EXCLUSIVE: Kerry, Heinz Family Have Millions Invested In Offshore Tax Havens
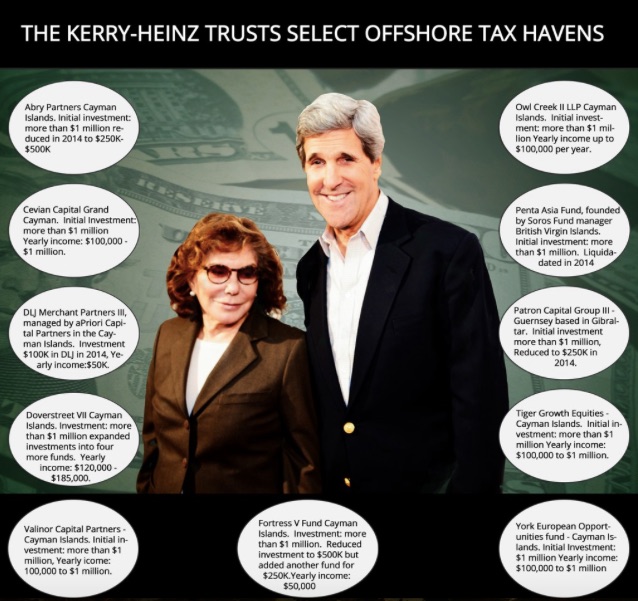
Pollock/DailyCaller: Secretary of State John Kerry and his wife Teresa Heinz have invested millions of U.S. dollars through family trusts in at least 11 offshore tax havens, according to The Daily Caller News Foundation’s Investigative Group.
The revelation comes on the heels of the release of the Panama Papers, a treasure trove of 11.5 million legal and financial records documenting how some of the world’s richest and most powerful people have used offshore bank accounts to conceal their wealth and avoid taxes.
Since the release of the papers, no American politician has been identified as using the secretive offshore accounts.
But a DCNF investigation has confirmed that the former Massachusetts Democratic senator and his billionaire wife, using an elaborate set of Heinz family trusts, have invested “more than $1 million” each into 11 separate offshore accounts — mainly hedge funds in the Cayman Islands.
The investments were made during both Kerry’s tenure in the Senate and in his present position as the nation’s chief diplomat.
The trusts funneled millions of dollars over the years into various offshore investment vehicles through a Heinz trust called the “Heinz Family Commingled Alternative Investment Fund.”
Two other trusts appear to have been set up by the Heinz family since Kerry was appointed by President Barack Obama in 2013 to succeed Hillary Clinton as secretary of state. One is called “HFI Intermediate Fund II” and other the “HFI Dividend Investments.” HFI stands for the Heinz Family Investments.
Another Heinz trust, called “HP Imperial,” invests in companies throughout Asia, including state-run companies within the People’s Republic of China. It is an interesting decision by the Heinz family, given Kerry’s present duties.
When Kerry joined the Obama administration in February 2013, he was considered the second wealthiest member of the Senate, with personal assets totaling nearly $200 million.
Teresa Heinz inherited hundreds of millions of dollars when her former husband, Republican Sen. John Heinz of Pennsylvania, died in 1991 in an airplane crash. Forbes estimates Heinz’s net worth today is $1 billion.
Even after his ascension as secretary of state, the Heinz family continues to make sizable investments in tax havens, a fact that doesn’t sit well with some who would normally be supportive of Kerry.
“Well I say it doesn’t look good by any means,” said Susan Harley, deputy director of Congress Watch, a progressive lobby organization founded by Ralph Nader.
“There’s always a question of whether it’s tax avoidance or tax evasion,” she told TheDCNF. “We would expect our government servants to uphold the law. Those folks need to be held to the same standards as everyone else.”
Obama recently lashed out at U.S. citizens who use tax havens.
On April 5, a few days after the Panama Papers were released, the president said the rich “have enough lawyers and enough accountants to wiggle out of responsibilities that ordinary citizens are having to abide by.” He said they were “gaming the system.”
Harley said the president might not be pleased with some of his cabinet members investing in tax havens: “Given what the president has said, it doesn’t sound like he would be in favor of that kind of behavior as far as people in his cabinet.”
For its part, State Department Spokesman Adm. John Kirby told TheDCNF Kerry is not a beneficiary of the investments and does not own them.
“Secretary Kerry has no offshore investments. He is not, nor has he ever been a beneficiary of Heinz Family and Marital Trusts and he has no decision-making power over them since they are entirely controlled by independent trustees,” said Kirby.
Heinz is a beneficiary, Kirby said, but he emphasized that the investments “are entirely controlled by independent trustees.” He declined to say who controls the trust and makes investment decisions.
The Kerry/Heinz family investments are so vast that Kerry’s federal financial disclosure form runs 169 pages in length, with about 10 investments per page.
Although Democrats are united in condemning offshore accounts, many Democrats, including Obama, have actually benefited from them.
