek our state secrets, our trade secrets, our technology, and our ideas—things of incredible value to all of us and of great importance to the conduct of our government business and our national security. They seek to strike our critical infrastructure and to harm our economy. We continue to see an increase in the scale and scope of reporting on malicious cyber activity that can be measured by the amount of corporate data stolen or deleted, personally identifiable information compromised, or remediation costs incurred by U.S. victims. For example, as the committee is aware, the Office of Personnel Management (OPM) discovered earlier this year that a number of its systems were compromised. These systems included those that contain information related to the background investigations of current, former, and prospective Federal government employees, as well as other individuals for whom a federal background investigation was conducted. The FBI is working with our interagency partners to investigate this matter. FBI agents, analysts, and computer scientists are using technical capabilities and traditional investigative techniques—such as sources, court-authorized electronic surveillance, physical surveillance, and forensics—to fight cyber threats. We are working side-by-side with our federal, state, and local partners on Cyber Task Forces in each of our 56 field offices and through the National Cyber Investigative Joint Task Force (NCIJTF), which serves as a coordination, integration, and information sharing center for 19 U.S. agencies and several key international allies for cyber threat investigations. Through CyWatch, our 24-hour cyber command center, we combine the resources of the FBI and NCIJTF, allowing us to provide connectivity to federal cyber centers, government agencies, FBI field offices and legal attachés, and the private sector in the event of a cyber intrusion. We take all potential threats to public and private sector systems seriously and will continue to investigate and hold accountable those who pose a threat in cyberspace. * * * Finally, the strength of any organization is its people. The threats we face as a nation have never been greater or more diverse and the expectations placed on the Bureau have never been higher. Our fellow citizens look to us to protect the United States from all of those threats and the men and women of the Bureau continue to meet—and exceed—those expectations, every day. I want to thank them for their dedication and their service. Chairman Johnson, Ranking Member Carper, and committee members, I thank you for the opportunity to testify concerning the threats to the homeland and terrorists’ use of the Internet and social media as a platform for spreading ISIL propaganda and inspiring individuals to target the homeland, and the impact of the Going Dark problem on mitigating their efforts. I am happy to answer any questions you might have.
|
|
Category Archives: Terror
LinkedIn Infiltrated by Iranian Hackers
Going back to 2012, Congress held hearings on how the United States is losing the cyber espionage war. To date, there has been no ground gained outside of the scope of creating more task forces and adding cyber personnel. To stop the intrusions by China, Russia and Iran has been a failure.
For a report on the major hacks in 2014, go here. This is by no means a complete list of corporations but it does give a view into the depth of the cyber threat.
WASHINGTON: The United States is “losing the cyber espionage war” against China, Russia and other countries, but even in the face of such a grave threat the country cannot agree on how to protect its precious intellectual seed capital from these predations, the chairman of the House Intelligence Committee says.
“We are running out of time on this,” Rep. Mike Rogers, respected for working closely with his ranking member, said in a speech at today’s Intelligence and National Security Alliance‘s (INSA) cyber conference here.
China is stealing intellectual property on a massive scale, as Gen. Keith Alexander, head of both the National Security Agency and Cyber Command, has made clear with his estimates of such thefts topping $1 trillion. While China is not alone, U.S government officials have made clear that no country engages in cyber espionage as systematically, as thoroughly or as broadly as does the People’s Republic of China.
“China is investing hugely in this technology,” Rogers notes. And the impact of that investment is felt not only in the economic sphere, important as that is. Cyber is now an integral of military planning and operations, as the Russians have demonstrated several times.
To help stem those thefts and to protect critical infrastructure such as power grids, Rogers and Rep. Dutch Ruppersberger, his Democratic colleague on the HPSCI, met with hundreds of business leaders, civil rights and privacy groups over several months as they began to craft what became their 13-page bill. It would have offered businesses liabliity insurance in return for their agreeing to share threat information with the government. The government also would have shared threat information with the businesses.
But there was a catch. Because of how sensitive sources and methods are in the cyber world, the businesses would have to get top secret clearance for senior officials, build and maintain a Sensitive Compartmented Information Facility (SCIF), and maintain the physical and bureaucratic complex required of anyone dealing with classified information.
