Sitting on the knife’s edge when it comes to protecting people’s communication from investigative agencies like the FBI and the NSA is a slippery and inexact argument. The Director of the FBI, James Comey has begged Congress for some legislation such that some encryption can be broken for terror and other criminal cases to be investigated yet nothing is forthcoming and not likely in the future.
In remarks at the American Law Institute on Tuesday and at a cyber security summit on Wednesday at Georgetown University Law Center, Comey said the group calling itself the Islamic State, or ISIL, represents the FBI’s most urgent threat. He described the organization’s use of social media to motivate troubled people in the United States to engage in acts of violence—either by traveling to the so-called caliphate or killing where they are. Comey said ISIL reaches out to individuals on Twitter and elsewhere, then moves their more sensitive communications to encrypted platforms.
“The threat we face has morphed,” Comey said on Wednesday. “It’s a chaotic spider web through social media—increasingly invisible to us because the operational communications are happening in an encrypted channel.”
Comey later elaborated on the issue of encryption, which is a process of encoding messages—on mobile phones for example—that only authorized parties can access. While it can be effective at thwarting digital thieves, strong encryption also limits the amount of information—or evidence—that law enforcement can effectively gather from a device.
“Increasingly we’re finding ourselves unable to read what we find, or unable to open a device,” Comey said, “and that is a serious concern.”
The issue of “going dark,” as the Bureau calls it, is worthy of a larger public conversation about the balance between privacy and public safety, Comey said. Momentum toward universal encryption, he explained, may have unintended consequences.
“As all of our lives become digital, the logic of encryption is all of our lives will be covered by strong encryption, and therefore all of our lives—including the lives of criminals and terrorists and spies—will be in a place that is utterly unavailable to court-ordered process,” he said. “And that, I think, to a democracy should be very, very concerning.”
The Director also pointed to provisions of the Patriot Act of 2001 that, if allowed to expire on June 1, could hobble the FBI’s investigative abilities. One of the provisions is Section 215, which authorized the National Security Agency’s database of telephony records and metadata.
Comey said the FBI relies on that provision fewer than 200 times a year—in particular cases to get particular records. “If we lose that authority,” Comey said, “we can’t get information that I think everybody wants us to attain.”
Two other provisions include:
- Roving wiretaps. The FBI has had authority since the 1980s to use legally authorized roving wiretaps in criminal cases—allowing authorities to follow surveillance targets rather than their phones, which can be easily trashed and replaced. The Patriot Act extended that authority to terrorism and counterintelligence cases.
- The Lone Wolf provision. In 2004, Congress amended the Foreign Intelligence Surveillance Act to authorize intelligence gathering on individuals not affiliated with any known terrorist organization.
“These three are going to go away June 1,” Comey said, “and I don’t want them to get lost in the conversation about metadata.”
It was not but a few months ago, the leadership of Islamic State (ISIS) published an edict for the top terror commanders to use an app called ‘Telegram’ and they are.
Now what? How is the conflict of civil liberties resolved?
Why Telegram has become the hottest messaging app in the world
Secret messages and advanced cryptography pose a challenge to WhatsApp
When WhatsApp went down for four hours this weekend, nearly 5 million people signed up for messaging service Telegram. The app skyrocketed to the top of the App Store charts, and is now the top free app in 46 countries from Germany to Ecuador. In the US and several other countries, the app is no. 1 in the social networking category, ahead of Facebook, WhatsApp, Kik, and others.
It’s not immediately clear why Telegram emerged as the alternative of choice following WhatsApp’s downtime. Users could have switched to Kik, or Facebook Messenger, or LINE — all of which have hundreds of millions of users. There’s seemingly something different about Telegram. Its rise isn’t only due to WhatsApp’s acquisition and subsequent downtime. “We have been the no. 1 app in Spanish, Arabic, and several Latin American app stores for several weeks before the Facebook deal happened,” says Telegram’s Markus Ra. “The growth was there — so the WhatsApp acquisition and problems merely multiplied the effect across all affected countries.” According to app analytics site App Annie, Telegram started truly gaining steam on February 17th, days before the WhatsApp news even hit.
