The Guardian takes huge exception to what President Trump said. There is merit in the Guardian’s rebuke. What could be in question however, is the outcome of the estimated thousand domestic cases the FBI is or was investigating, and this does remain unclear. Yet, it could be too that President Trump and his team are conflating the definition of terror attacks as there are cases of murder, too many to list done at the hands of illegals across the homeland.
So, as a review, it is important to go over the list as provided by the Guardian. It is a chilling history on its face.
****
The full list of Trump’s ‘under-reported’ terror attacks – and how they were reported
What does the White House’s choice of ‘cases the very, very dishonest press doesn’t want to report’ tell us?
TIMELINE: September, 2014 – December, 2016
NUMBER OF ATTACKS: 78
It is not clear why these dates were chosen. A December 2016 cut-off excludes the Québec City mosque attack from the list. There were more than 78 terrorist attacks in that period – the ones selected by the White House are almost exclusively those linked – or rumoured to be linked – to Islamic State. The White House text is reproduced in bold and its errors have been kept.
MELBOURNE, AUSTRALIA September, 2014
TARGET: Two police officers wounded in knife attack
ATTACKER: Abdul Numan Haider
Global media organisations including the Guardian, BBC, CNN and Fox News were among those who covered this story.
TIZI OUZOU, ALGERIA September, 2014
TARGET: One French citizen beheaded
ATTACKER: Jund al-Khilafah in Algeria
Algerian militant group Jund al-Khilafah broke its former allegiance with al-Qaida to pledge itself to Isis.

QUEBEC, CANADA October, 2014
TARGET: One soldier killed and one wounded in vehicle attack
ATTACKER: Martin Couture-Rouleau
The Saint-Jean-sur-Richelieu ramming attack was described by the Canadian government and police as Isis-inspired.
OTTAWA, CANADA October, 2014
TARGET: One soldier killed at war memorial; two wounded in shootings at Parliament building
ATTACKER: Michael Zehaf-Bibeau
Read the Guardian’s live coverage here.

NEW YORK CITY, NY, USA October, 2014
TARGET: Two police officers wounded in knife attack
ATTACKER: US person
This is vague but seems to refer to Zale Thompson, also known as Zaim Farouq Abdul-Malik, described as a “self-radicalised” Muslim convert. He was killed by police.
RIYADH, SAUDI ARABIA November, 2014
TARGET: One Danish citizen wounded in shooting
ATTACKERS: Three Saudi Arabia-based ISIL members
Read a news report here.
ABU DHABI, UAE DATE: December 2014
TARGET: One American killed in knife attack
ATTACKER: Dalal al-Hashimi
Read a news report here.
SYDNEY, AUSTRALIA December, 2014
TARGET: Two Australians killed in hostage taking and shooting
ATTACKER: Man Haron Monis
The Martin Place siege received blanket worldwide coverage.

TOURS, FRANCE December, 2014
TARGET: Three police officers wounded in knife attack
ATTACKER: Bertrand Nzohabonayo
Read a news report here.
PARIS, FRANCE January, 2015
TARGET: One police officer and four hostages killed in shooting at a kosher supermarket
ATTACKER: Amedy Coulibaly
The killings – part of the series of attacks around the Charlie Hebdo massacre – received global attention. Coulibaly had claimed to be acting for Isis. Curiously, the linked attacks by the Kouachi brothers, who had pledged allegiance to al-Qaida in the Arabian Peninsula, are not on the list.
TRIPOLI, LIBYA January, 2015
TARGET: Ten killed, including one US citizen, and five wounded in bombing and shooting at a hotel frequented by westerners
ATTACKERS: As many as five ISIL-Libya members
Read a news report here.