As Rogers put it, his committee had offered industry a “carrot and a stick.” But his colleagues in the Senate wanted to chart a different path, so the Rogers-Ruppersberger bill is on life support. I asked him today what he planned to do with his “dead” bill. “All is not lost. I am reaching out to members of the Senate just to see what our options are,” as is Ruppersberger. “We are not giving up.”
LinkedIn profiles said to be part of Iranian cyber-espionage campaign
WashingtonTimes: Iranian hackers are suspected of operating a network of bogus LinkedIn accounts that security researchers believe is part of a campaign targeting employees of corporations in the Middle East.
By creating phony profiles containing fabricated job histories and endorsements from other concocted accounts, researchers at Dell said this week that a group of hackers, likely acting on behalf of Iran, attempted to collect intelligence from legitimate LinkedIn users employed in the Arabian and African telecommunications and defense industries. Twenty-five fake LinkedIn accounts have been identified by researchers working for the company’s SecureWorks Counter Threat Unit, including those of supposed recruitment consultants with hundreds of connections apiece, Dell said on Wednesday.
“CTU researchers assess with high confidence the purpose of this network is to target potential victims through social engineering,” Dell said in the latest report, referring to a tactic in which sensitive data becomes compromised when an individual reveals information to an attacker, often under false pretenses.
Dell has named the actors “Threat Group-2889” and said it’s likely the same organization dubbed “Operation Cleaver” in a report released last year by Cylance, a security firm that linked the group to Iran and claimed it was working to undermine the security of over 50 companies across 15 industries in the region, possibly as retaliation for the U.S.-led Stuxnet campaign.
“Creating a network of seemingly genuine and established LinkedIn personas helps TG-2889 identify and research potential victims. The threat actors can establish a relationship with targets by contacting them directly, or by contacting one of the target’s connections. It may be easier to establish a direct relationship if one of the fake personas is already in the target’s LinkedIn network,” Dell said.
“The level of detail in the profiles suggests that the threat actors invested substantial time and effort into creating and maintaining these personas.”
According to the findings published by Cylance in December, the “Operation Cleaver” hackers used social engineering to trick targets into installing malware that would allow data to then be stolen from infected computers.
Cylance’s report had linked the group to attacks across the world, but Dell’s CTU team said the LinkedIn campaign seems to largely target account holders in the Middle East and northern Africa, a quarter of which work in telecommunications.
“Updates to profile content such as employment history suggest that TG-2889 regularly maintains these fake profiles. The persona changes and job alterations could suggest preparations for a new campaign, and the decision to reference Northrup Grumman and Airbus Group may indicate that the threat actors plan to target the aerospace vertical,” Dell said.
Last month, Director of National Intelligence James Clapper told a congressional committee that Iran uses its cyber program to carry out “asymmetric but proportional retaliation against political foes, as well as a sophisticated means of collecting intelligence.” He went on to blame Iranian hackers for cyberattacks against American banks in 2012 and 2013, as well as an assault last year on the Las Vegas Sands casino company.
Iran deal violates federal law
What does it look like when the president of the United States is a desperate man for a deal? Does he have a platoon of legal eagles searching law and then writing executive orders to finesse the law? The order from the White House is ‘FIND A LOOPHOLE’.
EXCLUSIVE: U.S. officials conclude Iran deal violates federal law
FNC:James Rosen > Some senior U.S. officials involved in the implementation of the Iran nuclear deal have privately concluded that a key sanctions relief provision – a concession to Iran that will open the doors to tens of billions of dollars in U.S.-backed commerce with the Islamic regime – conflicts with existing federal statutes and cannot be implemented without violating those laws, Fox News has learned.
At issue is a passage tucked away in ancillary paperwork attached to the Joint Comprehensive Plan of Action, or JCPOA, as the Iran nuclear deal is formally known. Specifically, Section 5.1.2 of Annex II provides that in exchange for Iranian compliance with the terms of the deal, the U.S. “shall…license non-U.S. entities that are owned or controlled by a U.S. person to engage in activities with Iran that are consistent with this JCPOA.”
