Primer:
The Justice Department on Tuesday announced plans to appeal a judge’s ruling that blocked President Donald Trump from shuttering a program that gave protections and work permits to some people who entered the U.S. illegally as children.
In a ruling last week, San Francisco-based U.S. District Court Judge William Alsup ordered the administration to resume accepting renewal applications for the Deferred Action for Childhood Arrivals program, better known as DACA. More here from Politico.
In part, highlights:
The Department has also implemented historic efforts to step up international cooperation. For the first time ever, DHS established a clear baseline for what countries must do to help the United States confidently screen travelers and immigrants from their territory. Every country in the world is now required to meet high security standards and to help us understand who is coming into our country.As required under President Trump’s Executive Order Protecting the Nation from Foreign Terrorist Entry into the United States (EO 13780), all foreign governments have been notified of the new standards, which include the sharing of terrorist identities, criminalhistory information, and other data needed to ensure public safety and national security, as well as the requirement that countries issue secure biometric passports, report lost and stolen travel documents to INTERPOL, and take other essential actions to prevent identity fraud.***Visa Waiver ProgramWe are also looking at ways to further strengthen the Visa Waiver Program (VWP). First and foremost, the VWP is a security partnership program. It mandates high and consistent standards from partner countries in the areas of national security, law enforcement, and immigration enforcement to detect and prevent terrorists, criminals, and other potentially dangerous individuals from traveling to the United States —while still facilitating legitimate travel and tourism.Currently, 38 countries participate in the VWP, which allows their citizens to travel to the United States for business or tourism for stays of up to 90 days after applying and being approved through the Electronic System for Travel Authorization (ESTA). In return, these countries must comply with program requirements to enter into information-sharing protocols that enable the relay of information concerning known and suspected terrorists and criminals; consistent and timely lost and stolen passport information reporting; and robust border and travel documentscreening. As a result of these program requirements, countries have adopted new laws, policies, and practices that strengthen our mutual security.The Visa Waiver Program Improvement and Terrorist Travel Prevention Act of 2015,combined with Secretarial action, have strengthened the VWP’s security provisions over the past two years.VWP countries are now required to issue high -security electronic passports (e-passports); implement information sharing arrangements to exchange terrorist identity information; establish mechanisms to validate e-passports at each key port of entry; report all lost and stolen passports to INTERPOL or directly to the United States no later than 24 hours after the country becomes aware of the loss or theft; and screen international travelers against the INTERPOL Stolen and Lost Travel Documents (SLTD) database and notices. As with other operational activities of DHS, a full discussion of the privacy impact of these initiatives and how we mitigate the risk to personal privacy is available on our website.Since enactment of the Visa Waiver Program Improvement and Terrorist Travel Prevention Act, DHS has realized an increase in the sharing of terrorist identity information. Several countries have increased the frequency of their reporting of lost and stolen passports —VWP countries account for over 70 percent of the almost 73 million lost and stolen travel documents reported to INTERPOL. All VWP countries are now issuing and using for travel to the United States fraud-resistant e-passports that meet or exceed the ICAO standards. Over 70,000 ESTA applicationshave been denied, cancelled or revoked under enforcement of the VWP Improvement Act’seligibility restrictions for VWP travel.Border SecurityIn compliance with Executive Order 13767: Border Security and Immigration EnforcementImprovements, DHS has conducted a comprehensive study of the security of the southern border that addresses all of the elements that provide an integrated solution for the Nation. Our first priority is to expand on our existing southern border wall system and close legal loopholes that encourage and enable illegal immigration and create a corresponding backlog in the courts. We currently have an immigration court backlog of more than 650,000 cases pending before the Department of Justice’s Executive Office for Immigration Review. We also have a massive asylum backlog with more than 270,000 pending cases before U.S. Citizenship and Immigration Services (USCIS).Recognizing the unsustainability of the asylum case backlog, USCIS has implemented efficiency measures designed to reduce adjudication times. Similarly, the Department of Justice has taken action to reduce unwarranted case continuances in immigration courts, which helps reduce the backlog while affording aliens full and fair hearings. To furtherreduce the “pull factors” and restore integrity