RIYADH, SAUDI ARABIA January, 2015
TARGET: Two US citizens wounded in shooting
ATTACKER: Saudi Arabia-based ISIL supporter
It’s not clear to which incident this refers. It could be two employees of Vinnell Arabia who were attacked by a former colleague in Al Ahsa, not Riyadh, that month; or the killing in October 2014 of another US VA employee, which did take place in Riyadh.
NICE, FRANCE February, 2015
TARGET: Two French soldiers wounded in knife attack outside a Jewish community center
ATTACKER: Moussa Coulibaly
COPENHAGEN, DENMARK February, 2015
TARGET: One civilian killed in shooting at a free-speech rally and one security guard killed outside the city’s main synagogue
ATTACKER: Omar Abdel Hamid el-Hussein
Read a news report here.

TUNIS, TUNISIA March, 2015
TARGET: 21 tourists killed, including 16 westerners, and 55 wounded in shooting at the Bardo Museum
ATTACKERS: Two ISIL-aligned extremists
In fact 22 people were killed, not including two perpetrators. Mention of “16 westerners” presumably excludes the Tunisian, Japanese and Colombian victims. Isis did claim responsibility but the Tunisian government blamed an al-Qaida splinter group. The story was carried live by many news outlets.
KARACHI, PAKISTAN April, 2015
TARGET: One US citizen wounded in knife attack
ATTACKERS: Pakistan-based ISIL supporters
No report of this could be found. However, an American woman, Debra Lobo, was shot and wounded in April 2015 in Karachi by a reported Isis sympathiser.
PARIS, FRANCE April, 2015
TARGET: Catholic churches targeted; one civilian killed in shooting, possibly during an attempted carjacking
ATTACKER: Sid Ahmed Ghlam
Sid Ahmed Ghlam is charged with the attack and is awaiting trial.
ZVORNIK, BOSNIA April, 2015
TARGET: One police officer killed and two wounded in shooting
ATTACKER: Nerdin Ibric
It is true there are few English-language reports on this attack. Here is one.

GARLAND, TX, USA May, 2015
TARGET: One security guard wounded in shooting at the Prophet Muhammad cartoon event
ATTACKERS: Two US persons
The “two US persons” were Elton Simpson and Nadir Soofi, both killed in the attack.
BOSTON, MA, USA June, 2015
TARGET: No casualties; one police officer attacked with knife
ATTACKER: US person
Very vague but could refer to Usaama Rahim, who was shot dead by police after officers said he “threatened” (not “attacked”) them with a knife. He was under counter-terrorism surveillance.
EL GORA (AL JURAH), EGYPT June, 2015
TARGET: No casualties; camp used by Multinational Force and Observers (MFO) troops attacked in shooting and bombing attack
ATTACKERS: Unknown number of ISIL-Sinai members
Few reports on this in mainstream press, possibly explained by the “no casualties”.
LUXOR, EGYPT June, 2015
TARGET: One police officer killed by suicide bomb near the Temple of Karnak
ATTACKER: Unidentified
This could be wrong. A police officer sustained minor injuries in an attempted suicide bombing at Karnak in which two would-be assailants were killed and one injured. Possibly muddled with an earlier attack near Giza pyramids in which two police officers were killed.
SOUSSE, TUNISIA June, 2015
TARGET: 38 killed and 39 wounded in shooting at a beach frequented by westerners
ATTACKERS: Seifeddine Rezgui and another unidentified attacker
The Sousse massacre was extensively covered. Inquests into the deaths of British victims are ongoing.

LYON, FRANCE June, 2015
TARGET: One civilian killed in beheading and explosion at a chemical plant
ATTACKER: Yasin Salhi
The suspect’s name was Yassin Salhi.
CAIRO, EGYPT July, 2015
TARGET: One killed and nine wounded in VBIED attack at Italian Consulate
ATTACKER: Unidentified ISIL operatives
Read a news report here.
CAIRO, EGYPT July, 2015
TARGET: One Croatian national kidnapped; beheaded on August 12 at an unknown location
ATTACKER: Unidentified ISIL-Sinai operative
The kidnapping and beheading of Tomislav Salopek received worldwide attention.
PARIS, FRANCE August, 2015
TARGET: Two civilians and one US soldier wounded with firearms and knife on a passenger train
ATTACKER: Ayoub el-Khazzani
Passengers who helped subdue the attacker were awarded the French legion of honour. Barack Obama personally called the three Americans involved to thank them.
EL GORA, EGYPT September, 2015
TARGET: Four US and two MFO troops wounded in IED attack
ATTACKER: Unidentified
Read news reports here.
DHAKA, BANGLADESH September, 2015
TARGET: One Italian civilian killed in shooting
ATTACKER: Unidentified
This could refer to the aid worker Cesare Tavella. Isis claimed responsibility.