In short, this means that foreign subsidiaries of U.S. parent companies will, under certain conditions, be allowed to do business with Iran. The problem is that the Iran Threat Reduction and Syria Human Rights Act (ITRA), signed into law by President Obama in August 2012, was explicit in closing the so-called “foreign sub” loophole.
Indeed, ITRA also stipulated, in Section 218, that when it comes to doing business with Iran, foreign subsidiaries of U.S. parent firms shall in all cases be treated exactly the same as U.S. firms: namely, what is prohibited for U.S. parent firms has to be prohibited for foreign subsidiaries, and what is allowed for foreign subsidiaries has to be allowed for U.S. parent firms.
What’s more, ITRA contains language, in Section 605, requiring that the terms spelled out in Section 218 shall remain in effect until the president of the United States certifies two things to Congress: first, that Iran has been removed from the State Department’s list of nations that sponsor terrorism, and second, that Iran has ceased the pursuit, acquisition, and development of weapons of mass destruction.
Additional executive orders and statutes signed by President Obama, such as the Iran Nuclear Agreement Review Act, have reaffirmed that all prior federal statutes relating to sanctions on Iran shall remain in full effect.
For example, the review act – sponsored by Sens. Bob Corker (R-Tennessee) and Ben Cardin (D-Maryland), the chairman and ranking member, respectively, of the Foreign Relations Committee, and signed into law by President Obama in May – stated that “any measure of statutory sanctions relief” afforded to Iran under the terms of the nuclear deal may only be “taken consistent with existing statutory requirements for such action.” The continued presence of Iran on the State Department’s terror list means that “existing statutory requirements” that were set forth in ITRA, in 2012, have not been met for Iran to receive the sanctions relief spelled out in the JCPOA.
As the Iran deal is an “executive agreement” and not a treaty – and has moreover received no vote of ratification from the Congress, explicit or symbolic – legal analysts inside and outside of the Obama administration have concluded that the JCPOA is vulnerable to challenge in the courts, where federal case law had held that U.S. statutes trump executive agreements in force of law.
Administration sources told Fox News it is the intention of Secretary of State John Kerry, who negotiated the nuclear deal with Iran’s foreign minister and five other world powers, that the re-opening of the “foreign sub” loophole by the JCPOA is to be construed as broadly as possible by lawyers for the State Department, the Treasury Department and other agencies involved in the deal’s implementation.
But the apparent conflict between the re-opening of the loophole and existing U.S. law leaves the Obama administration with only two options going forward. The first option is to violate ITRA, and allow foreign subsidiaries to be treated differently than U.S. parent firms. The second option is to treat both categories the same, as ITRA mandated – but still violate the section of ITRA that required Iran’s removal from the State Department terror list as a pre-condition of any such licensing.
It would also renege on the many promises of senior U.S. officials to keep the broad array of American sanctions on Iran in place. Chris Backemeyer, who served as Iran director for the National Security Council from 2012 to 2014 and is now the State Department’s deputy coordinator for sanctions policy, told POLITICO last month “there will be no real sanctions relief of our primary embargo….We are still going to have sanctions on Iran that prevent most Americans from…engaging in most commercial activities.”
Likewise, in a speech at the Washington Institute for Near East Policy last month, Adam Szubin, the acting under secretary of Treasury for terrorism and financial crimes, described Iran as “the world’s foremost sponsor of terrorism” and said existing U.S. sanctions on the regime “will continue to be enforced….U.S. investment in Iran will be prohibited across the board.”
Nominated to succeed his predecessor at Treasury, Szubin appeared before the Senate Banking Committee for a confirmation hearing the day after his speech to the Washington Institute. At the hearing, Sen. Tom Cotton (R-Arkansas) asked the nominee where the Obama administration finds the “legal underpinnings” for using the JCPOA to re-open the “foreign sub” loophole.
Szubin said the foreign subsidiaries licensed to do business with Iran will have to meet “some very difficult conditions,” and he specifically cited ITRA, saying the 2012 law “contains the licensing authority that Treasury would anticipate using…to allow for certain categories of activity for those foreign subsidiaries.”
