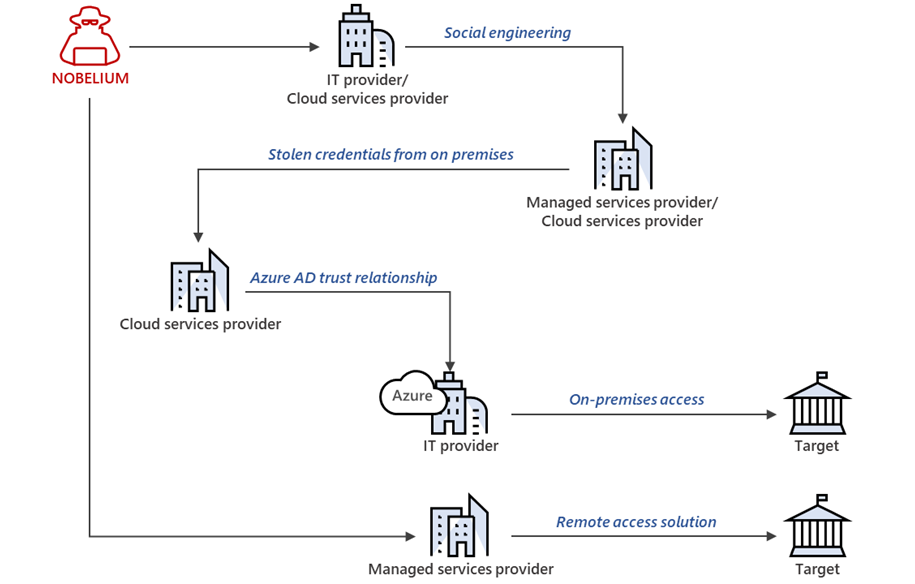
First there was a full-throated denial by Adm. Kirby from the White House Press Room that the story the Wall Street Journal reported was true. Then a couple of days later, Adm. Kirby walked it back and attempted in national security platitudes to explain why he initially denied the story. Then the White House decided to blame the Trump administration stating that China has had a base in Cuba since 2019. If that was true, then why would the Biden administration lift some sanctions on Cuba?
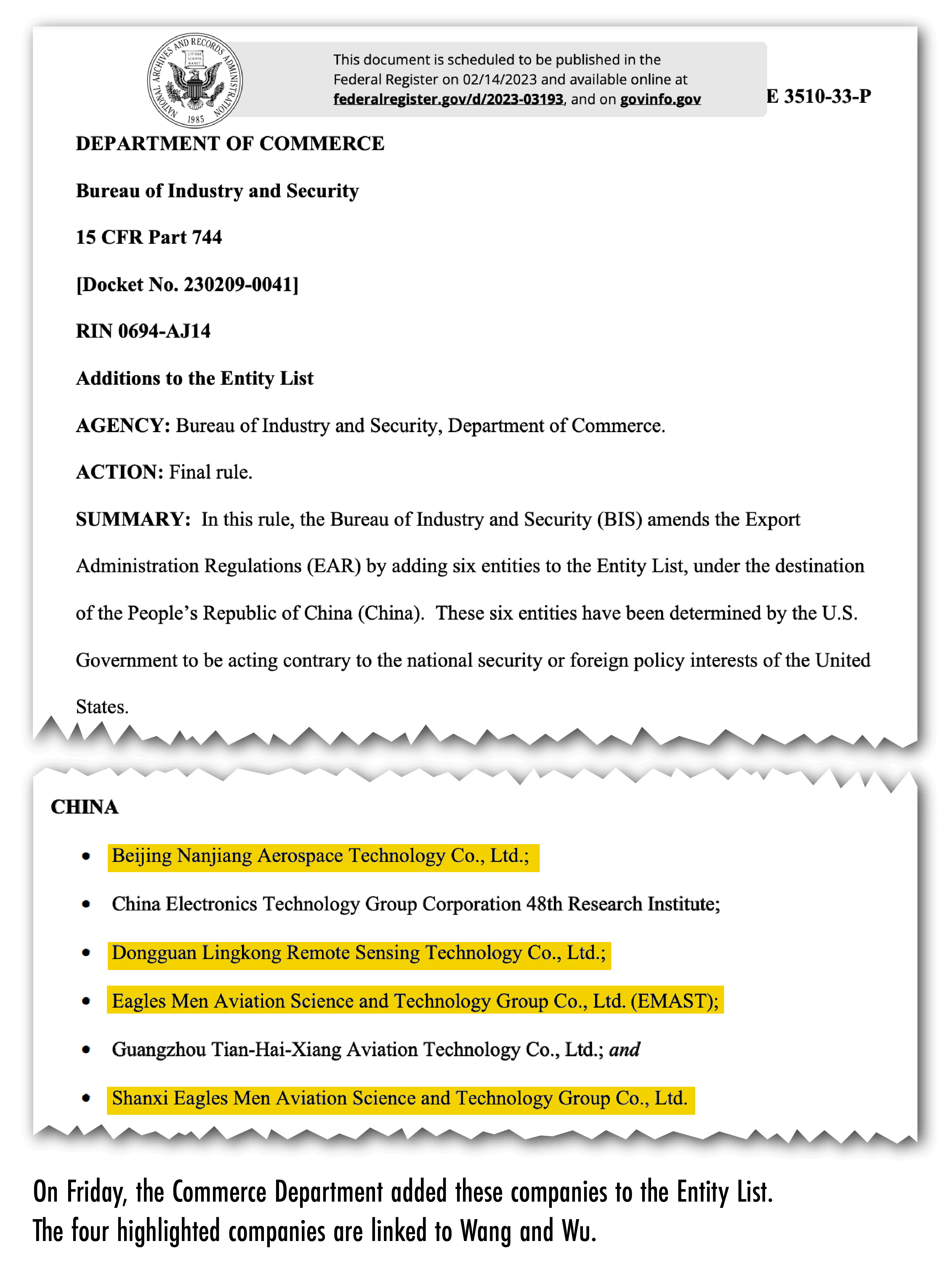
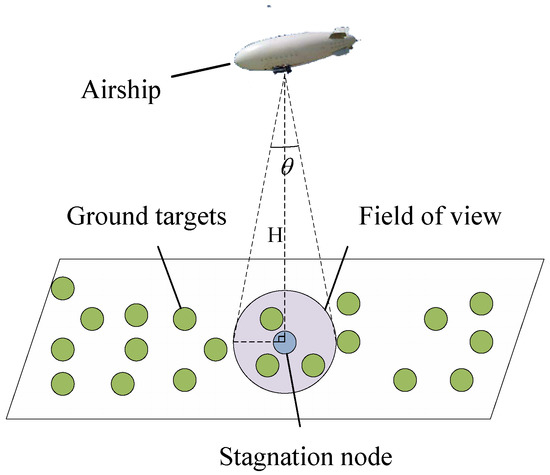
Well….no , under the Trump administration, that is not accurate either. Perhaps China only has had radar surveillance installation since 2018. but you can bet that since Russia has had a spy base in Cuba known as the Lourdes signals intelligence facility, they are not only collaborating but perhaps co-locating especially since Beijing and Moscow have nurtured a a friendly business relationship without limitations. However, no one is putting China and Cambodia in the conversation…that is right, China has a secret base there too, called the Ream Base.  .Satellite imagery of Ream Naval Base from 5 February 2023, annotated to show the shape of the pier extension. Original image courtesy of BlackSky
.Satellite imagery of Ream Naval Base from 5 February 2023, annotated to show the shape of the pier extension. Original image courtesy of BlackSky
Lourdes
Beyond the Wall Street Journal doing great work, then comes the Miami Herald with more.
The CIA and Office of the Director of National Intelligence declined to comment. The Cuban government also pushed back against the initial WSJ report calling it “totally false and unfounded information” in a statement made by the Vice-minister of Foreign Affairs, Carlos Fernández de Cossío.