COPENHAGEN, DENMARK September, 2015
TARGET: One police officer wounded in knife attack
ATTACKER: Palestinian national
It is not clear why the list spells “attacker” as “attaker” from here onwards.
EL GORA, EGYPT October, 2015
TARGET: No casualties; airfield used by MFO attacked with rockets
ATTAKER: Unidentified ISIL-Sinai operatives
News reports on this could not be found.
PARRAMATTA, AUSTRALIA October, 2015
TARGET: One police officer killed in shooting
ATTAKER: Farhad Jabar
The killing was widely reported in Australia and worldwide.
RANGPUR, BANGLADESH October, 2015
TARGET: One Japanese civilian killed in shooting
ATTAKER: Unidentified
Isis claimed responsibility for the death of Kunio Hoshi.
HASANAH, EGYPT October, 2015
TARGET: 224 killed in downing of a Russian airliner
ATTAKER: Unidentified ISIL-Sinai operatives
The Sinai plane crash was the subject of massive global media coverage.
MERCED, CA, US November, 2015
TARGET: Four wounded in knife attack on a college campus
ATTAKER: US person
Faisal Mohammad, whom the FBI called an Isis-inspired “lone wolf”, was shot dead. But why highlight this and the Ohio State University attack and not, say, these other campus attacks?
PARIS, FRANCE November, 2015
TARGET: At least 129 killed and approximately 400 wounded in series of shootings and IED attacks
ATTAKERS: Brahim Abdelslam, Saleh Abdeslam, Ismail Mostefai, Bilal Hadfi, Samy Amimour, Chakib Ahrouh, Foued Mohamed Aggad, and Abdelhamid Abaaoud
The White House surely cannot include the Paris attacks in the “most” on this list that it thinks were under-reported. It omits the names of three of the 11 men involved in the attack, and spells Chakib Akrouh’s name wrong. The death toll for the attacks stands at 130.

DINAJPUR, BANGLADESH November, 2015
TARGET: One Italian citizen wounded in shooting
ATTAKER: Unidentified
This appears to refer to the attack on the priest Piero Parolari.
RAJLOVAC, BOSNIA December, 2015
TARGET: Two Bosnian soldiers killed in shooting
ATTAKER: Enes Omeragic
Read news reports here.
SAN BERNADINO, CA, US December, 2015
TARGET: 14 killed and 21 wounded in coordinated firearms attack
ATTAKERS: Two US persons
The spelling should be San Bernardino. The “two US persons” were Syed Rizwan Farook and Tashfeen Malik. Media coverage extended to networks carrying live footage as reporters entered the couple’s home.