Elsewhere, in documents obtained by Fox News, Szubin has maintained that a different passage of ITRA, Section 601, contains explicit reference to an earlier law – the International Emergency Economic Powers Act, or IEEPA, on the books since 1977 – and states that the president “may exercise all authorities” embedded in IEEPA, which includes licensing authority for the president.
However, Section 601 is also explicit on the point that the president must use his authorities from IEEPA to “carry out” the terms and provisions of ITRA itself, including Section 218 – which mandated that, before this form of sanctions relief can be granted, Iran must be removed from the State Department’s terror list. Nothing in the Congressional Record indicates that, during debate and passage of ITRA, members of Congress intended for the chief executive to use Section 601 to overturn, rather than “carry out,” the key provisions of his own law.
One administration lawyer contacted by Fox News said the re-opening of the loophole reflects circular logic with no valid legal foundation. “It would be Alice-in-Wonderland bootstrapping to say that [Section] 601 gives the president the authority to restore the foreign subsidiary loophole – the exact opposite of what the statute ordered,” said the attorney, who requested anonymity to discuss sensitive internal deliberations over implementation of the Iran deal.
At the State Department on Thursday, spokesman John Kirby told reporters Secretary Kerry is “confident” that the administration “has the authority to follow through on” the commitment to re-open the foreign subsidiary loophole.
“Under the International Emergency Economic Powers Act, the president has broad authorities, which have been delegated to the secretary of the Treasury, to license activities under our various sanctions regimes, and the Iran sanctions program is no different,” Kirby said.
Sen. Ted Cruz (R-Texas), the G.O.P. presidential candidate who is a Harvard-trained lawyer and ardent critic of the Iran deal, said the re-opening of the loophole fits a pattern of the Obama administration enforcing federal laws selectively.
“It’s a problem that the president doesn’t have the ability wave a magic wand and make go away,” Cruz told Fox News in an interview. “Any U.S. company that follows through on this, that allows their foreign-owned subsidiaries to do business with Iran, will very likely face substantial civil liability, litigation and potentially even criminal prosecution. The obligation to follow federal law doesn’t go away simply because we have a lawless president who refuses to acknowledge or follow federal law.”
A spokesman for the Senate Banking Committee could not offer any time frame as to when the committee will vote on Szubin’s nomination.
For more details and reading:
Sanctions on Foreign Subsidiaries Implemented Under Iran Threat Reduction Act
In the months since the signing of the Iran Threat Reduction and Syria Human Rights Act (which we will stubbornly continue to refer to here as “ITRA”), the Obama administration has worked to implement tougher sanctions against Iran. Although many of the ITRA regulations are not expected until early November, an Executive Order issued last week marked the beginning of a much stricter era of sanctions pursuant to ITRA, the Iran Sanctions Act of 1996 (ISA), and the Comprehensive Iran Sanctions, Accountability, and Divestment Act of 2010 (CISADA). On October 9, 2012, sixty days after President Obama signed ITRA into law, he issued Executive Order No. 13,628, extending U.S. Iran sanctions to cover foreign subsidiaries of U.S. parent companies, a prohibition that did not exist until promulgated in ITRA.[1] The Executive Order implements ITRA Section 218,[2] which we highlighted in our August 17, 2012 post, by providing that:
No entity owned or controlled by a United States person and established or maintained outside the United States may knowingly engage in any transaction, directly or indirectly, with the Government of Iran or any person subject to the jurisdiction of the Government of Iran, if that transaction would be prohibited by [the pre-existing Iran sanctions].
The Executive Order defines the term “entity” to mean “a partnership, association, trust, joint venture, corporation, group, subgroup, or other organization.” This is a slight expansion of the definition provided by Congress in Section 218, which does not include the words “group” or “subgroup.” The resulting definition appears to authorize sanctions where any group “controlled by” a U.S. person, regardless of whether the group is formally incorporated, conducts prohibited Iran-related business.
The Executive Order gives no quarter for existing contracts, and authorizes standard Office of Foreign Assets Control (OFAC) penalties against the U.S. person controlling the foreign entity. However, Subsection 4(c) of the Order provides that civil penalties shall not apply if the U.S. person divests or terminates its business with the foreign subsidiary not later than February 6, 2013.