Regardless of Cuba’s sovereign rights in defense matters, the official said, Cuba rejects “any foreign military presence in Latin America and the Caribbean, including that of numerous United States military bases and troops, especially the military base that illegally occupies a portion of the national territory in the province of Guantánamo.” While China might be already collecting intelligence on the U.S. from its commercial facilities in the region, having a signals-intelligence facility “adds to China’s capabilities, especially in times of war,” said Evan Ellis, professor at the U.S. Army War College Strategic Studies Institute, which monitors China’s relationship with Latin America and the Caribbean. “I think it telegraphs Chinese willingness in the current difficult environment between our two countries to take some of these bolder steps and their sense, with their growing military power and economic power and the perception of the U.S. democratic disarray, that they can take these steps that maybe a decade ago, they would not have risked,” Ellis said. “It’s not that big of a threshold that they’ve crossed, but it is significant,” he added.
The news follows intense speculation that Russia, not China, was planning to reopen its Soviet-era espionage base in Lourdes, a town near Havana, which it shut down in 2002. High-ranking Russian national security officials and diplomats have been traveling to the island recently and the two governments appear as close as ever, with Cuban leaders offering public support for Russia’s invasion of Ukraine. But when publicly asked about reopening the Lourdes base during his trip to Havana in April, Russian Foreign Minister Sergei Lavrov did not directly address the question. And despite several economic agreements recently announced by Russian and Cuban authorities, including land-lease deals, the news about a Chinese spy base speaks to the realities on the ground: The island is desperate for cash as its economy continues sinking. Russia had limited resources even before embarking on a war against Ukraine — and China can pay. On May 20, Cuba’s Interior Minister, Gen. Lázaro Alberto Álvarez Casas, met with China’s Minister of Public Security, Wang Xiaohong. “China stands ready to work with Cuba to implement the important consensus reached by the leaders of the two countries and deepen pragmatic cooperation in various fields, especially in law enforcement and security,” a Chinese government statement said.
The news about the spy base comes as the Biden administration has been taking steps to improve its strained relationship with China, which is considered the United States’ primary military and economic rival. At the same time, State Department officials and members of Congress have been raising concerns about China’s increased influence in Latin America and the Caribbean. China has become South America’s largest trading partner and has exploited the Biden administration’s reluctance to new trade deals and has inked a free trade agreement with Ecuador, while Uruguay and Panama are in line, U.S. Rep Maria Elvira Salazar, a Miami Republican, said during a congressional hearing she chaired on Wednesday. “That is very troublesome,” Salazar said, blaming the Biden administration for ignoring the pleas of allies in the region with conservative governments “to the benefit of our enemies.”
When asked by representative Warren Davidson, R-Ohio, why the United States has seemed to become “more passive” and allowed China to increase its influence in the Western Hemisphere, the State Department’s top diplomat for the region acknowledged the administration needs to act with a sense of urgency. “This is the most challenging moment I have seen in 30 years in our hemisphere, and we have to do everything that we can to help our neighbors and our partners around the region to succeed and resist these strategic competitors from outside,” Assistant Secretary for Western Hemisphere affairs Brian Nichols said. The China deal also complicates U.S. policy towards Cuba.
The administration has lifted some restrictions on flights and remittances, resumed the family reunification program for Cubans and reestablished migration and law enforcement talks with the Cuban government. But it stopped short of easing other embargo restrictions and removing Cuba from the list of countries that sponsor terrorism, which the Cuban government had made a condition to improving relations. The cozying up to Russia and China indicates the Cuban government has chosen to seek further support from its longtime political and ideological allies rather than pursuing normalization of relations with the U.S. at a time Cuban authorities perceive their grip on power is at risk. Cuba is facing its worst economic crisis in decades and serious political challenges from a population that has taken to the streets to protest and demand regime change. Ebrahim Raeisi, the president of Iran, another major U.S. adversary, is set to travel to the island after visiting Venezuela and Nicaragua next week. The strategy suggests something else: The Cuban military is calling the shots on the island, not the civilian team led by Cuba’s handpicked president, Miguel Díaz-Canel. If true, the deal with China shows “Cuba’s desperation. It’s the same thing with Russian investors. Cuba is looking for cash where it can get it,” Ellis said. “Cuba also understands the limits of the Biden administration.