to our immigration benefits adjudication process, we must tighten case processing standards, including the “credible-fear” standard, impose and enforce penalties for fraud, and ensure applicants are fully vetted before they are allowed access to the United States.In addition, visa-overstays account for roughly 40 percent of all illegal immigration in theUnited States. In FY 2016, more than 628,000 aliens overstayed their visas. By increasingoverstay penalties and expanding ICE’s enforcement tools, we can help ensure that foreignworkers, students, and visitors respect the terms of their temporary visas. We need Congress to authorize the Department to raise and collect fees from immigration benefit applications to fund additional enhancements to our immigration system called for by the President’s Executive Orders.Enforcing Immigration LawsWe are also prioritizing the enforcement of our immigration laws in the interior of our country.There are nearly one million aliens with final orders of removal across the country—meaning these removable aliens were afforded due process of law, had theirday in court, and were ultimately ordered removed by a judge — yet they remain in our nation and ICE only has 6,000 Deportation Officers to arrest and remove them. The Administration looks to strengthen law enforcement by hiring 10,000 more ICE officers and agents, and supports the request from the Department of Justice to hire 300 more federal prosecutors.To further protect our communities, we must end so-called “sanctuary” jurisdictions. Hundreds of state and local jurisdictions across the country that do not honor requests from ICE to hold criminal aliens who are already in state and local custody. Instead, they allow them back into their communities, where they are allowed to commit more crimes. This also poses a greater risk of harm to ICE officers, who must locate and arrest these criminals in public places, and increases the likelihood that the criminal aliens can resist arrest or flee. Rather than enhancing public safety, sanctuary jurisdictions undermine it.The only “sanctuary” these jurisdictions create is a safe haven for criminals. States and localities that refuse to cooperate with federal authorities should be ineligible for funding from certain grants and cooperative agreements.Authorizing and incentivizing states and localities to enforce immigration laws would further help ICE with its mission and make all communities safer.In FY 2017, 1,761 criminal illegal aliens were released from ICE custody because of a 2001Supreme Court decision that generally requires ICE to release certain removable aliens with final orders of removal—including violent criminals—within 180 days, if they have not been removed and there is no significant likelihood of removal in the reasonably foreseeable future. Legally insupportable judicial interpretations of the law regarding the detention and removability of criminal aliens have eroded ICE’s authority to keep aliens in custody pending removal.Pursuant to this Executive Order, USCIS announced it will take a more targeted approach to combatting fraud and abuse in the employment -based visa programs, including the H-1B program. To help end H-1B petitioner fraud and abuse, USCIS has established a Targeted Site Visit and Verification Program (TSVVP). Targeted site visits allow USCIS to focus its resources where fraud and abuse of certain programs are more likely to occur. TSVVP initially focused on H-1B petitions filed by companies that are H-1B dependent (as defined by statute), employers petitioning for H-1B workers who will be placed off -site at another company’s location, or cases where USCIS cannot validate the H-1B petitioner’s business information through commercially -available data.USCIS has also taken great strides to improve transparency with the public about employment -based immigration programs. The agency has published new data on its website to give the public more information regarding the use of nonimmigrant workers in the H-1B, H-2B, and L nonimmigrant programs. Information about the use and legal authority for employment authorization documents has also been published.Most low-skilled immigration into the United States occurs legally through ourimmigrant-visa system, which, unlike many other countries’ systems, prioritizes family-based chain-migration. Each year, the United States grants lawful permanent resident status (greencards) to more than one million people; two-thirds of that total is based on a person having a sponsoring relative in the United States, regardless of the new immigrant’s skills, education, English language proficiency, or ability to successfully assimilate. This system of chain-migration has accounted for more than 60 percent of immigration into the United States over the past 35 years. We must end chain-migration, and limit family -based green cards to spouses and the minor children of U.S. citizens and lawful permanent residents.We must also eliminate the “diversity visa” lottery. Every year, through this lottery, 50,000green cards are awarded at random to foreign nationals. Many of these lottery beneficiaries have absolutely no ties to the United States, no special skills, and limited education. The random lottery program has not been adopted by other countries and does not adequately serve our national interest. Full opening summary here.