The Order also directs that Secretaries of Treasury and State to issue regulations to implement several other provisions of ITRA (though the ITRA itself also directed the issuance of such regulations within 90 days of the effective date of the statute). Thus, Treasury regulations may be expected by around November 8, 2012 regarding several ITRA provisions, including the following:
- Section 202, which requires the imposition of at least five ISA sanctions on any person who, on or after November 8, 2012, beneficially owns, operates, or controls a vessel that is used to transport crude oil from Iran to another country. This provision applies, however, only if the President determines under the National Defense Authorization Act that there is a sufficient supply of petroleum from countries other than Iran to permit petroleum purchasers to significantly reduce purchases from Iran;
- Section 214, which increases the availability of sanctions on subsidiaries and agents of UN-sanctioned persons;
- Section 215, which extends the availability of sanctions against persons connected to Iran’s weapons of mass destruction to any foreign financial institution who aids that person; and
- Section 216 adds a new section to CISADA, expanding sanctions to apply to financial institutions connected to certain proliferation or terrorism activities of Iran or its National Guard.
In addition to the forthcoming regulations, the President is required to provide a great deal of information to Congress on and after November 8. Under section 211, the President must report to Congress on the identity of operators of vessels and persons that conduct or facilitate significant financial transactions that manage Iranian ports designated for sanctions under the International Emergency Economic Powers Act. Furthermore, the President must provide the identity of and the restrictions on individuals, including senior Iranian officials, Iranian Revolutionary Guard Corps Officials, foreign persons supporting the Iranian Revolutionary Guard, and foreign government agencies carrying out transactions with certain Iran-affiliated persons.[3]
The Secretaries of Treasury and State also are required to report to the relevant Congressional committees on certain aspects of the implementation of ITRA. Under Section 206, the Secretary of State must brief Congress on the implementation of the ISA by November 8, 2012, and every 120 days thereafter. The Secretary of Treasury, pursuant to sections 216 and 220, must report to Congress on the implementation of sanctions on persons and entities who provide financial assistance to proliferation and terrorism activities.
The pace of Iran sanctions has accelerated rapidly in recent months and should be expected to continue to increase over the near and medium term. We will continue to provide our analysis of new developments here.
[1] On the same day the Executive Order was issued, OFAC issued a “Frequently Asked Questions” document providing guidance with regard to the Order.
[2] Sec. 218 – Liability of Parent Companies for Violations of Sanctions by Foreign Subsidiaries (requiring the President and the Secretary of Treasury to promulgate regulations within 60 days of enactment).
[3] ITRA §§ 221, 301-303.
Assimilate, Legal, Loyal, Self-Sustaining
Illegal, asylum, refugees, entitlements, protected class, surrendered
Record 63.2 million non-English speaking residents, surge in Arabic, Chinese, Spanish
By Paul Bedard
More than one in five U.S. residents speak a language other than English at home, a record, according to the U.S. Census Bureau.
In an analysis of the recent Census American Community Survey, a huge surge was recorded in those who speak Chinese, Spanish, Arabic and Urdu, Pakistan’s national language.
The report from the Center for Immigration Studies documented the growth of immigrants in the United States and provided evidence of concerns new immigrants are slow to assimilate into American culture, namely by speaking English at home.
According to the Center’s analysis released to Secrets Tuesday morning, in 2014, a record 63.2 million U.S. residents — native-born, legal immigrants, and illegal immigrants — spoke a language other than English at home. That represents a surge of 16.2 million since 2000 and 1.4 million just since 2013.
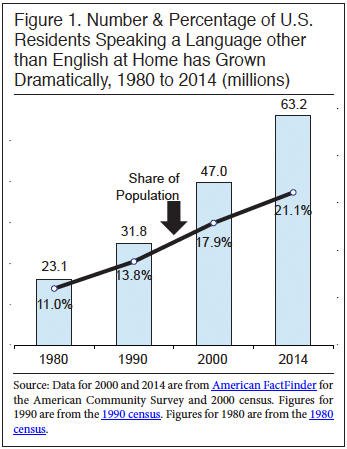
Overall, wrote the Center’s Steven A. Camarota and Karen Zeigler, the number of non-English speakers has doubled since 1990.