With the Republicans in control of the House in Washington, with Biden being more conservative, with a sense of lessons learned that the Obama opening was seen as ‘we gave up too much and receive too little from Cuba,’ there’s an understanding in Cuba that they’re not going to get much more out of Washington.” Latin America’s sharp turn to the left and the consolidation of power by Nicolás Maduro in Venezuela also gives Cuba confidence to do bolder things, Ellis said, while noticing that island has not gone that far as to sign military agreements with Russia or receive Russian weapons. Florida Republicans in Congress quickly reacted to the report on the China espionage base deal to highlight what they said is an increasing national security threat coming from Cuba. “The threat to America from Cuba isn’t just real, it is far worse than this,” Sen. Marco Rubio tweeted. “But to date, not only does the Biden White House not care, they have people who actually want to appease the regime.” “The Cuban regime is auctioning off land to the Russians, hosting the Iranians, and letting the Chinese open a base to spy on the U.S.,” Salazar tweeted. “Just 90 miles from our coast, the dictatorship has opened the door to our greatest enemies!” Later on Thursday, Rubio, who is the Vice Chairman of the Select Committee on Intelligence and the committee’s chairman, Mark R. Warner (D-VA), issued a statement urging the Biden administration “to take steps to prevent this serious threat to our national security and sovereignty.” “We must be clear that it would be unacceptable for China to establish an intelligence facility within 100 miles of Florida and the United States, in an area also populated with key military installations and extensive maritime traffic,” they said.
Read more at: https://www.miamiherald.com/news/nation-world/world/americas/cuba/article276215936.html#storylink=cpy





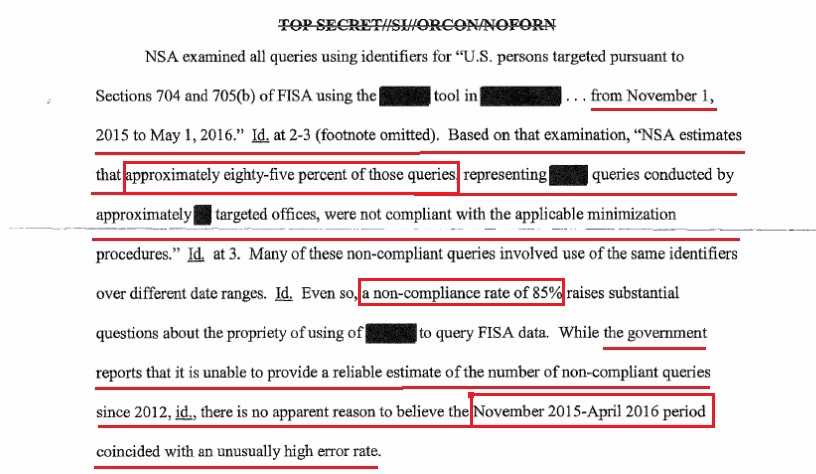
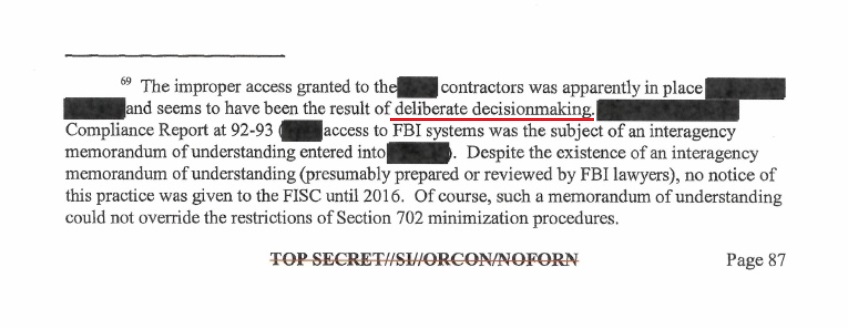 This specific footnote is a key. Note the phrase: “([redacted] access to FBI systems was the subject of an interagency memorandum of understanding entered into [redacted])”, this sentence has the potential to expose an internal decision; withheld from congress and the FISA court by the Obama administration; that outlines a process for access and distribution of surveillance data.
This specific footnote is a key. Note the phrase: “([redacted] access to FBI systems was the subject of an interagency memorandum of understanding entered into [redacted])”, this sentence has the potential to expose an internal decision; withheld from congress and the FISA court by the Obama administration; that outlines a process for access and distribution of surveillance data.