Category Archives: Legislation
Google Worked for Democrats Against Republicans
Sounds precisely like the Obama IRS when it did the same thing. It is yet another kind of cyber war.If there is any doubt about Google CEO Eric Schmidt and Obama and Hillary –>
Clinton Status Memo Mentioning Google’s Eric Schmidt by Joe Schoffstall on Scribd
Google Punished Gudeman for His Views on Racism and Discrimination88. After being reported to Google, Google HR spoke with Gudeman in or aroundSeptember 2015 regarding his posts.89. Google HR discussed Gudeman’s viewpoints on race and/or gender equality, and hispolitical viewpoints. Google HR chastised him for attempting to stand up for Caucasian males and his conservative views.90. At the end of the HR meeting, Gudeman was issued a verbal warning.91. Gudeman complained to his colleagues about the lack of fairness that conservativesreceived at Google, and the leeway Google provided for liberals to express their thoughts and opinions without repercussions.92. After the 2016 presidential election, many employees at Google began to panic, havingexpected a different outcome fully in line with their political views.
131. Google’s management-sanctioned blacklists were directed at specific Googleemployees who tactfully expressed conservative viewpoints in politically-charged debates. In one case, Jay Gengelbach, a L6 SWE Manager, publicly bragged about blacklisting an intern for failing to change his conservative views.133. Kim Burchett (“Burchett”), a L7 SWE Manager, proposed creating an onlinecompanywide blacklist of political conservatives inside Google. She was kind enough to suggest to her readership that they might deserve “something resembling a trial” before being added.134. On August 7, 2015, another manager, Collin Winter, posted threats directed at a Google employee as a result of raising concerns of harassment and discriminationto Urs Holzle. Winter stated: “I keep a written blacklist of people whom I will never allow on or near my team, based on how they view and treat their coworkers. That blacklist got a little longer today.”135.Also on August 7, 2015, another manager, Paul Cowan, reshared Collin Winter’s threatto express his agreement with it and to indicate that he had also blacklisted Google employees with perceived conservative views. Cowan stated: “If you express a dunderheaded opinion about religion, about politics, or about ‘social justice’, it turns out I am allowed to think you’re a halfwit… I’m perfectly within my rights to mentally categorize you in my dickhead box… Yes, I maintain (mentally, and not (yet) publicly) [a blacklist]. If I had to work with people on this list, I would refuse, and try to get them removed; or I would change teams; or I would quit.”
UN Declaration, Regular, Constant Global Migration = Insurgency
Berlin – A new series launched by the Global Migration Data Analysis Centre (GMDAC) of IOM, the UN Migration Agency, aims to summarize the existing evidence on migration in an accurate and accessible fashion, to support discussions and any follow-up activities of the Global Compact for Safe, Orderly and Regular Migration.
Note the words orderly and regular….if the United Nations and peacekeeping operations as well as the aid, education, construction and protection campaigns were successful, migration would not be required especially in non-war torn countries. Right? Or how about all these other global human interest organizations….they failing too? Those like the Clinton Foundation or hey how about the Gates Foundation, which is a private foundation founded by Bill and Melinda Gates. It was launched in 2000 and is said to be the largest private foundation in the US, holding $38 billion in assets, improving lives from Seattle to South Africa….ahem.
Check here for the largest 10 organizations…. if all this work and money and resources were effective, then why the migration at all?
For the first time on 19 September 2016 Heads of State and Government came together to discuss, at the global level within the UN General Assembly, issues related to migration and refugees. This sent an important political message that migration and refugee matters have become major issues in the international agenda. In adopting the New York Declaration for Refugees and Migrants, the 193 UN Member States recognized the need for a comprehensive approach to human mobility and enhanced cooperation at the global level.
What are the aims of the global compact for migration?
The global compact is framed consistent with target 10.7 of the 2030 Agenda for Sustainable Development in which member States committed to cooperate internationally to facilitate safe, orderly and regular migration and its scope is defined in Annex II of the New York Declaration. It is intended to:
- address all aspects of international migration, including the humanitarian, developmental, human rights-related and other aspects;
- make an important contribution to global governance and enhance coordination on international migration;
- present a framework for comprehensive international cooperation on migrants and human mobility;
- set out a range of actionable commitments, means of implementation and a framework for follow-up and review among Member States regarding international migration in all its dimensions;
- be guided by the 2030 Agenda for Sustainable Development and the Addis Ababa Action Agenda; and
- be informed by the Declaration of the 2013 High-Level Dialogue on International Migration and Development.