The top findings in the report titled “One in Five U.S. Residents Speaks Foreign Language at Home:”
- Since 1990 the number of foreign language speakers has roughly doubled; the number has almost tripled since 1980.
- In 2014, a record 63.2 million U.S. residents (native-born, legal immigrants, and illegal immigrants) spoke a language other than English at home. That number is up 16.2 million since 2000, up 3.6 million since 2010, and up 1.4 million just since 2013.
- Taking a longer view, since 1990 the number of foreign language speakers has roughly doubled.
- As a share of the population, 21 percent of U.S. residents speak a foreign language at home.
- The largest percentage increases from 2010 to 2014 were among speakers of Arabic (up 29 percent), Urdu (up 23 percent), Hindi (up 19 percent), Chinese and Hmong (both up 12 percent), and Gujarati and Persian (both up 9 percent). Urdu is spoken in Pakistan; Hindi and Guajarati are languages of India; Hmong is spoken in Laos; Persian is spoken in Iran.
- The largest numerical increases from 2010 to 2014 were among speakers of Spanish (up 2.3 million), Chinese (up 331,000), Arabic (up 252,000), Tagalog (up 115,000), Hindi (up 114,000), and Urdu (up 89,000). Tagalog is spoken in the Philippines.
- Languages with more than a million speakers in 2014 were Spanish (39. 3 million), Chinese (3.1 million), Tagalog (1.7 million), Vietnamese (1.5 million), French (1.2 million), and Korean and Arabic (1.1 million each).
- Of school-age children (five to 17), 22 percent speak a foreign language at home.
- Many of those who speak a foreign language at home are not immigrants. Of the more than 63 million foreign language speakers, 44 percent (27.7 million) were actually born in the United States.
- Of those who speak a foreign language at home, 25.6 million (41 percent) told the Census Bureau that they speak English less than very well.
One last item, the terror component:
Reuters: FBI counterterrorism investigators followed “dozens and dozens” of potential militants around the United States full time during the summer and “disrupted” many of them, FBI Director James Comey told a congressional committee on Thursday.
Comey, who testified before the Senate Committee on Homeland Security and Governmental Affairs along with Nick Rasmussen, director of the National Counterterrorism Center, said U.S. investigators are aware of dozens of U.S.-based Islamic militant suspects who now are using encrypted communications.
Comey said investigators had followed “dozens and dozens of people around the United States 24/7” during the summer and had “disrupted” them.
Comey told the committee that Islamic State recruits from the United States are incrementally younger with more “girls –women under 18” – seeking to join the militant group.
Rasmussen testified that Islamic State has overtaken al Qaeda as leader of the global violent extremist movement and has access to a large pool of potential recruits in Western countries.
He said counterterrorism experts still regard al Qaeda’s Yemen-based affiliate AQAP as big threat due to its interest in attacking the United States and airplanes.
Obama Does Gun Control, Putin Does Hockey, No Phone Calls
Scary with all this going on…no one is talking to each other especially when Defense Secretary Ash Carter says we will not cooperate or coordinate with Russia.
Carter: “Now, the Russians originally said they were going in to fight ISIL and al-Nusra and other terrorist organizations. However, within days of deploying their forces, the Russians began striking targets that are not any of these groups. I have said repeatedly over the last week that we, the United States, believed this is a fundamental strategic mistake and that it will inflame and prolong the Syrian civil war. We have not and will not agree to cooperate with Russia so long as they continue to pursue this misguided strategy. We’ve seen increasingly unprofessional behavior from Russian forces. They violated Turkish airspace, which as all of us here made clear earlier this week, and strongly affirmed today here in Brussels, is NATO airspace.” The full remarks by Carter while in Belgium are here.
Confluence or Conflating
Kearsarge ARG Deploys for Europe, Middle East Operations
The Kearsarge Amphibious Ready Group and 26th Marine Expeditionary Unit departed Oct. 6 from the East Coast for a deployment to the Middle East.
The more than 4,000 sailors and Marines will support theater security cooperation and maritime security operations and provide an added crisis response capability to U.S. 5th and 6th Fleet areas of operations.