The Fortress Fund, founded by James Dinan, is a tax shelter that is close to Democrats. The Heinz family invested “more than $1 million” in Fortress V when Kerry was a senator, according to his 2015 financial disclosure form.
Fortress is incorporated in the Cayman Islands, according to the company’s filing with the Securities and Exchange Commission.
In 2006, Fortress first came to public attention when it was disclosed that the hedge fund paid Democratic presidential candidate John Edwards $480,000 for a “part time job.” Edwards had invested $16 million into Fortress.
The New York Times described the Fortress Fund in 2007, saying it was comprised of “thinly regulated pools of often risky investments,” and linked it to the subprime mortgage meltdown of 2008.
Dinan also was a top Obama bundler who raised between $50,000 to $100,000 in 2008, according to OpenSecrets, a nonprofit campaign finance research group.
And Penta Asia Fund, based in the British Virgin Islands, was founded by former George Soros fund manager John Zwaanstra.
According to records from Kerry’s Senate filing and his federal disclosure filing, he and his family appear to have cut back on their offshore investments after he joined the Department of State, but did not eliminate them. In some instances, they actually invested more in various offshore funds.
The Kerry family trust offshore investments are in:
Abry Partners – The company finalized $42 billion in “leveraged transactions” according to its website. Incorporation: Cayman Islands. Kerry family investment was worth “more than $1 million” while he was in the Senate, but was reduced in 2014 to between $250K to $500K.
Cevian Capital – Is an active ownership investment firm that seeks ownership in undervalued public companies. Incorporated: George Town, Grand Cayman. This is the only offshore investment organized by the new Kerry family “HFI Diversified Investment Fund.” While secretary of state, Kerry and family invested “more than $1 million” in the fund. It pays annual dividends, interest and capital gains of $100,000 to $1 million.
DLJ Merchant Partners III — is a Delaware registered company, but as of 2013, it was managed by APriori Capital Partners, a Cayman Island registered firm. Kerry only had $100K in DLJ in 2014, but the family still receives dividends, rentals and royalties, interest and capital gains. Annual income is $50,000.
Dover Street VII – Seeks to buy investments in venture capital or buyouts in the U.S. and U.K. Incorporated: Cayman Islands. The family trust invested more than $1 million while Kerry was in the Senate. As secretary of state, the family expanded investments into four more funds. They get annual dividends, interest, rents royalties, and capital gains totaling $120,000 to $185,000.
Fortress V Fund – Specializes in buyouts and recapitalizations, according to Bloomberg. Incorporation: Cayman Islands. The trust investment: more than $1 million. After Kerry became secretary of state, the family reduced investment to $500,000 for Fortress V but added a new investment in “Fortress V Co-investment Fund” for $250,000. The family receive dividends, rents and royalties, interest and capital gains.
Owl Creek II – A hedge fund. Incorporation: Cayman Islands. Kerry family investment: More than $1 million in Senate filing; reduced to $100,000 from $1 million in 2014. The family receives dividends, rent and royalties, and capital gains up to $100,000 per year.
Penta Asia Fund – An Asia-focused hedge fund founded by Soros Fund manager John Zwaanstra. Registration: British Virgin Islands. The trusts investment began while Kerry was in the Senate with an investment of more than $1 million. It was liquidated in 2014.
Patron Capital Group III – The fund makes “opportunistic and value-oriented investments,” including “liquidity constrained property assets” predominantly in Western Europe. Registered in Guernsey and based in Gibraltar. While Kerry was in the Senate, the family invested more than $1 million, but that was reduced to $250,000 in 2014. They receive dividends, interest, and capital gains, now only $5,000 per year
Tiger Growth Equities – This fund primarily focuses investment in China, Southeast Asia, Latin America and Eastern Europe. Incorporation: Cayman Islands. More than $1 million in Kerry’s Senate filing. Kerry and family have continued their investment during his secretary of state years. They receive annual dividends, interest and capital gains estimated from $100,000 to $1 million.
Valinor Capital Partners – Is a “pooled investment hedge fund.” Incorporated: Cayman Islands. Kerry and family invested more than $1 million, receiving annual income from dividends, interest and capital gains of $100,000 to $1 million.
York European Opportunities fund – a hedge fund, that invests in “restructures, spinoffs, split-ups and proxy contests.” Incorporation: Cayman Islands. Kerry Family Investment: $1 million during the Senate term. Dividends: $100,000 to $1 million annually. Subsidiary York Capital Management’s number one investment is in the HJ Heinz Company.
“HP Imperial,” another Heinz trust invests in Malaysia, Hong Kong, Thailand and South Korea. Its biggest investments are in communist China, including the Alibaba Group; Boer Holdings, a Chinese electrical distribution company in Wuxi, Yixing and Shanghai; Hubao International Holdings, a tobacco company; Labixiaoxin Snacks Group, a Chinese snack food provider; Sands China, with six casinos in Macau; and Tibet 5100 Water Holdings, a Chinese-owned company trying to sell Tibetan premium water like Evian.