The development of the global compact for migration – an open, transparent and inclusive process
The Modalities Resolution for the intergovernmental negotiations of the global compact for safe, orderly and regular migration outline the key elements and timeline of the process. The global compact will be developed through an open, transparent and inclusive process of consultations and negotiations and the effective participation of all relevant stakeholders, including civil society, the private sector, academic institutions, parliaments, diaspora communities, and migrant organizations in both the intergovernmental conference and its preparatory process.
N Korea Nuke Sites Go Further Underground
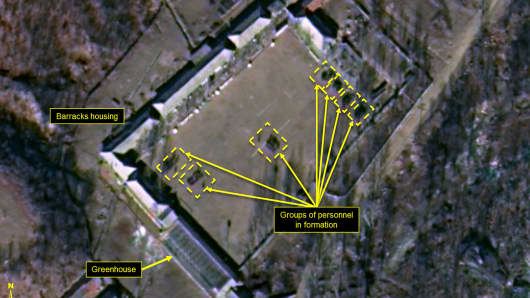
“Significant tunneling” excavation is underway at North Korea’s Punggye-ri nuclear test site and shows the regime’s continued efforts to maintain the site for potential future nuclear testing, a think tank specializing in tracking North Korean activities reported Thursday.
It follows reports in October that the test site is unstable and experienced tunnel collapses that have killed several hundred North Korean laborers.
The report on the 38 North website was based on an analysis of new commercial satellite images released of Punggye-ri, where the North Koreans have conducted the last six underground nuclear tests. It said throughout December 2017, there were “mining carts and personnel” as well as what appeared to be a “spoil pile” that had been greatly expanded at the test facility’s west portal.
The test site’s north portal, used in the last five nuclear tests, “remains dormant,” but there’s new activity at the west portal, according to the 38 North, a think tank at the Johns Hopkins School of Advanced International Studies. Yet, it said there appears to be draining going on at the entrance to this portal.
The last nuclear test at Punggye-ri was conducted in September. Pyongyang claimed that blast was a miniaturized hydrogen weapon designed for an intercontinental ballistic missile.
In October, Japan’s Asahi TV reported that as many as 200 North Korean workers may have been killed in a tunnel collapse at the nuclear test site. Also, at least four defectors from North Korea have shown signs of radiation exposure, Reuters reported last month.
In Thursday’s report, 38 North said about 100 to 200 people were observed in satellite images taken Dec. 28 in a “Southern Support Area,” which it said rarely has such activity. And it said “the purpose of their activities is unknown.”
The new analysis of the Punggye-ri satellite imagery was done by Frank Pabian, Joseph Bermudez Jr. and Jack Liu, the 38 North website said. They concluded that the recent activity is a sign that the regime will maintain the facility.
The recent activity at the Punggye-ri nuclear test site comes on the heels of North and South Korean negotiators meeting Tuesday at the Demilitarized Zone. It was the first high-level talks between the two countries since late 2015.
The negotiations resulted in Pyongyang agreeing to send a delegation of athletes to the upcoming Winter Olympic Games in PyeongChang, South Korea. The two sides also agreed to reinstate a military hotline and to hold future talks, although no deal was reached on denuclearization.
Also, South Korea’s Yonhap news agency reported Thursday that Chinese President Xi Jinping had a 30-minute phone conversation with South Korean President Moon Jae-in and they jointly agreed “to continue working together to peacefully resolve the North Korean nuclear issue.”