LONDON, ENGLAND, UK December, 2015
TARGET: Three wounded in knife attack at an underground rail station
ATTAKER: Muhyadin Mire
The stabbing was covered in the US as well as across the UK. Mire was jailed for life.
DERBENT, RUSSIA December, 2015
TARGET: One killed and 11 wounded in shooting at UN World Heritage site
ATTAKER: Unidentified ISIL-Caucasus operative
Read news reports here.
CAIRO, EGYPT January, 2016
TARGET: Two wounded in drive-by shooting outside a hotel frequented by tourists
ATTAKERS: Unidentified ISIL operatives
Another unclear one. There was a drive-by shooting outside a Cairo hotel that month, though no injuries were reported. A police officer and a soldier were shot dead in a separate incident in the following days.
PARIS, FRANCE January, 2016
TARGET: No casualties; attacker killed after attempted knife attack on Paris police station
ATTAKER: Tarek Belgacem
Read news reports here and here.
PHILADELPHIA, PENNSYLVANIA January, 2016
TARGET: One police officer wounded in shooting
ATTAKER: US person
The case of Jesse Hartnett, the police labor union said after the White House claim, was covered adequately and fairly.
HURGHADA, EGYPT January, 2016
TARGET: One German and one Danish national wounded in knife attack at a tourist resort
ATTAKER: Unidentified
As with the Cairo incident cited above, this is not clear. Three people – two Austrians and a Swede – were stabbed at a Hurghada resort. One perpetrator was shot dead.
MARSEILLES, FRANCE January, 2016
TARGET: One Jewish teacher wounded in machete attack
ATTAKER: 15 year-old Ethnic Kurd from Turkey
Read a news report here.
ISTANBUL, TURKEY January, 2016
TARGET: 12 German tourists killed and 15 wounded in suicide bombing
ATTAKER: Nabil Fadli
Thirteen people were killed. Turkey said Isis was responsible.

JAKARTA, INDONESIA January, 2016
TARGET: Four civilians killed and more than 20 wounded in coordinated bombing and firearms attacks near a police station and a Starbucks
ATTAKERS: Dian Joni Kurnaiadi, Muhammad Ali, Arif Sunakim, and Ahmad Muhazan bin Saron
See the Guardian’s live coverage here.
COLUMBUS, OH, US February, 2016
TARGET: Four civilians wounded in machete attack at a restaurant
ATTAKER: US person
This received widespread coverage in the US. The “US person” was Mohamed Barry, who was shot dead by police.
HANOVER, GERMANY February, 2016
TARGET: One police officer wounded in knife attack
ATTAKER: Safia Schmitter
The incident was covered by media but most chose not to identify the alleged attacker, who was 15.
ISTANBUL, TURKEY March, 2016
TARGET: Four killed and 36 wounded in suicide bombing in the tourist district
ATTAKER: Mehmet Ozturk
Read a news report here.
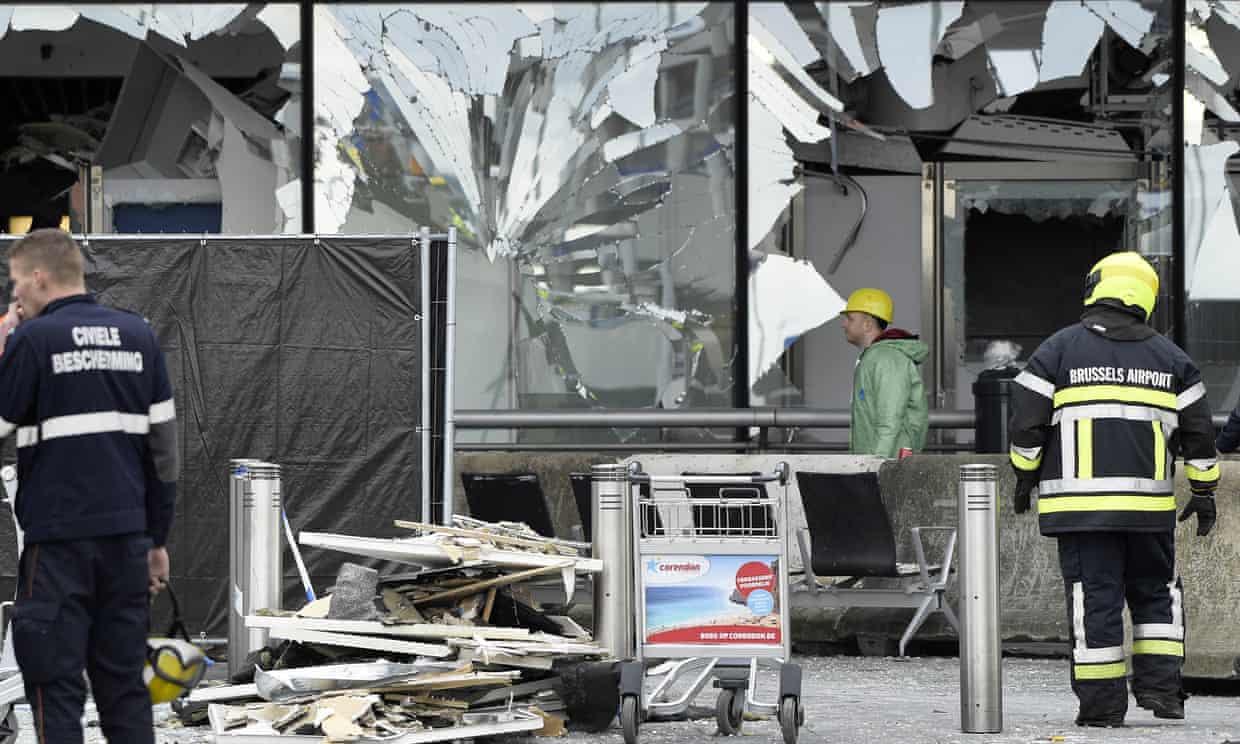
BRUSSELS, BELGIUM March, 2016
TARGET: At least 31 killed and 270 wounded in coordinated bombings at Zaventem Airport and on a subway train
ATTAKERS: Khalid el-Bakraoui, Ibrahim el-Bakraoui, Najim Laachraoui, Mohammed Abrini, and Osama Krayem
The attack on Brussels garnered wall-to-wall media coverage. The death toll was 32.
ESSEN, GERMANY April, 2016
TARGET: Three wounded in bombing at Sikh temple
ATTAKERS: Three identified minors
Three boys are charged with attempted murder.
ORLANDO, FL, US June, 2016
TARGET: 49 killed and 53 wounded in shooting at a nightclub
ATTAKER: US person
The worst mass shooting by a single perpetrator in US history was far from “under-reported”. The “US person” responsible was Omar Mateen.

