It is a matter of law….the democrats and some republicans are providing higher protection for illegals and criminals than they do for just plain ol’ Americans. At least they should be forced to register or something similar like a declaration that they are more loyal to illegals and criminal action than they are to Americas.

Some democrats are posturing to abolish ICE as an agency.
The Democrats mulling a run for the White House in 2020 are facing intense pressure from liberals to campaign on abolishing the agency that enforces federal immigration laws, a proposal that was once relegated to the far-left fringe.
In protesting the Trump administration’s policies toward illegal immigration, liberal commentators and writers have been embracing the idea of gutting the U.S. Immigration and Customs Enforcement agency, which identifies, arrests and deports illegal immigrants inside the United States.
“This is a growing position on the left, and I imagine 2020 Democratic presidential aspirants will have to grapple with it,” liberal writer and MSNBC host Chris Hayes tweeted.
We have seen California become a sanctuary state and now Illinois is too. We have seen mayors refuse to cooperate with ICE supported by their governors. Can states refuse to cooperate with ICE or how about other Federal agencies like ATF or DEA?
As long as these politicians provide legal cover and sanctuary for foreign criminals they should all be registered as ‘foreign agents’ under the FARA.
The Foreign Agents Registration Act (FARA) was enacted in 1938. FARA is a disclosure statute that requires persons acting as agents of foreign principals in a political or quasi-political capacity to make periodic public disclosure of their relationship with the foreign principal, as well as activities, receipts and disbursements in support of those activities. Disclosure of the required information facilitates evaluation by the government and the American people of the statements and activities of such persons in light of their function as foreign agents. The FARA Registration Unit of the Counterintelligence and Export Control Section (CES) in the National Security Division (NSD) is responsible for the administration and enforcement of the Act.
We have a missing illegal criminal from Denver that is part of a case of vehicular homicide….Denver law enforcement let him go under bail even though ICE had a detainer on him….he cannot be found.
Meanwhile, let us look at Illinois shall we?
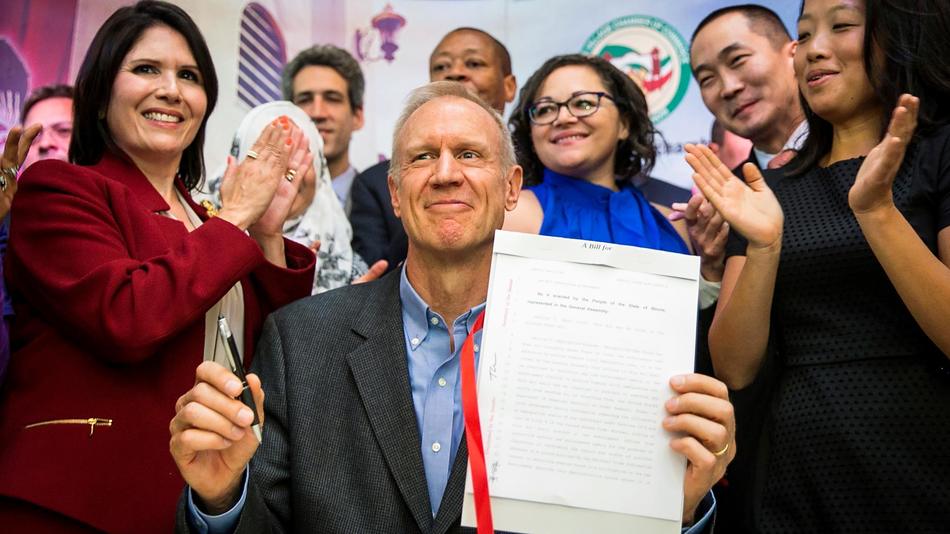 Illinois Gov. Bruce Rauner smiles while surrounded by law enforcement officials and immigrant rights activists in Chicago’s Little Village neighborhood Monday, Aug. 28, 2017, after signing legislation that will limit how local and state police can cooperate with federal immigration authorities. The narrow measure prohibits police from searching, arresting or detaining someone solely because of immigration status, or because of so-called federal immigration detainers. AP (Ashlee Rezin /)
Illinois Gov. Bruce Rauner smiles while surrounded by law enforcement officials and immigrant rights activists in Chicago’s Little Village neighborhood Monday, Aug. 28, 2017, after signing legislation that will limit how local and state police can cooperate with federal immigration authorities. The narrow measure prohibits police from searching, arresting or detaining someone solely because of immigration status, or because of so-called federal immigration detainers. AP (Ashlee Rezin /)
With mariachis performing in the background, Governor Bruce Rauner signed the TRUST Act on Monday, at a Mexican restaurant in Chicago’s Little Village neighborhood, officially barring cooperation between Illinois police departments and immigration officials.
The TRUST Act, valid in all cases except where a federal judge has issued a warrant for arrest, will make Illinois more welcoming to immigrants and refugees, according to its supporters.
The law denies local law enforcement the ability to detain people on behalf of Immigration and Customs Enforcement (ICE), the federal agency charged with identifying and investigating immigrants present in the country illegally. It also prohibits local officials from inquiring about a person’s immigration status, something Ruiz-Velasco called a “very important protection,” that will make immigrants more comfortable reporting crimes to local police.
“The TRUST Act will ensure that those who live in this state of limbo [as concerns immigration status] can have one certainty: When their lives and their families are in danger, they can turn to the police without their world being taken away from them,” said Serafina Ha, of the Korean immigrant services agency, the Hana Center.
Support for the law came from Illinois law enforcement functionaries, as well as over 170 faith leaders, and over 170 Illinois employers. The Campaign for a Welcoming Illinois, in support of the bill, engaged over 84 organizations and 14,000 people in the state, according to ICIRR.
However some political leaders, including many downstate Republicans, voiced opposition.
“We are a country founded by immigrants, but those were legal immigrants, and I think the last thing Illinois wants is to see a sanctuary state, and this moves us in that direction,” state Sen. Kyle McCarter, a Republican from Lebanon, Ill., told the Chicago Tribune.
Just five Republicans voted for the law in the Illinois Senate, and only one Republican voted for it in the House.
Passing with mainly Democratic support on May 5, 2017, the law had since sat on Governor Rauner’s desk as supporters organized through letters, press conferences and rallies.
“This will provide an unprecedented level of protection for Illinois’ half-million undocumented residents, who could otherwise enter the deportation pipeline through any simple interaction with police including a traffic violation,” ICIRR said in a statement. “Illinois is now the gold standard for statewide protections against deportation.”