US Treasury to Publish Russian Oligarch Corruption Index
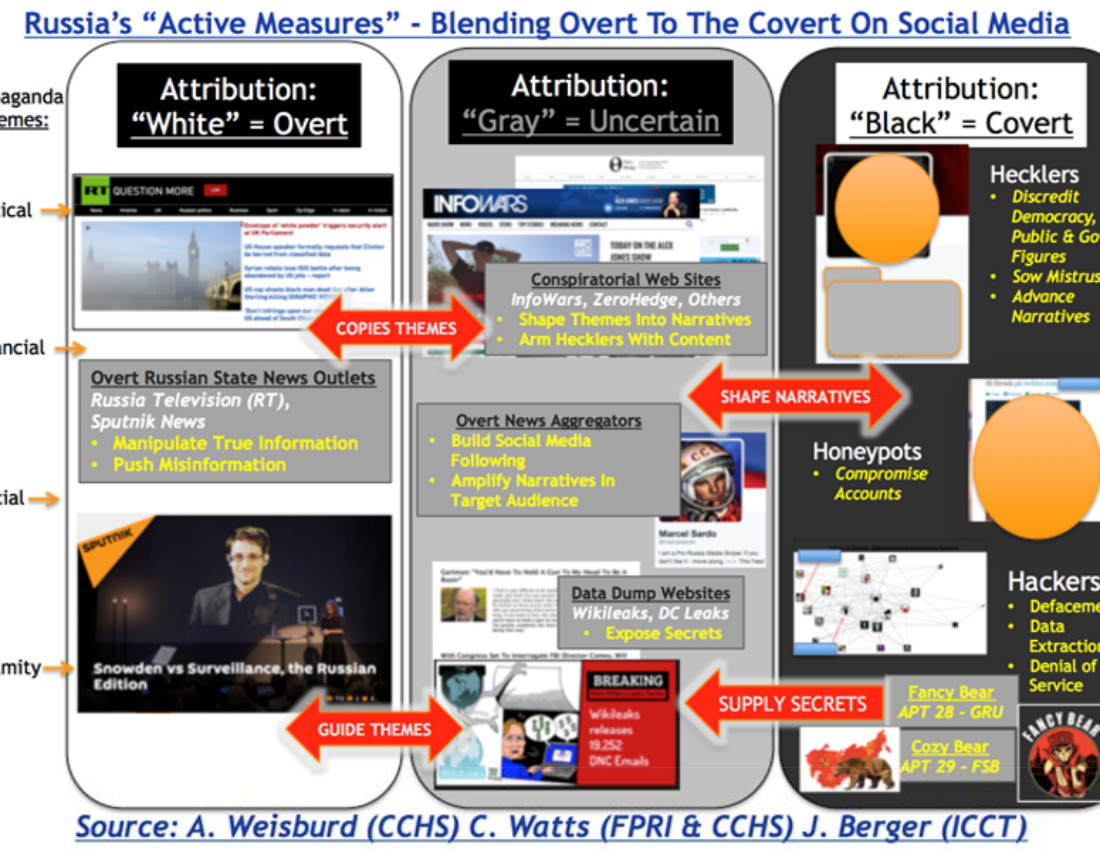
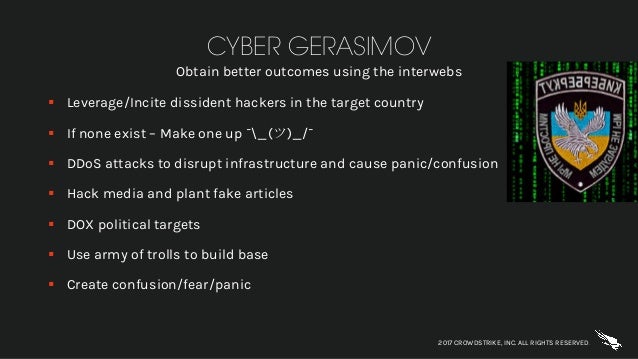
In December of 2015, Obama took aggressive action expelling Russian diplomats over hacking and political intrusion.
“In addition, the Russian Government has impeded our diplomatic operations by, among other actions — forcing the closure of 28 American corners which hosted cultural programs and English-language teaching; blocking our efforts to begin the construction of a new, safer facility for our Consulate General in St Petersburg; and rejecting requests to improve perimeter security at the current, outdated facility in St Petersburg.” Some additional actions and those expelled include:
Two Russian intelligence agencies, the GRU and the FSB, four GRU officers and three companies “that provided material support to the GRU’s cyber operations”.
The White House named Igor Valentinovich Korobov, the current chief of the GRU; Sergey Aleksandrovich Gizunov, deputy chief of the GRU; Igor Olegovich Kostyukov, a first deputy chief of the GRU; and Vladimir Stepanovich Alexseyev, also a first deputy chief of the GRU. The Obama Executive Order is here.
Russia’s Oligarchs Brace for U.S. List of Putin Friends
(Bloomberg) — The U.S. Treasury Department is finishing its first official list of “oligarchs” close to President Vladimir Putin’s government, setting off a flurry of moves by wealthy Russians to shield their fortunes and reputations.
