Late Monday evening, the State Department released a large volume of Hillary emails and it will take a long time to review all of them.
In case you need a sampling of her communications with various people, I am pleased to share a handful. If Hillary is this needy and inept, how can she be president?
Hillary has a cook, needs skim milk and cant figure out the TV guide, she needs Visiting Angels:

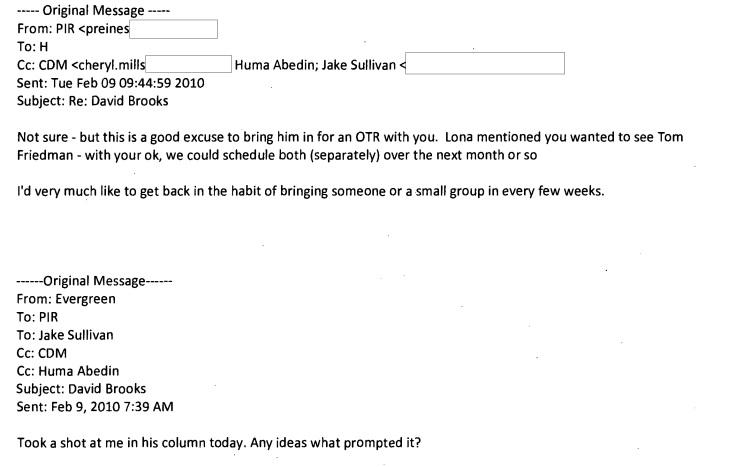
Evergreen, Secret Service codename:
Worried about server security:

Benghazi, note the date, so no video to blame:

Then, just how anti-Semitic is Hillary and her inner circle:
Hilary and her team are fans of Max Blumenthal, Peter Beinart, J-Street
Hilary was thrilled with Max Blumenthal’s book “Republican Gomorrah,” writing on September 11, 2009, “I just finished the book and it is great!.”
Blumenthal’s father, Sidney, often shared Max’s articles with Hilary, including “The Great Islamophobic Crusade” where Blumenthal began his career of conflating all evils of the world to Jews and Zionists, blaming them for anti-Islamic initiatives and then moving on to pretend that all Jews in Israel support murdering Arabs for no reason. Hilary asked her staff to “Pls print for me.”
Sid also recommended to her Peter Beinart’s article, “The Failure of the American Jewish Establishment,” saying
H: I’m sure you are preoccupied with the adventures of Lula, et al. Nonetheless, the article below, just posted by the NY
Review, soon to be published, is a breakthrough piece that will have a large impact. It’s worth reading, not least for Frank
Luntz’s poll numbers. The hysterical tone of much of the Israeli leadership and US Jewish community is partly rooted in
this long-term and profound development. Sid
Sid also pushed hard the idea that American Jews are against the Israeli government, as another Sid Blumenthal memo says:
March 23, 2010
For: Hillary
From: Sid
Re: US Jewish and Israeli public opinion
Three new polls released: from AVO07 (all US), J Street (US Jews), and Ha’aretz (Israelis). I’ve
sent Lauren the whole J Street poll to print out for you; its internals are the most detailed,
relevant and suggestive. My reading of that poll is that the administration is in a pretty good spot
with US Jewish opinion and that the drag (about 10 points, I think) has less to do with the Middle
East and Israel than with the economy. Jewish opinion is far more solidly supportive of the
administration generally than the general population (except minorities). Those adamantly
opposed to the administration stance on Israel are preconceived to be against; they are
predictable, a minority of the US Jewish community and have reached their natural limits. The
institutional US Jewish position backing Bibi and against the administration does not have
majority support among Jews.
Sid also recommended that Hilary tell AIPAC that they are too right wing:
For: Hillary
From: Sid
Re: AIPAC speech
This memo does not address specific policy initiatives.
What I’ve written are options. Use what you like, or none at all. Here are some ideas:1. Hold Bibi’s feet to the fire, remind everyone he was at Wye, his key participant event in
the peace process, and that it was successful.2. Reassure all players of our commitment to the process and the solution (whatever the
language is).3. Perhaps most controversial, I would argue something you should do is that, while
praising AIPAC, remind it in as subtle but also direct a way as you can that it does not
have a monopoly over American Jewish opinion. Bibi is stage managing US Jewish
organizations (and neocons, and the religious right, and whomever else he can muster)
against the administration. AIPAC itself has become an organ of the Israeli right,
specifically Likud. By acknowledging J Street you give them legitimacy, credibility and
create room within the American Jewish community for debate supportive of the
administration’s pursuit of the peace process. Just by mentioning J Street in passing,
AIPAC becomes a point on the spectrum, not the controller of the spectrum. I suggest a
way how to do this below.1. On US national security interest, Israel’s security and the peace process:
The reason the US has always supported Israel since the moment President Harry S. Truman
decided to recognize the State of Israel is that it is in the US national security interest and
consistent with our values. It is in our interest to support a thriving democracy in the Middle East
Only through the marketplace of ideas will sound policies to help resolve complicated and
seemingly intransigent problems be developed. This administration values everybody’s views.
They are important. You are important. We welcome views across the spectrum, from AIPAC to
J Street. All these views are legitimate and must be heard and considered.
There’s also a Martin Indyk email forwarded to Hilary that blames Bibi for not extending his 2010 settlement freeze, without a negative word about Mahmoud Abbas for refusing to negotiate:
From: Martin Indyk [mailto
Sent: Thursday, September 30, 2010 8:59 AM
To: George Mitchell; Feltman, Jeffrey D
Subject: Dealing with Netanyahu
The principle conclusion from a quick visit to Israel and Ramallah over the weekend is that Netanyahu is in a strong
position politically, with an unusually stable ruling coalition. Nobody I spoke with believed that the government would
have fallen if he had decided to extend the settlement freeze before its expiry, as a gesture to U.S. peacemaking efforts.
In their view, he could have easily garnered the support of a large majority of the people, for whom the settlers are a
marginal concern. And this would have given him leverage over his ministers to ensure their support or abstention in
the cabinet. ..3. As his friend, paint a realistic picture of the strategic consequences of his negotiating tactics, particularly in terms of
what is likely to happen to the PA leadership if he worries only about his politics and not at all about Abu Mazen’s
politics.
4. If all else fails, avoid recriminations in favor of a “clarifying moment.” The world will of course blame Bibi. But you
should avoid any kind of finger-pointing in favor of a repeated commitment to a negotiated solution and a willingness to
engage with both sides in trying to make that happen, when they’re ready. The Israeli public and the American Jewish
Community should know how far the President was prepared to go and they should be allowed to draw their own
conclusions
Based on the relatively narrow timeframe of last night’s email dump the overall tone is that Israel is obstinate and not interested in peace, the Zionist American Jewish community must be marginalized, the Palestinians are victims and not responsible for any of their actions, and that Hilary must still publicly cultivate the AIPAC crowd while working behind the scenes to undermine it. Haaretz is liberally quoted but no conservative analysis about Israel ever reached Hilary’s eyes through her handpicked, trusted advisers.
(h/t Babylonian Hebrew)