MAGNANVILLE, FRANCE June, 2016
TARGET: One police officer and one civilian killed in knife attack
ATTAKER: Larossi Abballa
Read a news report here.
KABUL, AFGHANISTAN June, 2016
TARGET: 14 killed in suicide attack on a bus carrying Canadian Embassy guards
ATTAKER: ISIL-Khorasan operative
Although mostly covered in Canada, the attack was reported globally. The victims were Nepalese.
ISTANBUL, TURKEY June, 2016
TARGET: 45 killed and approximately 240 wounded at Ataturk International Airport
ATTACKERS: Rakhim Bulgarov, Vadim Osmanov, and an unidentified ISIL operative
Another deadly attack in Turkey dominated news headlines. The two identified perpetrators are reported to be Russian.
DHAKA, BANGLADESH July, 2016
TARGET: 22 killed, including one American and 50 wounded after hours-long siege using machetes and firearms at holy Artisan Bakery
ATTACKERS: Nibras Islam, Rohan Imtiaz, Meer Saameh Mubasheer, Khairul Islam Paye, and Shafiqul Islam Uzzal
The location was the Holey Artisan Bakery; 22 civilians and two police officers were killed.
NICE, FRANCE July, 2016
TARGET: 84 civilians killed and 308 wounded by an individual
ATTACKER: Mohamed Bouhlel
86 people were killed by Mohamed Lahouaiej-Bouhlel.