Some people who think they’re likely to land on the list have stress-tested the potential impact on their investments, two people with knowledge of the matter said. Others are liquidating holdings, according to their U.S. advisers.
Russian businessmen have approached former Treasury and State Department officials with experience in sanctions for help staying off the list, said Dan Fried, who previously worked at the State Department and said he turned down such offers.
Some Russians sent proxies to Washington in an attempt to avoid lobbying disclosures, according to one person that was contacted.
The report is expected to amount to a blacklist of Russia’s elite. It was mandated by a law President Donald Trump reluctantly signed in August intended to penalize the Kremlin for its alleged meddling in the 2016 election.
A rare piece of legislation passed with a bipartisan veto-proof margin, the law gave Treasury, the State Department and intelligence agencies 180 days to identify people by “their closeness to the Russian regime and their net worth.”
That deadline is Jan. 29.
Shamed Oligarchs
The list has also become a headache within Treasury, where some officials are concerned it will be conflated with sanctions, a person familiar with the matter said.
Treasury officials are considering keeping some portions of the report classified — which the law allows — and issuing it in the form of a letter from a senior official, Sigal Mandelker, instead of releasing it through the Office of Foreign Assets Control, which issues sanctions.
That would help distinguish it from separate lists of Russians subject to U.S. economic penalties, said the person, who spoke on condition of anonymity.
“You’re going to have people getting shamed. It’s a step below a sanction because it doesn’t actually block any assets, but has the same optics as sanctions — you’re on a list of people who are engaged in doing bad things,” said Erich Ferrari, who founded Ferrari & Associates in Washington and has helped people get removed from the sanctions designation list.
Corruption Index
The report must include “indices of corruption” with the oligarch’s names and list any foreign assets they may own. Lawmakers expect the list to provide a basis for future punitive actions against Russia.
“Because of the nervousness that the Russian business community is facing, a number of oligarchs are already beginning to wind back businesses, treating them as if they are already designated, to stay ahead of it,” said Daniel Tannebaum, head of Pricewaterhousecoopers LLP’s global financial sanctions unit.
He advises a handful of wealthy Russian individuals and some businesses who he declined to identify.
Treasury’s terrorism and financial intelligence unit is working with the State Department and Office of National Intelligence to complete the report, said a spokesman who declined to elaborate on the criteria for the list or whether it would be made public.
“It should be released in the near future,” Treasury Secretary Steve Mnuchin said at a White House briefing. ‘It’s something we’re very focused on.”
‘Allows Mischief’
The list’s impact will depend on how it’s released, said Adam Smith, a former senior adviser in Treasury’s sanctions unit and now a partner at Gibson, Dunn & Crutcher LLP in Washington.
The law is “written in a way that it allows mischief if the administration wanted to go a different way,” Smith said. “If the president wanted to provide little or a lot and be very selective, he has the ability to do that.”
That discretion partly flows from the criteria used to assemble the list, which Congress left up to Treasury.
Senator Ben Cardin of Maryland, the ranking Democrat on the committee on foreign relations, said he would like to see “as much transparency as possible” from Treasury when it finishes the list.
Russia has sought to defend its elites. Putin warned of worsening U.S. sanctions last month and introduced a capital amnesty program to encourage wealthy nationals to repatriate some of their overseas assets.
He also approved a plan to issue special bonds designed to give the wealthy a way to hold their dollar assets out of reach of the U.S. Treasury.
‘Disgusting’ Relations
While compilation of the list doesn’t mean there’ll be a new round of tit-for-tat sanctions, Russia will react to any punitive measures against its business people, Kremlin spokesman Dmitry Peskov told reporters on a conference call Friday.
“The principle of reciprocity remains,” and it would be for Putin to decide on the best response, he said.
Prime Minister Dmitry Medvedev, a Putin lieutenant for two decades, called the state of the relationship “disgusting” in November.
Congress has also requested that Treasury submit an impact analysis of potential sanctions on Russian sovereign bonds. A Treasury spokesman said its international affairs office is working on the analysis.
U.S. sanctions on the bonds would deal a major blow to Russia’s finances, raising the prospect of a selloff in the bond market, posing a risk to the ruble and the potential for higher borrowing costs.
The Russian Finance Ministry relies on debt to cover budget shortfalls and is seeking to borrow $18 billion domestically in 2018.