The ARG/MEU includes amphibious assault ship USS Kearsarge (LHD-3), amphibious transport dock ship USS Arlington (LPD-24), amphibious dock landing ship USS Oak Hill (LSD-51),
Kearsarge and the 26th MEU last deployed from March to November 2013, during a time of great unrest in the region. Kearsarge and USS San Antonio (LPD-17) spent a lot of time in the northern part of the region – operating in the Mediterranean out of Rota, Spain, and in the northern Red Sea – while USS Carter Hall (LSD-50) spent time operating independently near Bahrain and Djibouti.
Upon returning home, Kearsarge spent five months in maintenance at BAE Systems Norfolk Ship Repair before beginning sea trials last summer. Kearsarge served as the flagship in the Bold Alligator 2014 amphibious exercise last fall.
Rocket Launch with Secret Payload
United Launch Alliance aims to launch its second Atlas V rocket in less than a week with a blastoff planned Thursday morning from California’s Central Coast.
The rocket is targeting a liftoff at 5:49 a.m. PT from Vandenberg Air Force Base, carrying a classified mission for the National Reconnaissance Office.
There’s a 70% chance of acceptable weather at Vandenberg’s Space Launch Complex-3. The full launch window has not been disclosed.
“We are excited and ready to take on our first Atlas launch of 2015,” said Col. J. Christopher Moss, commander of the 30th Space Wing, in a statement Wednesday. “Our team and mission partners have put a lot of hard work into preparing for this important mission for our nation.”
Amateur spacecraft observers speculate that the rocket is carrying a pair of satellites updating the Naval Ocean Surveillance System, or NOSS.In addition to the primary mission, the rocket’s Centaur upper stage will deliver a group of 13 experimental and student-developed CubeSats to orbit.
The tiny spacecraft include nine missions sponsored by the NRO and four by NASA. Kennedy Space Center’s Launch Services Program was responsible for securing the ride for the NASA-sponsored payloads known as ElaNA-12.
A successful launch would keep ULA on track to return to Cape Canaveral for an Oct. 30 launch of the Air Force’s next Global Positioning System satellite on an Atlas V. The booster for that mission was delivered to the Cape on Tuesday.
An Atlas V last Friday successfully delivered Mexico’s Morelos-3 communications satellite to orbit, completing ULA’s 100th launch since Boeing and Lockheed Martin formed the joint venture in December 2006.And Wednesday, in the first launch since an Antares rocket exploded shortly after takeoff on Oct. 29, 2014, a sounding rocket successfully blasted off from NASA’s Wallops Space Facility in Virginia.
“It wasn’t an easy decision,” an Iranian official source said when asked about Russia’s intervention in Syria. “The Russians were certain that if they did not move now, the next war they would fight would be inside their borders; this is about Russia’s national security before being about Syria. Therefore, a decision to start this pre-emptive war was taken by the Kremlin.”
For decades, Syria has been one of Russia’s main allies in the Middle East. The collapse of the Soviet Union didn’t change anything in this regard. Moscow continued to support Damascus with whatever necessary to keep the old empire’s last balcony on the warm waters of the Mediterranean Sea.
In 2011, amid the eruption of the revolution in Syria, the Russians started feeling the heat. It was almost obvious to them that the fall of the regime in Damascus would lead to serious changes in Russia’s status in the Middle East; thus this wasn’t an option to even think about, and everything possible should be done to maintain the regime and keep it breathing, should this be using the veto in the UN Security Council, sending arms and ammunitions, or as we are witnessing today, intervening militarily and fighting to keep the status quo. Russia is not the only ally of the Syrian government; Iran also has been supporting President Bashar al-Assad.
Russia and Iran have not previously been allies. They share common interests, common allies and common rivals; however, this doesn’t necessarily mean they act as allies. In Syria, their common interest has been — and still is — keeping their common ally, the regime, alive. Even within the Syrian regime, there are different views among the ranks on how to deal with both countries; there are officials who are seen as “Iranians” and others as “Russians.” This is prompted by fears among one wing that the Islamic Republic’s agenda in Syria involves Islamization of society, while the other wing that prefers the Iranians sees them as very reliable since they were the first to roll their sleeves up in the fight for the regime’s existence. Yet, this is only a matter of preferences, and nothing more.