Built by the pioneering Durov brothers behind Russia’s largest social network, VKontakte (also known as VK), Telegram is a messaging service combining the speed of WhatsApp with Snapchat’s ephemerality and advanced new security measures. WhatsApp might have heralded the first time we heard of Telegram, but it certainly won’t be the last.
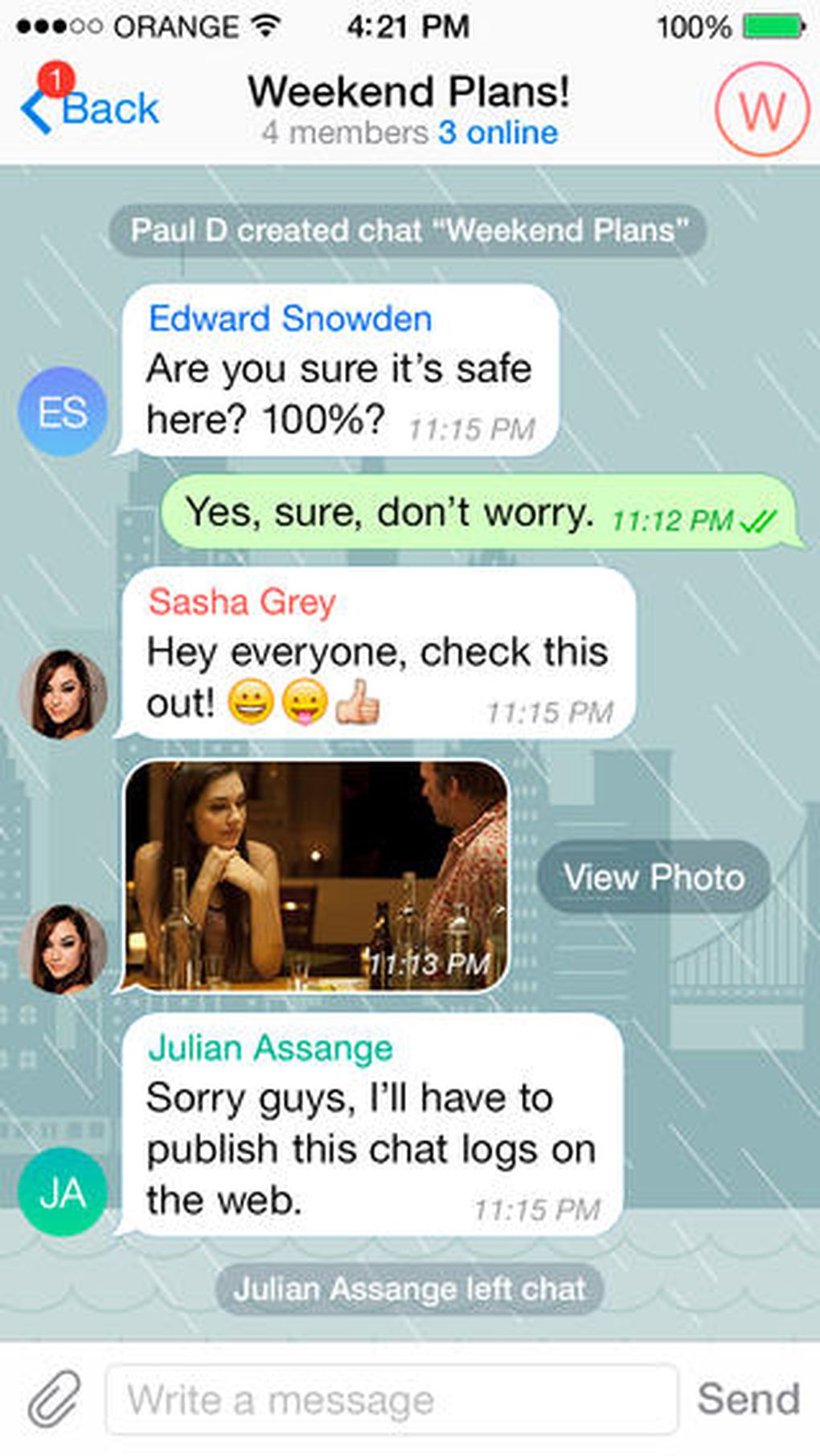
Telegram Messenger for iPhone screenshots
Telegram feels in many ways like a straight-up clone of WhatsApp, from its green double-checkmark read receipts to its cartoonish wallpapers. There’s also the usual gamut of messaging app features including the ability to see a friend’s online status and attach photos, videos, your location, contacts, and documents to messages. But where it lacks originality, Telegram makes up for it in speed and security features. “Telegram is the fastest and most secure mass market messaging system in the world,” the company claims, which it attributes in part to Nikolai Durov’s open-sourced MTProto protocol. Telegram was in fact built as a testing bed for MTProto, Reuters reported when the app launched back in August. The company is so confident in the security of MTProto that it’s offering $200,000 to anyone who can crack it. It’s not unusual for companies to offer bug bounties, but bounties of this size are generally only reserved for critical bugs in widely used apps like Windows.