WURZBURG, GERMANY July, 2016
TARGET: Four civilians wounded in axe attack on a train
ATTACKER: Riaz Khan Ahmadzai
Read a news report here.
ANSBACH, GERMANY July, 2016
TARGET: At least 15 wounded in suicide bombing at a music festival
ATTACKER: Mohammad Daleel
See the Guardian’s live coverage.
NORMANDY, FRANCE July, 2016
TARGET: One priest killed in knife attack
ATTACKERS: Adel Kermiche and Abdel Malik Nabil Petitjean
The killing provoked horror and was covered globally.
CHALEROI, BELGIUM August, 2016
TARGET: Two police officers wounded in machete attack
ATTACKER: Khaled Babouri
It is Charleroi. See the Guardian report.

QUEENSLAND, AUSTRALIA August, 2016
TARGET: Two killed and one wounded in knife attack at a hostel frequented by Westerners
ATTACKER: Smail Ayad
Smail Ayad has been charged but not brought to trial; proceedings have been suspended and referred to the mental health court. Police and the mother of one of the victims have said extremism was not a factor.
COPENHAGEN, DENMAKR September, 2016
TARGET: Two police officers and a civilian wounded in shooting
ATTACKER: Mesa Hodzic
It is Denmark. Isis claimed responsibility – the attacker is dead – but it is thought the crime could be linked to drugs.
PARIS, FRANCE September, 2016
TARGET: One police officer wounded in raid after VBIED failed to detonate at Notre Dame Cathedral
ATTACKERS: Sarah Hervouet, Ines Madani, and Amel Sakaou
Read the Guardian report here.
SYDNEY, AUSTRALIA September, 2016
TARGET: One civilian wounded in knife attack
ATTACKER: Ihsas Khan
Ihsas Khan has been charged but still awaits trial.
ST. CLOUD, MN, US September, 2016
TARGET: 10 wounded in knife attack in a mall
ATTACKER: Dahir Ahmed Adan
Read the Guardian report here.
NEW YORK, NY; SEASIDE PARK AND ELIZABETH, NJ, US September, 2016
TARGET: 31 wounded in bombing in New York City; several explosive devices found in New York and New Jersey; one exploded without casualty at race in New Jersey; one police officer wounded in shootout
ATTACKER: Ahmad Khan Rahami
Rahami has been charged but no trial date has been set.

BRUSSELS, BELGIUM October, 2016
TARGET: Two police officers wounded in stabbing
ATTACKER: Belgian national
Belgian prosecutors said the attack could be terrorism-related.
KUWAIT CITY, KUWAIT
TARGET: No casualties; vehicle carrying three US soldiers hit by a truck
ATTACKER: Ibrahim Sulayman
The soldiers were not harmed. The attempted attack was reported.
MALMO, SWEDEN October, 2016
TARGET: No casualties; mosque and community center attacked with Molotov cocktail
ATTACKER: Syrian national
A Malmo court charged a man with arson but said it was not a terrorism offence.
HAMBURG, GERMANY October, 2016
TARGET: One killed in knife attack
ATTACKER: Unknown
The story that a 16-year-old boy had been killed attracted global attention. Isis claimed responsibility but police say a motive has not been confirmed.
MANILA, PHILIPPINES November, 2016
TARGET: No casualties; failed IED attempt near US Embassy
ATTACKERS: Philippine nationals aligned with the Maute group
Police said there were no explosives in the package.
COLUMBUS, OH, US November, 2016
TARGET: 14 wounded by individuals who drove a vehicle into a group of pedestrians and attacked them with a knife
ATTACKER: US person
Read the Guardian report here.
N’DJAMENA, CHAD November, 2016
TARGET: No casualties; attacker arrested after opening fire at entrance of US Embassy
ATTACKER: Chadian national
This one was barely covered by media. There were no injuries.
KARAK, JORDAN December, 2016
TARGET: 10 killed and 28 wounded in shooting at a tourist site
ATTACKERS: Several gunmen
Read the Guardian report here.
BERLIN, GERMANY December, 2016
TARGET: 12 killed and 48 wounded by individual who drove truck into a crowded market
ATTACKER: Anis Amri
The Berlin Christmas market attack dominated the news agenda in the run-up to Christmas.