“The no. 1 reason for me to support and help launch Telegram was to build a means of communication that can’t be accessed by the Russian security agencies,” Durov told TechCrunch. Durov built in a feature that lets you start a “Secret Chat” with any of your friends. According to Telegram, Secret Chats offer end-to-end encryption, leave no trace on the company’s servers, and let you set Snapchat-esque self-destruct timers on messages that range from two seconds to one week. There’s also the ability to check the security of your Secret Chats using an image that serves as an encryption key. By comparing your encryption key to a friend’s, you can effectively verify that your conversation is secure and less vulnerable to man-in-the-middle attacks, the company says. But despite Telegram’s alleged sophistication, no cryptographic method is infallible. The company has, in fact, already doled out $100,000 to one developer for finding a critical bug, TechCrunch reports.
“The no. 1 reason for me to [help launch] Telegram was to build a means of communication that can’t be accessed by the Russian security agencies.”
Telegram is interesting not just because of its stringent security standards, but also because it allows any developer to build a Telegram client of their own, and even for desktop computers. Most new messaging services today, including WhatsApp, build one-size-fits-all messaging apps and lock out third-party developers. It’s hard to blame them, since maintaining one federated language and security paradigm across dozens of apps is difficult. Also, making money off of a platform takes more thought than making money off a simple paid app. Yet, the Durovs’ VKontakte found a lot of success letting developers build alternate versions of its site. More importantly, Telegram operates as a non-profit organization, and doesn’t plan to charge for its services.
“Telegram is not intended to bring revenue, it will never sell ads or accept outside investment. It also cannot be sold,” the company writes in its FAQ. “We’re not building a ‘user base,’ we are building a messenger for the people.” If Telegram ever “runs out” of the money supplied by the Durov brothers, the company says, it will ask for donations from its users. Telegram’s noble goals echo the sentiments of many bright-eyed startup founders, but with the Durovs’ pocketbook in hand and the service’s open API available to third-party developers, it may actually have a chance at fulfilling its goals. Telegram isn’t a CryptoCat for the masses, considering it uses your phone number, of all things, as an identifier — but it’s an important step towards finding a highly encrypted messaging platform that’s accessible to anyone.
“Telegram is not intended to bring revenue, it will never sell ads.”
Championing an ostensibly noble goal, free services, and the experience of VKontakte’s creators, Telegram would seem like a great alternative to any of the leading messages apps out there. After WhatsApp’s acquisition news and downtime, the app is spiking at the right time. The company incentivized several million new users into switching over, but keeping those users will be a continuous challenge. “The switching cost for users on a phone number-based messaging services is at or near zero,” argues Union Square Ventures partner Albert Wenger in a blog post, but that’s only half the story. A network is only as strong as the number of friends you have using it, and convincing all of your friends to switch is no easy task. If Facebook thought that WhatsApp users were liable to switch at a moment’s notice, it wouldn’t have paid $19 billion for the company.
Facebook paid for WhatsApp’s user base, but also for its brand — a brand that spent years solving a very important problem: that it costs a fortune to text across borders. Perhaps the next messaging problem to solve is personal security, considering WhatsApp’s alleged cryptographic weaknesses and the NSA’s data collection policies. WhatsApp became synonymous with texting. Perhaps for Telegram to succeed, it will need to become synonymous with security.

